
Don’t just sit there, look at the geotargeted ads on your phone. Photo by adm on Flickr.
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
A selection of 10 links for you. Deja vu again? I’m @charlesarthur on Twitter. Observations and links welcome.
AI winter is well on its way • Piekniewski’s blog
Filip Piekniewski is sceptical on the AI/ML front:
»
One of the key slogans repeated about deep learning is that it scales almost effortlessly. We had the AlexNet in 2012 which had ~60M parameters, we probably now have models with at least 1000x that number right? Well probably we do, the question however is – are these things 1000x as capable? Or even 100x as capable? A study by openAI comes in handy:
So in terms of applications for vision we see that VGG and Resnets saturated somewhat around one order of magnitude of compute resources applied (in terms of number of parameters it is actually less). Xception is a variation of google inception architecture and actually only slightly outperforms inception on ImageNet, arguably actually slightly outperforms everyone else, because essentially AlexNet solved ImageNet. So at 100 times more compute than AlexNet we pretty much saturated architectures in terms of vision, or image classification to be precise. Neural machine translation is a big effort by all the big web search players and no wonder it takes all the compute it can take (and yet google translate still sucks, though has gotten arguably better). The latest three points on that graph, interestingly show reinforcement learning related projects, applied to games by Deepmind and OpenAI. Particularly AlphaGo Zero and slightly more general AlphaZero take ridiculous amount of compute, but are not applicable in the real world applications because much of that compute is needed to simulate and generate the data these data hungry models need. OK, so we can now train AlexNet in minutes rather than days, but can we train a 1000x bigger AlexNet in days and get qualitatively better results? Apparently not…
«
I’m not sure I agree with him on all of this, but refuting it isn’t trivial. The point is, Google/DeepMind tends to go a long time in submarine mode, then pop up with something big. Just because you can’t see the submarine doesn’t mean it isn’t making progress – perhaps a lot.
link to this extract
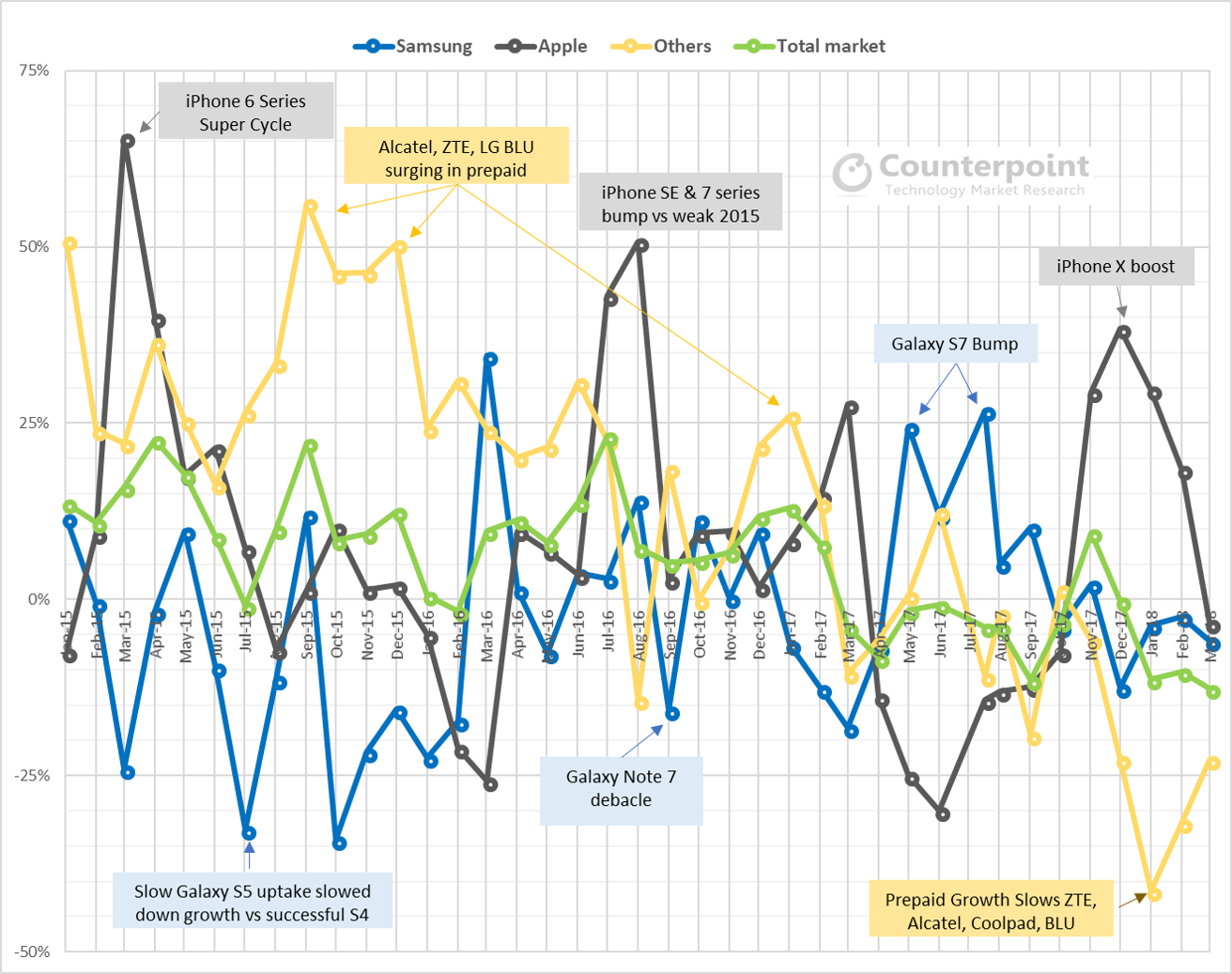
Worldwide smartphone volumes will remain down in 2018 before returning to growth in 2019 • IDC
»
After declining 0.3% in 2017, the worldwide smartphone market is expected to contract again in 2018 before returning to growth in 2019 and beyond. According to the International Data Corporation (IDC) Worldwide Quarterly Mobile Phone Tracker, smartphone shipments are forecast to drop 0.2% in 2018 to 1.462bn units, which is down from 1.465bn in 2017 and 1.469bn in 2016. Looking further out, IDC expects the market is to grow roughly 3% annually from 2019 onwards with worldwide shipment volume reaching 1.654bn in 2022 and a five year compound annual growth rate (CAGR) of 2.5%.
