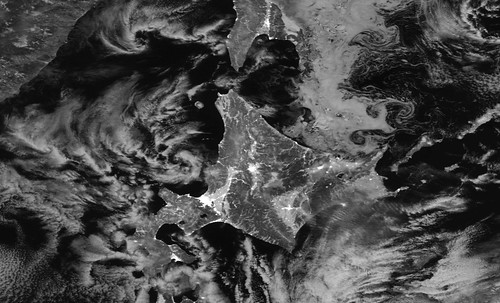
Hokkaido, by night: the number of lights is correlated with GDP. Photo by Stuart Rankin on Flickr.
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
A selection of 9 links for you. Nearly Friday! I’m @charlesarthur on Twitter. Observations and links welcome.
I asked Apple for all my data. Here’s what was sent back • ZDNet
»
What’s interesting about the data is what Apple has – and what it doesn’t.
The zip file contained mostly Excel spreadsheets, packed with information that Apple stores about me. None of the files contained content information – like text messages and photos – but they do contain metadata, like when and who I messaged or called on FaceTime.
Apple says that any data information it collects on you is yours to have if you want it, but as of yet, it doesn’t turn over your content which is largely stored on your slew of Apple devices. That’s set to change later this year when the tech giant will allow customers to download their data archives, largely to comply with new European data protection and privacy rules. And, of the data it collects to power Siri, Maps, and News, it does so anonymously – Apple can’t attribute that data to the device owner.
My entire set of data can be perused in less than an hour – at most.
One spreadsheet – handily – contained explanations for all the data fields, which we’ve uploaded here. Not all the spreadsheets contained information referencing these fields, but it shows you what kind of data Apple can collect on you…
…As insightful as it was, Apple’s treasure trove of my personal data is a drop in the ocean to what social networks or search giants have on me, because Apple is primarily a hardware maker and not ad-driven, like Facebook and Google, which use your data to pitch you ads.
«
In short, it doesn’t tell very much about you. (Side note: the comments. 🙄)
link to this extract
How Sonos played patent hardball to strike Google deal • The Information
Aaron Tilley starts out by explaining how Sonos waved a patent on tuning speakers to rooms to get Google to put Assistant on Sonos products, but this is where it gets more interesting:
»
Sonos was founded in 2002. Despite being located far from Silicon Valley in Santa Barbara, it managed to become an influential player in the tech industry and has grown to $1bn in revenue in 2017.
Along the way, it built up a portfolio of roughly 1,300 patents and pending applications, around features like how music can be streamed to speakers from phones or servers in the cloud, how antennas are laid out on a device or how the speaker can automatically be tuned. Starting in 2016, Sonos has also begun filing more patents around how voice assistants work with its speaker system, said Mr. Triplett.
Sonos’ patents are ranked number two in the electronics industry, behind only Apple, according to Patent Power ranking in IEEE Spectrum, an engineering magazine. The ranking takes into account not the number of patents, but how often they are cited in other company patents and how influential they are.
“Sonos’ patents are highly cited by other companies,” including the likes of Google, Apple and Bose, said Patrick Thomas, co-founder of 1790 Analytics, the intellectual property firm that conducts the Patent Power ranking every year. “It suggests that these companies are looking at Sonos’ technology and saying this is state of the art and how can we improve it.”
Sonos’ most influential patent was filed in 2004 and describes a method for controlling its sound system across multiple speakers. New speaker systems from Apple and Google include a similar feature.
“This is the key patent in their portfolio,” said Mr. Thomas. “It underpins their technology.”
…Sonos appears to have considered, and then mostly abandoned, trying to make money by licensing. Last year, it hired its first chief licensing officer with Tanya Moore, a veteran patent lawyer used to working out massive patent licensing deals at Microsoft and IBM.
Licensing its patents could generate royalty revenue, but would open up competition for Sonos, making it a short-term approach. Sonos appears to have realized that. Ms. Moore left Sonos earlier this year and the company said it doesn’t plan to hire a replacement.
«
That point about licensing being a problem is worth noting.
link to this extract
Vigilante hacks government-linked cyberespionage group • Motherboard
»
Somewhere, government-linked hackers might be panicking. A digital vigilante has struck back against what researchers believe is a cyberespionage group connected to a nation state. The hacker has allegedly stolen, rather ironically, a cache of data that the government-linked hackers lifted from their own victims across the Middle East.
