
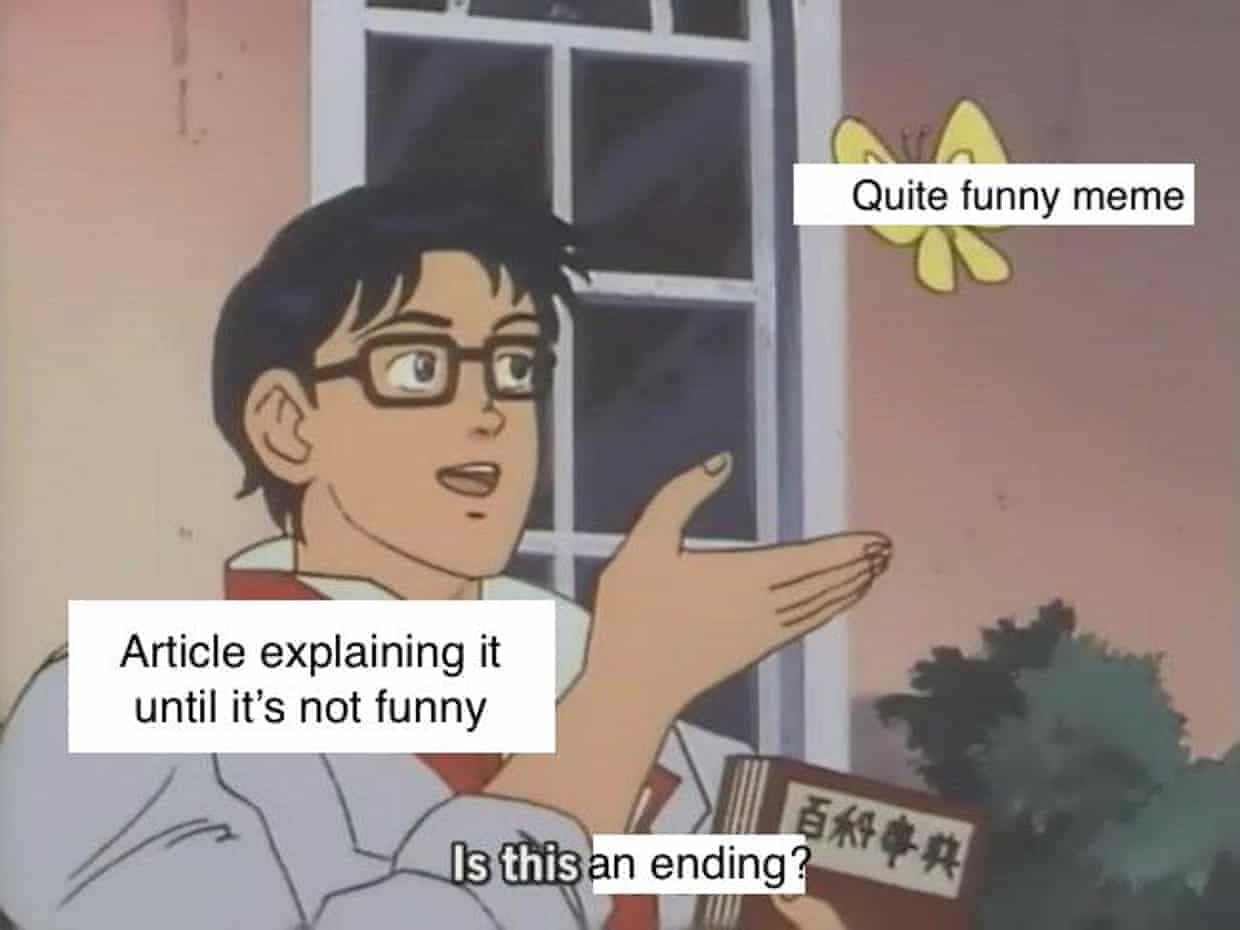
If you don’t recognise this scene, get a kid to explain it to you. Photo by BagoGames on Flickr.
A selection of 11 links for you. No, you broke up the negotiations. I’m @charlesarthur on Twitter. Observations and links welcome.
