
You know what helium does to balloons. But what does it do to iPhones (and not Android phones)? Photo by Ed Visoso on Flickr.
A selection of 10 links for you. Swords/ploughshares, laser pointers/?. I’m @charlesarthur on Twitter. Observations and links welcome.
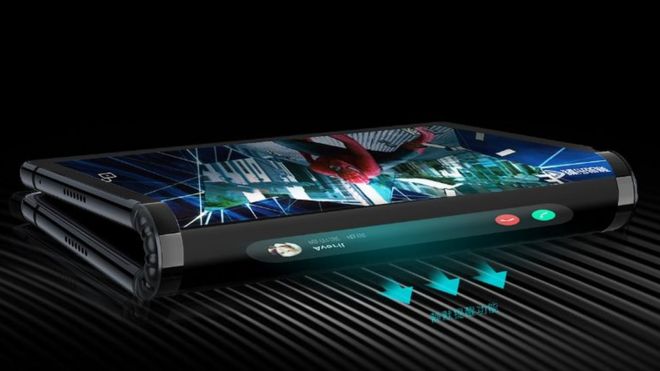
Royole’s bendy-screen FlexPai phone unveiled in China • BBC News
»
A little-known California-based company has laid claim to creating the “world’s first foldable phone”. Royole Corporation – a specialist in manufacturing flexible displays – unveiled the FlexPai handset at an event in Beijing.
When opened, the device presents a single display measuring 7.8in (19.8cm) – bigger than many tablets. But when folded up, it presents three separate smaller screens – on the front, rear and spine of the device. The six-year-old company said it would hold three “flash sales” to consumers in China on 1 November to offer the first product run.
The firm says that when folded the spine of the device will be used to show notifications. Photo: RoyoleThe phones will be priced between 8,999 and 12,999 yuan ($1,290 to $1,863; £1,011 to £1,460) depending on the memory and storage specifications selected.
In addition, Royole said it would also offer a slightly different version of the devices to developers across the world the same day. It intends to start deliveries in “late December”. The launch has caught many industry watchers by surprise.
«
Alternative futures: “Grandpa, how did Royole become the biggest company in the world?”
Or: “Why didn’t any realise that nobody wants a flexible phone screen?”
Plenty of room in the middle, of course.
link to this extract
Once paralyzed, three men take steps again with spinal implant • The New York Times
»
David Mzee broke his neck in 2010. He was a college student in Zurich at the time, an athlete who enjoyed risk and contact, and he flipped off a trampoline and onto a foam pad. “The foam pad, it didn’t do its job,” he said.
Mr. Mzee, now 33, is one of three men who lost the use of their legs years ago after severe spinal injuries, but who now are able to walk without any supports, if briefly and awkwardly, with the help of a pacemaker-like implant, scientists reported on Wednesday.
The breakthrough is the latest achievement in the scientific effort to understand and treat such life-changing injuries. Several recent studies have restored motion to paralyzed or partially paralyzed patients by applying continuous electrical stimulation to the spinal cord.
The new report, described in the journal Nature, is the first demonstration of so-called patterned stimulation: an implant sends bursts of targeted stimulation to the muscles that intend to move. In effect, the stimulation occurs on an as-needed basis, roughly mimicking the body’s own signaling mechanism.
«
The BBC report, with video, is truly amazing.
link to this extract
Luka Sabbat sued for failure to influence • Variety
»
PR Consulting Inc. says it signed an influencer agreement with Sabbat on Sept. 15, the day after he was first photographed with Kardashian. The PR company filed the lawsuit in New York Supreme Court, alleging that Sabbat breached his agreement to post three Instagram stories and one post to his Instagram feed in which he would be wearing the spectacles.
Sabbat made only one Instagram story and one post to his feed, and did not submit the post to PR Consulting for pre-approval, the suit alleges. Sabbat also reneged on an agreement to be photographed in public wearing the spectacles during the Milan or Paris Fashion Weeks, according to the suit.
Under the contract, Sabbat was to be paid $60,000 — with $45,000 paid up front. The suit seeks reimbursement of the $45,000 plus another $45,000 in additional damages.
«
You’re asking “who?” He’s an actor known for.. hmm two films. OK he says he’s a “creative entrepreneur exploring the worlds of art and fashion”. Not technology, then.
link to this extract
‘Stalkerware’ website let anyone intercept texts of tens of thousands of people • Motherboard
Joseph Cox and Lorenzo Franceschi-Bicchierai:
»
A website and app designed to let users monitor their children, employees, or illegally spy on their spouse inadvertently allowed anyone who was using the service to obtain information contained within other peoples’ accounts and intercept the communications of around 28,000 users, Motherboard has confirmed following a tip from a hacker.