The news provides a rare instance of someone targeting a so-called advanced persistent threat, or APT, as well as an opportunity for a behind-the-scenes look at a government hacking campaign.
“10 minutes of effort; intel on Iranian APTs,” the anonymous hacker told Motherboard in an online chat, saying which nation they believe may be linked to the hacking group. Some cybersecurity experts tentatively agreed. But Kaspersky, which originally reported on the hacking group it dubbed “ZooPark” earlier this month, told Motherboard it could not currently link the outfit to a known actor.
The stolen data the hacker provided to Motherboard though is noteworthy. It includes text messages, emails, and GPS locations seemingly swept up by ZooPark’s tools; audio recordings apparently captured by the malware of people speaking; and the hacker said they found another related server hosted in Tehran, Iran during their spree.
«
An Android hacking campaign which had victims in Egypt, Jordan, Morocco, Lebanon and Iran. Feels like an Iranian nation-state group.
link to this extract
Trump links ZTE rescue to larger trade talks with China, contradicting top aides • The Washington Post
»
President Trump on Wednesday said for the first time that he would allow a rescue of embattled Chinese telecommunications company ZTE only if China agrees to a range of trade concessions, contradicting several of his top advisers who had said that the firm would be dealt with separately.
Trump’s comments, made in morning Twitter posts, mark the most direct linkage he has made between helping ZTE and extracting concessions from Chinese leaders on trade.
But the Twitter posts also included statements that appear at odds with what he or his aides had asserted in recent days about ZTE and the status of trade talks with China.
The biggest discrepancy came over whether ZTE would be dealt with individually or as part of a larger trade package with China.
“Nothing has happened with ZTE except as it pertains to the larger trade deal,” Trump wrote Wednesday in posts that also criticized CNN and The Washington Post for their coverage of the issue.
«
Their coverage of the issue, where they’d been trying to work out what on earth his strategy was, partly based on his tweets, which seemed conciliatory. And of course from talking to his Commerce Secretary and others. The White House doesn’t know what it’s doing from room to room.
link to this extract
‘I lost it’: the boss who banned phones, and what came next • WSJ
»
Mr. Hoopes put his convictions into practice at group gatherings when he took over a team of about 25 people at the aerospace defense company three years ago. “Every time someone’s phone went off, they had to stand for the rest of the meeting,” he says. Before long, he asked the group to leave their phones at their desks when two or more people got together.
Over time, he says, he has noticed not only an improvement in the quality of conversation and ideas in meetings, but also that his people seem to show more respect and appreciation for one another’s work.
Mat Ishbia, CEO of United Wholesale Mortgage, banned technology from meetings about two years ago and recently asked that his executive team and other managers not check their phones as they walk to and from meetings.
“Don’t act like we’re too important to say hello,” he says he told them. “Make eye contact with people.”
Mr. Ishbia is now piloting another solution to phone addiction. A group of about 250 workers are part of an experiment in which they refrain from all personal phone use at their desks. If they want to use their devices they must go to a common area designated for phone use and socializing. Forty-five days into the trial run, workers are checking their phones a lot less, he said.
«
So we’re moving back towards the point where we use our phones sensibly.
link to this extract
If solar and wind hit 50% of generation, US wholesale energy prices could fall 25% or more • Greentech Media
»
In a world where wind and solar resources make up 40% to 50% of generation, wholesale energy prices will drop by as much as $16 per megawatt-hour, according to a study released Wednesday from a group of researchers at Lawrence Berkeley National Laboratory.
Modeling 2030 scenarios in which CAISO, NYISO, SPP and ERCOT reach combined wind and solar penetration at or above 40%, the researchers found electricity prices will fall — but price fluctuations may increase and the number of peak net-load hours will spread to a greater number of days.
According to co-author Joachim Seel, the study offers a “holistic” analysis of price formation in a decarbonizing market. He said that data is not generally available to the public.
Researchers hope the results, part of a three-part study stretching into the next several years, will offer policymakers, utilities and grid authorities a long-range view of how current choices could impact their future ability to cope with changes in the electric sector.