The biggest driver of the 2017 downturn was China, which saw its smartphone market decline 4.9% year over year. Tough times are expected to continue in 2018 as IDC forecasts consumption in China to decline another 7.1% before flattening out in 2019. The biggest upside in Asia/Pacific continues to be India with volumes expected to grow 14% and 16% in 2018 and 2019. Chinese OEMs will continue their strategy of selling large volumes of low-end devices by shifting their focus from China to India. So far most have been able to get around the recently introduced India import tariffs by doing final device assembly at local India manufacturing plants. As for components, almost everything is still being sourced from China.
«
Europe and the US have had their rapid growth; now it’s going to be the slow slide to saturation.
link to this extract
Google spinoff Dandelion uses ground energy to heat, cool homes • CNET
»
Google spinoff Dandelion unveiled on Wednesday a smart heating and air conditioning system that uses energy from the ground to regulate your home’s temperature.
The business, which originated in the semi-secret X research and development lab run by Google parent company Alphabet, was founded last year to sell geothermal energy systems to consumers. Its first commercial product is dubbed Dandelion Air.
Dandelion Air is a geothermal system that moves heat between the house and the ground using plastic pipes and a pump, bringing heat to the building in winter and pushing heat into the ground in summer.
The system is nearly twice as efficient as typical air conditioning systems and four times more efficient than traditional furnaces, the New York-based energy company said.
«
Er, to my eyes this is a completely standard ground source heat pump, and they all have that typical comparative efficiency. They’ve been around for decades. Work like a fridge in reverse. This came out of Google X? What next, a film camera?
link to this extract
How futures trading changed bitcoin prices • Federal Reserve Bank of San Francisco
Galina Hale, Arvind Krishnamurthy, Marianna Kudlyak, and Patrick Shultz:
»
The peak bitcoin price coincided with the day bitcoin futures started trading on the Chicago Mercantile Exchange (CME). In this Economic Letter, we argue that these price dynamics are consistent with the rise and collapse of the home financing market in the 2000s, as explained in Fostel and Geanakoplos (2012). They suggested that the mortgage boom was driven by financial innovations in securitization and groupings of bonds that attracted optimistic investors; the subsequent bust was driven by the creation of instruments that allowed pessimistic investors to bet against the housing market. Similarly, the advent of blockchain introduced a new financial instrument, bitcoin, which optimistic investors bid up, until the launch of bitcoin futures allowed pessimists to enter the market, which contributed to the reversal of the bitcoin price dynamics…
…Given that there is no actual asset that backs the value of bitcoin and it doesn’t provide a natural hedge as insurance against sharp moves in any other asset’s value, what will eventually determine the “fundamental” price of bitcoin is transactional demand relative to supply. We know that bitcoin is used as a means of exchange in a number of markets. The amount of bitcoins needed for these markets to function constitutes transactional demand. The supply growth of bitcoin is becoming more limited as the mining price increases. If transactional demand grows faster than supply, we would expect the price to grow.