The app, called Xnore, can be installed on Android, iPhone, and BlackBerry devices, and collects Facebook and WhatsApp messages, GPS coordinates, emails, photos, browsing histories as well as records phone calls. Customer accounts were exposed by a map feature on Xnore’s website. The flaw allowed anyone who viewed the HTML code of the page to see the mobile identifier used by Xnore to view any collected data. This identifier could then be used to add the intercepted data of someone else’s account to your own.
This new breach of a consumer spyware company—sometimes dubbed ‘stalkerware’ or ‘spouseware’ due to its common target audience of abusive partners—shows how truly lax the security of many of these companies really is. Regardless of whether customers use these apps for legal purposes, they’re putting the intercepted data of their victims—be them their children, employees, or spouses—in serious jeopardy…
…When users download the Xnore app, they are provided a mobile identifier; a string of characters and numbers unique to their device. Xnore offers a free trial so anyone can download the software and start intercepting communications.
The hacker pointed Motherboard to a section of Xnore’s website containing a map. Although the map itself appeared to be non-functional at the time of viewing, a dropdown menu let users select from a slew of mobile identifiers. Viewing the HTML source for that page reveals the identifiers of Xnore users. Motherboard ran a script to extract all of the mobile identifiers included in the exposed data, and found over 28,000 in total. That number matches the total number of Xnore targets the hacker says they found.
«
Couldn’t one effectively disable this simply by turning off its permissions on the phone? And wouldn’t kids figure that out?
link to this extract
MacBook Air vs. iPad Pro: what is Apple’s best new computer? • The Verge
»
In the years since Apple last upgraded the MacBook Air in a meaningful way, I’ve noticed much of my work time gradually shifting to my smartphone, with the laptop taking a secondary role, deployed only when I need the larger screen and more comfortable keyboard. That’s in large part because of the always-on connection of the phone, the immediacy of everything I can do on it, and the connectedness to all of the most popular social and work communication apps. The number of times I’ve caught myself using my phone in front of an open laptop on my lap has been growing.
At its outset, the iPad was dismissed as being merely a “jumbo iPhone,” but in 2018, we might want to start asking if that’s a criticism or a form of praise. The best apps today are being developed for the iPhone and, by the extension of iOS, as the common platform for the iPad. iOS is the operating system of Apple’s future, macOS is the operating system of Apple’s past. As a writer, I find plenty of apps like iA Writer to deposit my loquaciousness into on iOS. As a photographer, I’m excited that real Photoshop is arriving on the iPad. And as a casual gamer, I recognize that iOS gives me vastly more entertainment options that macOS.
«
Similar views are expressed by Lauren Goode in a Wired article:
»
Yesterday’s event had its fair share of subtly awkward moments as Apple tried to present its two philosophies for how it believes you’re supposed to use a computer. On the one hand, there was a new laptop. This clamshell design still matters, Apple was insisting. Moments later, the company was touting a tablet it clearly sees as the real future of computing, something better and more advanced than a notebook. Cook even called the iPad not only the most popular tablet, but also, “the most popular computer in the world.”
«
Lots of people are prepared to tell you that you’ll never be able to do X on an iPad. Given that Photoshop is on the way, audio recording (say, of a Skype interview) is about the only thing left to fix. A gazillion podcasters will rejoice and buy an iPad when that happens.
link to this extract
This ad fraud scheme stole millions, but almost no one in the advertising industry wants to own up to it • Buzzfeed News
»
A massive ad fraud scheme that Google acknowledged stole close to $10m from its ad networks and partners has been shut down after BuzzFeed News revealed its existence last week. But as of today more than 30 companies that unwittingly helped the fraudsters earn money won’t comment on how many fraudulent ads they sold, or say the amount is small or nonexistent.
The fraud operation exposed by BuzzFeed News last week involved more than 125 Android apps and websites that tracked real human users and used this data to program bots to mimic their behavior as a way to evade fraud detection systems. These bots opened apps and loaded webpages in order to generate fake ad views, and therefore revenue for the fraudsters. The affected apps and websites were distributed among a web of shell and front companies to hide their true owners and obscure the scale of the operation.
BuzzFeed News contacted 36 companies that carried ad inventory for the affected apps and sites, or otherwise helped them monetize at some point. Almost none shared specifics about how much money was stolen via their platforms, or whether they will be issuing refunds. Ultimately, the money is stolen from the brands and other companies who bought ads on the affected websites or in apps.
