 |
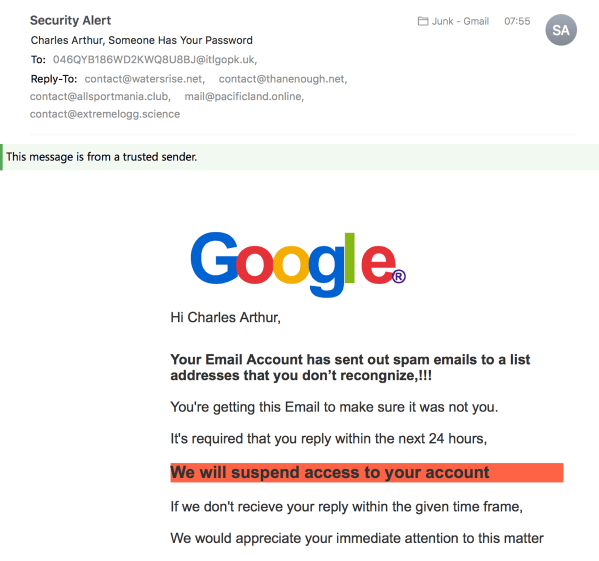
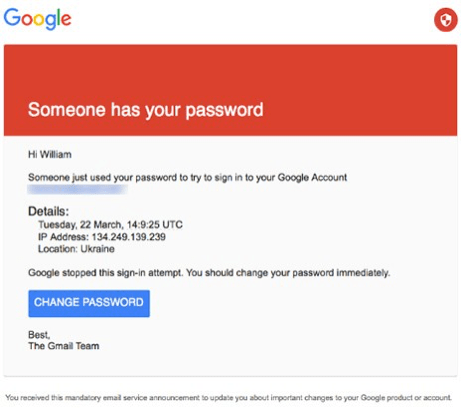
This is the second of a series of posts about my book Cyber Wars, published May 2018 in the UK and in the US, which investigates hacking incidents such as the Sony Pictures hack, the TalkTalk hack, ransomware, the Mirai IoT botnet. It looks at how the people in those organisations responded to the hacks – and takes a look at what future hacks might look like. (The first was on phishing.) |
When I’m giving presentations about Cyber Wars, I often include this picture in a slide. It shows the character Hermione Granger in one of the Harry Potter films opening a door by saying the spell “Alohomora”. Hacking, I explain, is the search for the spell that will open the door. Not a physical door, generally, but the “door” into the target computer so that you can make it do what you want.
I think that the resemblances go deeper, though. The wizards in the Harry Potter novels are all hackers, in one way or another: they’re using their skills to make something that doesn’t ordinarily happen (levitating feathers, say) occur.
Like hackers, they range in ability, from the most basic “script kiddies” following instructions handed down by their seniors – basically, the classrooms where the first-years learn to incant “wingardium leviosa!” – to the people working at the limits of what’s known, good or bad: think Voldemort and his groundbreaking approach to not dying, or Dumbledore and his research (pre-Hogwarts, I think?) into various types of magic.
Mother and father of invention (and wizards)
This might seem like an overcooked metaphor to you, but there’s an important question in the Harry Potter universe which isn’t directly answered in the books.
It’s this: where do spells come from? And the related question: can you invent new ones? This relates to hackers, because if wizards can invent new spells, then they’re exactly like hackers, who are always searching for new ways to break into stuff – think Heartbleed, Meltdown, Spectre, Shellshock – even as they rely on older tried and trusted methods, such as SQLi and buffer overflows, the “Alohomora” and “Accio!” of the hacking world.
JK Rowling never deals with the question of where spells come from in the books. But this doesn’t mean that she hasn’t left clues or that we can’t tease out the truth about it. Rowling famously plotted everything in great detail, but just as she doesn’t deal with where spells come from, she doesn’t deal with what makes a wizard, well, wizardy.
When it comes to wizardry, it’s evident from the way the capability passes through families, and sometimes drops out of families (as in the case of the Hogwarts caretaker Filch, a non-wizard born to wizarding parents who describes himself as a “squib”), or pops up in non-wizarding families (as with Hermione, born to non-wizarding parents) that it is genetic. Inevitably, there’s been a paper written about this, suggesting it’s autosomal dominant; squibs are from double recessives, and wizards born to Muggles from spontaneous mutations. (Autosomal dominant characteristics are usually described for their bad characteristics – Huntington’s disease, for example. Wizards might differ.)
