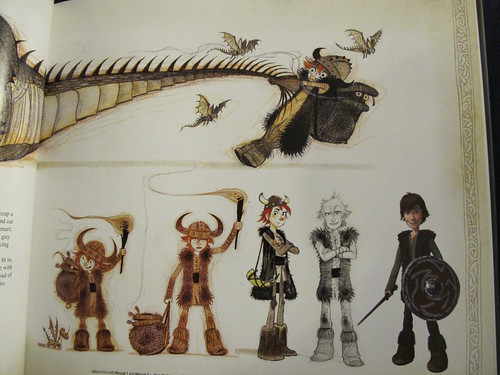
How To Train Your Dragon was a success for Dreamworks, but other films aren’t. Picture by donielle on Flickr.
A selection of 9 links for you. Use them wisely. I’m charlesarthur on Twitter. Observations and links welcome.
Samsung patents home-screen backup and transfer solution » Phandroid
No major smartphone manufacturer has yet to create a solution for copying home screen setups from one device to another. It’s a feature we’ve been hoping to see in Android from Google’s own ingenuity for quite some time, but someone seems to have beaten them to the punch.
Samsung’s latest patent details a software solution that would allow a user to configure a home-screen and copy it to another remote device. The details in the patent are very specific about the process, but an abstract look at the thing reveals a few different possible scenarios…
Umm, “no major smartphone manufacturer”? Apple has had this backup thing called iCloud since 2011 which lets you create a phone that clones your previous layout, apps, settings, everything. Commenters also mention an app called Nova – and say that Lollipop does it anyway.
Sony to cut 1,000 jobs in smartphone business, says Nikkei » Re/code
Sony plans to cut another 1,000 jobs in its smartphone division, mainly in Europe and China, the Nikkei business daily reported.
The cuts are in addition to the 1,000 jobs Sony said it would eliminate in its mobile unit in October, the Nikkei said.
Overall, Sony’s mobile division workforce will shrink by about 30% to 5,000 by the end of the fiscal year ending March 2016, the report said.
Can’t remember when I saw a report of Sony expanding a division. (Maybe the PlayStation division does it quietly.) Of course, contract manufacturing means you don’t need a gigantic dedicated workforce to make a lot of phones. Just the right workforce.
My thesis on Microsoft » Beyond Devices
Jan Dawson:
I see a downward trajectory over time in sales of Windows in total, even accounting for the many different form factors Windows runs on. As such, last quarter’s poor performance in Windows sales is much more indicative of the longer-term trend than short-term headwinds. I see Windows 10 slowing the decline a little, but I actually think the free upgrades could stall or postpone new device purchases for some users, which may be counterproductive in the short term. I don’t see Windows 10 solving any of the fundamental challenges I just outlined.
Software sales to consumers will shrink to zero
To my mind, the other major question about Microsoft’s future is its ability to continue to sell software to consumers for a price. I’ve talked for some time now about the fact that, in Microsoft’s two major software categories (OS and productivity), its two major competitors and essentially every other company now give their software away for free.
Hard to argue with any part of this. The downward pressure on Microsoft is inescapable. Strange that at a time when software is eating the world, the ability to charge for it is vanishing.
Haunted Empire » Asymco
Horace Dediu:
I’ve often said that corporate governance is medieval, or pre-scientific in its approach to understanding causality. That may be too generous. As far as the reward/punishment system (also known as Human Resources) it’s probably pre-neolithic. The luxuries and extravagance which we heap upon the leader provide abundant evidence. Leaders insist on these ironic “pay packages” and boards approve them because they know they can and will be ritualistically sacrificed if and when the mobs turn against them.
A manager would be a fool to accept even generous pay given the risk, actually near certainty, of ritualistic slaughter. They demand and are unquestionably given absurd pay that has no relationship to performance. Such pay has no relationship to performance because it isn’t designed to reward performance but to account for the risk of arbitrary and very public sacrifice. Boards (and hence shareholders) are deliberately hiring a scapegoat for sins as yet unknown. Luxury and violence are thus finely balanced in what is called “Executive Search”.
A finely-judged thumb in the eye for a lot of management speak, and for a book about Apple.. oh, what was the name…
How DreamWorks Animation can claw its way back » The Hollywood Reporter
The maker of Shrek is in financial trouble:
And while the film unit is clearly troubled — four of the last six movies have resulted in write-downs (Rise of the Guardians, Mr. Peabody & Sherman, Turbo and Penguins of Madagascar) — Katzenberg has put new co-presidents (Bonnie Arnold and Mireille Soria) in charge of filmmaking and is making good on his 2013 promise to diversify “from an animated feature film company into a multifaceted, branded-entertainment company.” For its most recent quarter, DWA reported a $46.4m loss, but its television segment showed a $2.3m profit and consumer products posted a $4.2m profit.