Experts say this lack of transparency is endemic in the digital ad industry, which has a large and growing fraud problem that sees criminals steal billions of dollars a year from advertisers. Many brands now grudgingly accept that a certain amount of the money they spend on digital will be lost to fraud. But when fraud is discovered, as in this scheme or in multiple BuzzFeed News exposés published in the past 12 months, almost no one wants to talk about where the money went, or who stole it.
«
Smart followup by Silverman to his own story; he’s contacted 22 of 36 companies involved, and it only accounts for $300,000. Estimates of how much might have been funnelled away are in the hundreds of millions.
“Nothing to see here, move along” is the story in ad fraud land.
link to this extract
From Silicon Valley elite to social media hate: the radicalization that led to Gab • The Washington Post
Craig Timberg, Drew Harwell, Elizabeth Dwoskin and Emma Brown:
»
Andrew Anglin, creator of the neo-Nazi site Daily Stormer, began posting frequently on Gab, according to reports at the time. The site exploded with new, pseudonymous users posting viral misinformation, hate speech and memes that echoed white-supremacist or anti-Semitic tropes — what Donovan called “an echo chamber of the most disgusting content offered online.”
Google then banned the service from its app store, saying that “social networking apps need to demonstrate a sufficient level of moderation, including for content that encourages violence and advocates hate against groups of people.” In response, Gab sued the search giant.
But the bans and crackdowns haven’t curbed Gab’s growth. There are now about 800,000 users, said Sanduja, compared with 10,000 two years ago. The company’s few employees are all under 30 and number fewer than half a dozen, including Torba and his wife, Sanduja said.
But there are signs that the company’s fractious public image has taken a toll on its leadership. Ekrem Buyukkaya, a Turkey-based developer who co-founded Gab with Torba, said on Sunday that he would step down as the company’s chief technology officer because of “attacks from the American press.” The company had previously said in an SEC filing that Buyukkaya’s work was crucial to its “future success.” Buyukkaya did not respond to requests for comment.
The growth of Gab’s fan base, however, has helped fund an aggressive expansion designed to bring new users into the fold. In an SEC filing in March, Gab said it had more than $600,000 in cash, up from $16,000 in 2016, and had made $100,000 in revenue, primarily from subscriptions.
«
I’d be surprised if the FBI isn’t crawling all over Gab; now you know where 800,000 of the most likely domestic terrorists are. Though hate on that level must be self-limiting in some way. Mustn’t it?
link to this extract
George Soros and the migrant caravan: how a lie multiplied online • USA Today
Brad Heath, Matt Wynn and Jessica Guynn:
»
By Oct. 16 – four days after the caravan departed – the combined following of accounts mentioning both Soros and the caravan had reached 2 million, still a pebble in the flood tide of social media. (The total includes some duplicates because people follow more than one account.)
On Twitter, someone with the username “LibertyBell1000” warned about 42,000 followers that Soros had “manufactured yet another immigrant caravan ‘crisis.’ ” Another, using the name “WhoWolfe,” asked “Anybody else think Soros and the Dirty Dems are behind this?”
More posts spread across Facebook. Trump supporter Randy Penrod posted in a group called “The Deplorable’s,” with about 186,000 members, “Our stable leader just called out the Soros conspired invasion of new Democrat voters in a tweet just moments ago.”
Tap, tap, tap.
It took just one more day for the theory to reach critical mass, breaking through into widespread public consciousness.
The evening of Oct. 17, a Republican member of Congress posted a video on Twitter of what he said was people in Honduras handing out small sums of money to migrants.
“Soros? US-backed NGOs? Time to investigate the source!” he wrote.
Rep. Matt Gaetz would later concede that he was mistaken about where the video was shot (it was Guatemala). But by then his message had metastasized, spreading far beyond the 153,000 people who follow the north Florida congressman’s tweets.
Conservative commentator Ann Coulter retweeted it to her 2 million followers. So did Sarah Carter, a journalist who’s a frequent guest on Fox News.
«
(The URL says El Paso Times, but it’s the story that appeared in USA Today; but its website was having conniptions about European users over that story. No idea why.)
link to this extract
Twitter should kill the retweet • The Atlantic
»
Retweets prey on users’ worst instincts. They delude Twitter users into thinking that they’re contributing to thoughtful discourse by endlessly amplifying other people’s points—the digital equivalent of shouting “Yeah, what they said!” in the midst of an argument. And because Twitter doesn’t allow for editing tweets, information that goes viral via retweets is also more likely to be false or exaggerated. According to MIT research published in the journal Science, Twitter users retweet fake news almost twice as much as real news. Some Twitter users, desperate for validation, endlessly retweet their own tweets, spamming followers with duplicate information.