Cast a spell
So let’s move on to spells. We know that there are lots and lots of spells; the children are taught them, at tedious length. It’s clear too that some adults have access to levels of skill in applying spells that the children can’t perceive; think of the fight (best shown in the film) between Voldemort and Dumbledore in the Ministry of Magic, which for my money is the best sequence of all the films.
But crucially, in Harry Potter and the Half-Blood Prince, we learn that spells can be improved upon. Harry comes across an old textbook for his Potions class which has handwritten notes about how to make various potions; they improve on what’s in the book, demonstrating that you can do better than what past wizards do. Harry then discovers a spell in it that he’s never seen before: a fighting curse, “sectumsempra” (which, if it were Latin, would mean “always cut”), which he later employs to almost lethal effect. When he subsequently tries to use it on a fleeing adult, his attempt is deflected – and the adult sneers at him: “you dare use my own spells against me?”
There’s your proof: in the Harry Potter universe, wizards can indeed invent their own spells. The potential is literally unlimited, bounded only by what they can imagine and find to do. That is, spells are not the same as, say, laws of physics or chemical elements. Spells are human – well, wizard – creations rather than natural phenomena.
In this way, Harry Potter wizarding is exactly like hacking. There, people try to find new ways to get computers to do stuff that nobody had expected. You mean that when you demand more data from the input buffer of a TLS server, it gets read and sent back? Sure – that’s Heartbleed, which seems to have been discovered at least three and possibly four times, if you include the two final times that led to its public disclosure. (One of those pre-discoverers is thought to be the US National Security Agency.) Who would have thought to ask that? Who would have thought to try “sectumsempra” as a fighting curse? (In the book, it says that different versions of the word have been written and crossed out before the final one is left. Which leaves you wondering how the previous versions were tested.) Trial and error plays a huge part in hacking too: trying combinations, trying different things, guessing, intuiting. And if you’re lucky or talented or both, you’ll get results.

(image from Wikipedia)
Butterbeer and layer cake
We can also see that the Potter world is striated rather like the hacking world. At the base level, you have the script kiddies (OK, spell kiddies): carrying out commands without really knowing quite how they work, but pleased with the effect.
Then there are the professionals: people who are using these techniques to get things done, and will occasionally invent their own methods to get around limitations that block them. For the most part, though, it’s the careful refinement of existing processes – think of all those people in the Ministry of Magic doing magic gruntwork. Think too of the commercial hackers rewriting a piece of ransomware to take account of the new defences put up against them.
At a higher level still you have those who are using more sophisticated versions of these skills for personal and political ends. Of course we’re back with Dumbledore and Voldemort. What doesn’t vary, though, is the general requirement to explore the capabilities of the systems involved, and in that you’re talking about the same sort of approach. Creating a Horcrux to defeat your enemies? Developing a virus that will wipe every computer on your target’s network once you’ve exfiltrated all their email, spreadsheets and a number of unreleased films? Pretty much the same process: a certain amount of education, knowledge, research, non-live testing, and then implementation.
One point about this metaphor is that we’re used to thinking of Harry Potter and his ilk as the good guys, the white hats, the nice ones. This is true enough if you think that most wannabe hackers go on to be “white hat” players, defending systems from attack from the Hogwarts first-years. (It’s also disconcerting if you take this approach, because a significant number of systems are hacked by people whose hacking skills are comparable with Neville Longbottom rather than Hermione’s.) When you think of Potter creating “Dumbledore’s Army” in “Order of the Phoenix”, just recast it as a password-protected online hacker forum where a bunch of script kiddies are trading methods to break into commercial systems.
When thinking about real-world hackers, it’s useful to consider that some people are very highly skilled – wizards, almost – and that their ability to use the hacker equivalent of the Imperius spell to subvert systems you thought you could rely on means you might not even realise that they’re inside. Certainly that was the experience recently of Dixons Carphone, which in June said that it had discovered that hackers had been inside its systems since the previous July. Eleven months? That’s pretty dramatic, and embarrassing for those who were meant to be guarding the perimeter, and the inside.
One could go on extending this metaphor: Azkaban prison is like any old prison. The Dementors are the plain old law enforcement, taking away your soul – well, computer – and leaving you as good as dead. House-elves are perhaps Internet of Things devices (which would explain why they occasionally cease obeying us altogether when a hacker comes along and gives them different instructions). Other suggestions of metaphor extensions – for dragons, goblins, and other members of that universe – are welcome.
And meanwhile, although there isn’t any discussion of Harry Potter and hacking in my book, there is plenty about hacking topics. See the links at the top.