«
The “if” in “if transactional demand grows” is doing a lot of heavy lifting – and as they also point out, as these are winner-takes-all markets, if something is able to do the transactional job better than bitcoin, all the value could migrate there. Someone said on a panel on Wednesday that bitcoin will be seen in the future as the Napster of cryptocurrencies. Could be correct.
link to this extract
Lawyers send mobile ads to phones in ER waiting rooms • NPR
»
Patients sitting in emergency rooms, at chiropractors’ offices and at pain clinics in the Philadelphia area may start noticing on their phones the kind of messages typically seen along highway billboards and public transit: personal injury law firms looking for business by casting mobile online ads at patients.
The potentially creepy part? They’re only getting fed the ad because somebody knows they are in an emergency room.
The technology behind the ads, known as geofencing, or placing a digital perimeter around a specific location, has been deployed by retailers for years to offer coupons and special offers to customers as they shop. Bringing it into health care spaces, however, is raising alarm among privacy experts.
“It’s really, I think, the closest thing an attorney can do to putting a digital kiosk inside of an emergency room,” says digital marketer Bill Kakis, who runs the Long Island, N.Y.-based firm Tell All Digital. Kakis says he recently inked deals with personal injury law firms in the Philadelphia area to target patients.
«
“Potentially” creepy? All-around creepy, unwarranted, unwelcome. I’m constantly amazed at Americans’ ability to monetise the smallest moments of life, as though it were an insult that any moment should be left without commerce.
link to this extract
Software is eating the world, Tesla edition • Marginal REVOLUTION
»
Last week Consumer Reports refused to recommend Tesla’s Model 3 because it discovered lengthy braking distances. This week Consumer Reports changed their review to recommend after Tesla improved braking distance by nearly 20 feet with an over the air software update!
…The larger economic issue is that every durable good is becoming a service. When you buy a car, a refrigerator, a house you will be buying a stream of future services, updates, corrections, improvements. That is going to change the industrial organization of firms and potentially increase monopoly power for two reasons. First, reputation will increase in importance as consumers will want to buy from firms they perceive as being well-backed and long-lasting and second durable goods will be rented more than bought which makes it easier for durable goods producers not to compete with themselves thus solving Coase’s durable good monopoly problem.
«
Coase’s durable monopoly problem (in case you don’t have a JSTOR login) is explained on Wikipedia: essentially, it’s that in a market where you can’t resell a particular product, a monopoly provider will have to go for the lowest, rather than highest, possible price.
Tabarrok is saying that over-the-air updates make items more desirable over time, which keeps pricing higher. Makes sense. There’s also some fun discussion in the comments about how Tesla improved its braking distance so much and so quickly.
link to this extract
This AI knows who you are by the way you walk • Gizmodo
»
Neural networks can find telltale patterns in a person’s gait that can be used to recognize and identify them with almost perfect accuracy, according to new research published in IEEE Transactions on Pattern Analysis and Machine Intelligence. The new system, called SfootBD, is nearly 380 times more accurate than previous methods, and it doesn’t require a person to go barefoot in order to work. It’s less invasive than other behavioral biometric verification systems, such as retinal scanners or fingerprinting, but its passive nature could make it a bigger privacy concern, since it could be used covertly.
“Each human has approximately 24 different factors and movements when walking, resulting in every individual person having a unique, singular walking pattern,” Omar Costilla Reyes, the lead author of the new study and a computer scientist at the University of Manchester, said in a statement.
To create the system, Reyes compiled a database consisting of 20,000 footstep signals from more than 120 individuals. It’s now the largest footsteps database in existence. Each gait was measured using pressure pads on the floor and a high-resolution camera. An artificially intelligent system called a deep residual neural network scoured through the data, analyzing weight distribution, gait speed, and three-dimensional measures of each walking style. Importantly, the system considers aspects of the gait, rather than the shape of the footprint.
«
I certainly recall writing stories about systems that could recognise whether you were up to no good in, say, a car park by how you walked: did you head purposefully in one direction or amble around (sizing up cars)? Identification by gait has also been a thing for a while – it’s a plot strand in Mission Impossible: Rogue Nation. When that opened in 2015, Gizmodo asked “why does this [gait analysis] even exist??” (Though as it points out, there are many more difficult questions you could ask about MI:RN.)