Facebook closed 583m fake accounts in first three months of 2018 | Technology | The Guardian
»
Facebook said the overwhelming majority of moderation action was against spam posts and fake accounts: it took action on 837m pieces of spam, and shut down a further 583m fake accounts on the site in the three months. But Facebook also moderated 2.5m pieces of hate speech, 1.9m pieces of terrorist propaganda, 3.4m pieces of graphic violence and 21m pieces of content featuring adult nudity and sexual activity.
“This is the start of the journey and not the end of the journey and we’re trying to be as open as we can,” said Richard Allan, Facebook’s vice-president of public policy for Europe, the Middle East and Africa.
The amount of content moderated by Facebook is influenced by both the company’s ability to find and act on infringing material, and the sheer quantity of items posted by users. For instance, Alex Schultz, the company’s vice-president of data analytics, said the amount of content moderated for graphic violence almost tripled quarter-on-quarter…
…Facebook also managed to increase the amount of content taken down with new AI-based tools which it used to find and moderate content without needing individual users to flag it as suspicious. Those tools worked particularly well for content such as fake accounts and spam: the company said it managed to use the tools to find 98.5% of the fake accounts it shut down, and “nearly 100%” of the spam.
Automatic flagging worked well for finding instances of nudity, since, Schultz said, it was easy for image recognition technology to know what to look for. Harder, because of the need to take contextual clues into account, was moderation for hate speech. In that category, Facebook said, “we found and flagged around 38% of the content we subsequently took action on, before users reported it to us”.
«
That’s pretty good work by the AI, though of course we don’t know how many fake accounts it missed.
link to this extract
Russian troll farm hijacked American teen girls’ computers for Likes • Daily Beast
»
The Kremlin-linked Russian troll farm known as the Internet Research Agency took an ominous detour into malware distribution in the middle of the 2016 presidential campaign, targeting teenage girls in the US with a Chrome plug-in that pulled their browsers into a crude botnet, according to an analysis by The Daily Beast and outside security experts.
The app, called FaceMusic, was billed as an embedded music player that would allow users to listen to free tunes while browsing Facebook. The Internet Research Agency purchased Facebook ads promoting the app in May 2016 through one of its fraudulent profiles, “Stop All Invaders,” which normally pushed xenophobic anti-immigration memes in support of the Donald Trump campaign.
Facebook data released by Congress last week shows the FaceMusic ads garnered 24,623 impressions from 107 ads, but only 85 clicks in all. The most successful single ad run, with 28 clicks, used Facebook’s targeting system to go after female users in the United States between 14 and 17 years old. (In total, more than 13,000 machines were likely infected by the FaceMusic malware, according to a Daily Beast analysis.)
Google has since removed the malicious app from the Chrome store, and the public FaceMusic website at fbmusic[.]com is now defunct. But an examination of an archived copy of the code, coupled with an analysis of its web traffic, shows it packed hidden functionality that was active even when the victim wasn’t on Facebook.
«
Despite passing Google’s review before going on the Chrome Web Store, it could connect to a server and silently connect to web addresses it was told to. Considering what Chrome extensions can do, that’s unlikely to have attracted attention. But it’s a basis for clickfraud and botnets. Time to reconsider Chrome extensions, as it once was for ActiveX on IE6?
Qualcomm’s new smartwatch chips launch soon – what do they mean for Wear OS? • Wareable
»
Wear OS is in an awkward spot. Having recently rebranded the smartwatch OS formerly known as Android Wear, Google hopes the number of iPhone users buying Wear smartwatches will continue to swell – but the bedrock on which these wearables are built is starting to fossilise.
Over the last few years Google has assembled an all-star cast of fashion and technology brands to build Wear OS smartwatches, but they’re all being held back by technology that feels antiquated – and is rapidly falling behind the competition. Qualcomm’s Snapdragon Wear 2100 system-on-chip was announced at the start of 2016 and – some software improvements aside – hasn’t been refreshed since, while the Apple Watch and even Samsung’s Tizen smartwatches have bounded ahead.