Retweets were introduced, ironically, to make Twitter better. At the time, the company’s co-founder Biz Stone declared that “we hope interesting, newsworthy, or even just plain funny information will spread quickly through the network making its way efficiently to the people who want or need to know.” Retweets were an early way for the company to ensure that the most interesting and engaging content would bubble up in the feed and keep users entertained.
But for more than two and a half years, the company has shown people tweets based on an algorithmic accounting of exactly what the most interesting and engaging content is (yes, part of that algorithm takes user behavior like retweets into account). It has also tested suggesting tweets, recommending accounts to follow based on interest, and built Moments to surface noteworthy tweets about news events. The retweet isn’t just dangerous; it’s redundant.
«
Before the retweet was a function, one had to manually copy the content of a tweet and put “RT” or “MT” (modified tweet) in front of it. This friction meant something had to be really worthwhile to achieve any velocity.
Increasingly it looks as though adding friction (back in) is the way to make social networks more reasonable.
link to this extract
IPhones are allergic to helium • iFixit
Kyle Wiens on the strange case of a helium leak at a hospital which bricked newer iPhones and Watches – but not Android phones:
»
Every phone has gyroscopes and accelerometers with micrometer-thin elements. My initial theory, shared by some on Reddit, was that the helium molecules were small enough to get inside these chips and interfere with the mechanical workings.
But there are two problems with this idea: One, Apple isn’t alone in using MEMS gyroscopes—every phone has them. Why weren’t the Android phones affected? Perhaps there’s a bug in iOS that causes crashes when it gets faulty data from the gyro? But the bug impacted Apple Watches, too—and they run WatchOS. Additionally, iPhones earlier than the 6 weren’t affected. It seems unlikely that this was a new software bug that impacted both iOS and WatchOS.
So what else could it be? Well, at the heart of every electronic device is a clock. Traditionally, these are quartz oscillators, crystals that vibrate at a specific predictable frequency—generally 32 kHz. When they were first invented, they enabled the first digital ‘quartz’ watches. Now, these frequency generators are at the heart of every electronic device.
Without a clock, the system stands still. The CPU flat out doesn’t work. The clock is literally the heartbeat of a modern device.
But quartz oscillators have some problems. They don’t keep time as well at high (and low) temperatures, and they’re a relatively large component—1×3 mm or so. In their quest for smaller and smaller hardware, Apple has recently started using MEMS timing oscillators from a specialized company called SiTime to replace quartz components.
Specifically, they’re using the SiT512, ‘the world’s smallest, lowest power 32 kHz oscillator.’ And if the MEMS device was susceptible to helium intrusion, that could be our culprit!
«
The electron microscope pictures are amazing too.
link to this extract
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
Errata, corrigenda and ai no corrida: none notified

Further point – think of the number here: “where 800,000 of the most likely domestic terrorists are.”. Eight hundred thousand? That’s a lot of likely domestic terrorists. A quick check gives that there are less than 80 or so bona-fide domestic terrorist incidents in the entire country in a year (roughly, explicitly politically motivated shooting or bombing attempt). Thus we’re talking a yearly rate of less than 1 in 10,000. What could the FBI do in terms of that needle-in-a-haystack problem? Even if there’s probably a needle in there somewhere, it’s still a huge haystack. And any idea that all haystacks must be destroyed so no needles can escape notice (be created doesn’t work in this metaphor) has some pretty profound implications.
On a lighter note, one writer/journalist thing I always wished I could do (but would never have the social backing) was to interview the Federal agent who had the job of monitoring the old cypherpunks list. There was one real (stink) bomber on it, and another (very minor) bomber comes to mind though don’t recall exact details, as well as one person extremely well-versed about how far one could go in terms of threatening government officials while staying on the legal side of the line. I always wondered what the guy who had the surveillance job of reading the list’s voluminous rants, thought about it all.
Digression re 14th amendment. Funny How some people want to be very literal about the 2nd, and very spirit-of & context about the 14th.
Both approaches might be justified. Alternating between the two can’t.
re bendy phone. They must make it a scarf, because that thing will never fit in my pockets. Also, winter is coming.
re. Xnore spying app: If you sneak an app onto my phone and put it in the middle of my Junk folder, it’ll be months before I spot it. And some Launchers offer the ability to fully hide an app, app folders, and file drectories.
re. Interview recording: Isn’t Skype adding that feature for all versions, Video too ?
https://www.theverge.com/2018/7/16/17576348/skype-call-recording-feature
The ad fraud story implies that the security measures are hosted by Google and not the site which hosts the ads, right? Because otherwise i could just direct fake clicks at a site I own without bothering to go through the hoops.