And actually.. what are the circumstances where you’d use this?
link to this extract
Mary Meeker’s 2018 internet trends report: All the slides, plus analysis • Recode
Rani Molla pulls some highlights from the full presentation; these are a few of the higher highlights:
»
• Despite the high-profile releases of $1,000 iPhones and Samsung Galaxy Notes, the global average selling price of smartphones is continuing to decline. Lower costs help drive smartphone adoption in less-developed markets.
• Mobile payments are becoming easier to complete. China continues to lead the rest of the world in mobile payment adoption, with over 500 million active mobile payment users in 2017.
• Voice-controlled products like Amazon Echo are taking off. The Echo’s installed base in the US grew from 20 million in the third quarter of 2017 to more than 30 million in the fourth quarter.
• Tech companies are facing a “privacy paradox.” They’re caught between using data to provide better consumer experiences and violating consumer privacy.
• Tech companies are becoming a larger part of U.S. business. In April, they accounted for 25% of US market capitalization. They are also responsible for a growing share of corporate R&D and capital spending.
• E-commerce sales growth is continuing to accelerate. It grew 16% in the US in 2017, up from 14% in 2016. Amazon is taking a bigger share of those sales at 28% last year. Conversely, physical retail sales are continuing to decline.«
How spies can use your cellphone to find you – and eavesdrop on your calls and texts too • The Washington Post
Craig Timberg on the creaking, insecure SS7 system that helps track phones for carriers, and so is exploited to track individuals:
»
[US Senator Ron] Wyden said the risks posed by SS7 surveillance go beyond privacy to affect national security. American, Chinese, Israeli and Russian intelligence agencies are the most active users of SS7 surveillance, experts say, and private-sector vendors have put systems within the reach of dozens of other governments worldwide. Sophisticated criminals and private providers of business intelligence also use the surveillance technology.
“America is the Number One target, far and away. Everyone wants to know what’s happening in America,” said Brian Collins, chief executive of AdaptiveMobile Security, a cellular security firm based in Dublin. “You will always be a target, whether at home or away.”
Other experts said SS7 surveillance techniques are widely used worldwide, especially in less developed regions where cellular networks are less sophisticated and may not have any protection against tracking and interception. But the experts agreed that Americans are significant targets, especially of rival governments eager to collect intelligence in the United States and other nations where Americans use their cellphones.
Collins said his firm detected a surge in SS7 queries in US networks in late 2014 that it thinks was related to the Office of Personnel Management hack in which intruders — widely reported to be Chinese — gained access to the files of millions of federal workers, including in some cases their phone numbers. (Although publicly reported in 2015, the hack began at least a year earlier.)
AdaptiveMobile Security also detected an uptick in malicious SS7 queries this month in the Middle East, in the days after President Trump announced the US withdrawal from the Iran nuclear agreement, Collins said. This surveillance probably was the work of intelligence agencies studying how the US move would affect oil prices and production, Collins said.
«
Sonic and ultrasonic attacks damage hard drives and crash OSes • Ars Technica
»
Attackers can cause potentially harmful hard drive and operating system crashes by playing sounds over low-cost speakers embedded in computers or sold in stores, a team of researchers demonstrated last week.
The attacks use sonic and ultrasonic sounds to disrupt magnetic HDDs as they read or write data. The researchers showed how the technique could stop some video-surveillance systems from recording live streams. Just 12 seconds of specially designed acoustic interference was all it took to cause video loss in a 720p system made by Ezviz. Sounds that lasted for 105 seconds or more caused the stock Western Digital 3.5 HDD in the device to stop recording altogether until it was rebooted.
The device uses flash storage to house its firmware, but by default it uses a magnetic HDD to store the large quantities of video it records. The attack used a speaker hanging from a ceiling that rested about four inches above the surveillance system’s HDD. The researchers didn’t remove the casing or otherwise tamper with the surveillance system.
“For such systems, the integrity of the recorded data is vital to the usefulness of the system, which makes them susceptible to acoustic interference or vibration attacks,” the researchers wrote in a paper titled “Blue Note: How Intentional Acoustic Interference Damages Availability and Integrity in Hard Disk Drives and Operating Systems.”
The technique was also able to disrupt HDDs in desktop and laptop computers running both Windows and Linux. In some cases, it even required a reboot before the PCs worked properly.
«
Yet another reason to use SSDs.
link to this extract
Errata, corrigenda and ai no corrida: none notified



















/cdn.vox-cdn.com/uploads/chorus_asset/file/10835899/slhfldg4.jpg)