There also are signs that its digital acquisition AwesomenessTV is profitable (DWA reported a $1.2m profit attributed to “other items,” which consists largely of Awesomeness). DWA paid $33m for Awesomeness in 2013 with a potential earn-out of another $115m. Instead, DWA settled the earn-out last year for $80m then sold 25% of Awesomeness to Hearst Corp. for $81.3m. The net result is that DWA paid about $33m for a 75% stake in a fast-growing, potentially highly profitable digital asset that has a perceived value of more than $300m.
But by focusing on expansion and diversification, Katzenberg acknowledges he might have been distracted from job No. 1: making profitable movies.
Contrast with Pixar, bought by Disney and still turning out successful films – yet always focussing on the story, and not just churning them out. Pixar, of course, was made successful by Steve Jobs. And it retains its focus.
The Apple Watch: The next big thing or living on borrowed time? » Harvard Business School
From September 2014:
Q Do you think the Apple Watch will fundamentally change our lives in a similar way the iPhone and iPad did?
Ryan Raffaelli, Harvard Business School assistant professor: We often define radical innovations as “competency- destroying,” meaning that they render all related products and services in the same market category obsolete. While the Apple Watch is certainly the most advanced smartwatch on the market today, I’m not sure it fits the traditional definition of a “radical” innovation. For instance, it is unlikely the Apple Watch will have the same transformative effect on society as other life-changing innovations throughout history – think about the steamship’s impact on the sailing industry, how the personal computer ended the use of typewriters, or how electronic fuel injection systems replaced carburettors.
The news that the Apple Watch isn’t as radical as the steamship or fuel injection will, surely, persuade Jony Ive once and for all that it’s time to give it up and head off into the sunset.
BlackPwn: BlackPhone SilentText type confusion vulnerability » Azimuth Security
In the phone market, one of the premier products to be released in recent years is undoubtedly the BlackPhone (http://www.blackphone.ch), which has been cited numerous times in tech publications as being one of the best available defences against mass surveillance, as it provides full end-to-end encryption facilities for voice calls and text/MMS messaging.
While exploring my recently purchased BlackPhone, I discovered that the messaging application contains a serious memory corruption vulnerability that can be triggered remotely by an attacker. If exploited successfully, this flaw could be used to gain remote arbitrary code execution on the target’s handset. The code run by the attacker will have the privileges of the messaging application, which is a standard Android application with some additional privileges. Specifically, it is possible to:
• decrypt messages / commandeer SilentCircle account
• gather location information
• read contacts
• write to external storage
• run additional code of the attacker’s choosing (such as a privilege escalation exploit aimed at gaining root or kernel-mode access, thus taking complete control of the phone)
How surprising that people would believe a claim made by a company about having excellent security.
The secret Douglas Adams RPG people have been playing for 15 years » Kotaku
Fantastic tale from Lewis Packwood:
Yoz [Grahame] then quickly forgot all about the employee forum, but six months later he happened to take a quick peek. And there were ten thousand posts in there.
Bearing in mind that the forum was buried deep within the website and was (just about) password secured, this was a phenomenal result. But even more fascinatingly, the forum had evolved into an extension of the game itself.
Visitors to the forum had created fictional employees and passengers on the Starship Titanic and begun role playing as them. Someone would make up an implausible, Adams-esque scenario, and everyone else would react to it in character, resulting in some enormously complex storylines and in-jokes that developed and diversified over years. And this strange fictional world had appeared entirely spontaneously, without any input from Douglas Adams or The Digital Village. Indeed, Yoz was as surprised as anyone when he stumbled across it: “It was like ignoring the vegetable drawer of your fridge for a year, then opening it to find a bunch of very grateful sentient tomatoes busily working on their third opera,” he says.
I loved Starship Titanic. Not least because there were two alternative endings, diametrically opposed in their result.
A pirated version of the Assassin’s Creed application for Android is bundled with malware » 0xicf
“Blackpiano”:
The Trojanized variety of the Assassin’s Creed application has the potential to be quite potent, because when a user downloads it, what he or she is actually downloading is malware. The malware in turn downloads a fully functional, pirated version of the actual application. The gaming app works as advertised, so the standard mobile gamer is going to have a tough time realizing that the package they’ve downloaded is malicious…
…The malicious application is capable of sending multi-part text messages, harvesting text messages from a victim’s device, and sending stolen information to a remote Command & Control (C2) server. We were able to locate phone numbers belonging to Russian bank “Volga-Vyatka Bank of Sberbank of Russia” in the malicious application code for which SMS messages are being intercepted to steal sensitive information.
Sneaky.