«
That’s quite a fall – though it would also be a dramatic rise in PV/wind generation.
link to this extract
Microsoft reportedly working on $400 Surface tablets to compete with the iPad • The Verge
»
Microsoft is working on a new line of budget Surface tablets to better compete with Apple’s low-cost iPad options, according to a report from Bloomberg.
According to the report, the new Surface tablets won’t just be smaller, cheaper Surface Pros. Rather, Microsoft is said to be completely redesigning the devices, with 10in screens instead of the 12in size currently found on the Surface Pro, rounded corners that more resemble an iPad than the more rectangular Surface design, and USB-C for charging. Most importantly, priced at $400, they will be more in line with Apple’s cheaper tablets, too.
Bloomberg also claims that the new models will be around 20% lighter than the current Surface Pro, although that reduced weight comes at the cost of around four hours fewer of battery life. Like the full-size Surface, the new budget Surface computer will feature Intel processors and graphics, and run the full version of Windows 10 Pro. (No word on whether or not S Mode will be enabled by default, which may make sense given the budget nature of the device.) And like the iPad, Microsoft is said to be planning on models that offer LTE connectivity.
«
A discussion on Twitter between Tom Warren (longtime Microsoft watcher) and Steve Sinofsky (ex-Surface creator) drew the conclusion that this is more about competing with Chromebooks than the iPad. You’re not going to get people to switch from the iPad to a Surface.
link to this extract
Satellite data strongly suggests that China, Russia and other authoritarian countries are fudging their GDP reports • The Washington Post
»
China, Russia and other authoritarian countries inflate their official GDP figures by anywhere from 15 to 30% in a given year, according to a new analysis of a quarter-century of satellite data.
The working paper, by Luis R. Martinez of the University of Chicago, also found that authoritarian regimes are especially likely to artificially boost their gross domestic product numbers in the years before elections, and that the differences in GDP reporting between authoritarian and non-authoritarian countries can’t be explained by structural factors, such as urbanization, composition of the economy or access to electricity.
Martinez’s findings are derived from a novel data source: satellite imagery that tracks changes in the level of nighttime lighting within and between countries over time…
“The key question that the paper tries to tackle is whether the checks and balances provided by democracy are able to constrain governments’ desire to manipulate information or, more specifically, their desire to exaggerate how well the economy is doing,” Martinez said via email. “The way I try to answer the question above is by comparing GDP (a self-reported indicator, prone to manipulation) and nighttime lights (recorded by satellites from outer space and much harder to manipulate) as measures of economic activity.”
Research published in 2012 by economists from Brown University and the National Bureau of Economic Research showed how changes in nighttime lighting closely tracked with changes in economic activity. “Consumption of nearly all goods in the evening requires lights,” that paper explained. “As income rises, so does light usage per person, in both consumption activities and many investment activities.”
«
The paper leans a lot on others’ data, so it’s hard to see quite how reliable this is. One can think of lots of confounding factors. But it’s an interesting point.
link to this extract
UK police use of facial recognition technology a failure, says report • The Guardian
»
Some in policing see facial recognition as the next big leap in law enforcement, akin to the revolution brought about by advances in DNA analysis. Privacy campaigners see it as the next big battleground for civil liberties, as the state effectively asks for a degree of privacy to be surrendered in return for a promise of greater security.
But for now the Big Brother Watch report says the benefits are missing, because the technology does not work.
The Met used facial recognition at the 2017 Notting Hill carnival, where the system was wrong 98% of the time, falsely telling officers on 102 occasions it had spotted a suspect.
The technology failed to pick out any suspects during the Met’s trial at the previous carnival.
South Wales police have been given £2.1m by the Home Office to test the technology, but so far it gets it wrong 91% of the time. It was used at at a festival to celebrate Elvis, a Kasbian concert in Cardiff, a royal visit by Prince Harry and a Liam Gallagher concert, among other deployments.
On 31 occasions police followed up the system saying it had spotted people of concern, only to find they had in fact stopped innocent people and the identifications were false.
«
So how long until it is good enough, a la Facebook tagging you in photos? A few years? Many years? Never?
link to this extract
Errata, corrigenda and ai no corrida: none notified