That will change when Qualcomm unveils its new silicon later this year, said Pankaj Kedia, Qualcomm’s senior director of wearables. The new platform will be announced this autumn alongside a lead smartwatch, he revealed, and by the holidays several partners will have Wear OS smartwatches with the new chipset on the market. Sadly a lot of the specifics will remain under wraps until Qualcomm is ready for a more formal announcement, but in a discussion with Wareable, Kedia and Dennis Troper, Wear OS director of product, confirmed the new platform is coming and gave us a taste of what it will look like.
«
This all feels to me like digital media players in the iPod age. One company made the hardware, another the software, and the content (apps, here) came from another place – though on watches, at least, there’s less demand for third-party apps. The problem with the modular (Microsoft) model, though, is that it can’t move as fast as the vertical one. In this case, the laggard element is Qualcomm, which hasn’t seen enough demand to make it worth updating those smartwatch chips. If the next lot don’t sell – as seems likely – it could be a few years before it updates them again.
link to this extract
Justice Department and FBI are investigating Cambridge Analytica • The New York Times
Matthew Rosenberg and Nicholas Confessore:
»
The Justice Department and the FBI are investigating Cambridge Analytica, the now-defunct political data firm, and have sought to question former employees and banks that handled its business, according to an American official and other people familiar with the inquiry.
Prosecutors have questioned potential witnesses in recent weeks, telling them that there is an open investigation into Cambridge Analytica — which worked on President Trump’s election and other Republican campaigns in 2016 — and “associated U.S. persons.” But the prosecutors provided few other details, and the inquiry appears to be in its early stages, with investigators seeking an overview of the company and its business practices.
The investigation compounds the woes of a firm that has come under intense scrutiny from lawmakers and regulators in the United States and Britain since The New York Times and Observer in London reported in March that it had harvested private data from more than 50 million Facebook profiles, and that it may have violated American election laws. This month, Cambridge Analytica announced that it would shut down and declare bankruptcy, saying that negative press and cascading federal and state investigations had driven away customers and made it impossible for the firm to remain in business.
«
This is what is known in British football manager lingo as “squeaky bum time”.
link to this extract
Is this a pigeon? The story behind the internet’s new favorite meme • The Guardian
»
The image comes from a scene in the show where an android is trying to convince a police detective that he is human. He’s a long way from Westworld standards of artificial intelligence, however, and keeps wrongly identifying the objects around him. He thinks roses are violets, and asks if a butterfly is a pigeon…
…Finding an image that can tell a story so perfectly isn’t easy, but “is this a pigeon?” fits the bill, which is likely why it remerged. It also helps that anyone with the most slapdash editing skills can give it a go, even me.
«
Thank you, Sam. (There are some great other examples in there, though sadly the four-frame biker-father-and-son one has already been forgotten.)
link to this extract
A DC think tank uses fake Twitter accounts and a shady expert to reach the NSA, FBI, and White House • Buzzfeed
»
Earlier this year, leaders from the Marine Corps, the Department of Homeland Security, NASA, the NSA, the White House, and the FBI gathered at a Ritz-Carlton in Virginia to discuss the latest in cybersecurity and information warfare.
The event was organized by the Institute for Critical Infrastructure Technology, a nonprofit think tank founded just a few years ago that quickly established itself as a convener of well-attended cybersecurity events, a facilitator of Capitol Hill briefings, and the beneficiary of hundreds of thousands of dollars in sponsorships from top private sector security vendors.
The day’s closing session featured James Scott, ICTI’s senior fellow and cofounder, discussing Russian cyberinfluence operations and his new book about information warfare. What audience members from intelligence and law enforcement agencies didn’t know is that Scott and ICIT have been running their own deceptive information operation.
BuzzFeed News identified a network of at least 45 fake Twitter accounts being used to amplify ICIT content and Scott’s book, as well as a group of fake YouTube accounts that upload and like ICIT videos and frequently post adoring comments about Scott on content featuring him.
Reporting by BuzzFeed News has also established that Scott, ICIT’s top expert, previously sold spammy and fake social media engagement services, has a history of manufacturing flattering articles about himself and his ventures using dubious SEO techniques, and ran companies that are magnets for online complaints about dishonest business practices. His background in information security also primarily consists of self-published books on the topic that he only began publishing in 2013.
«
Scott has been emailing me (I notice) since early 2016. I haven’t actioned any of it, though the ICIT seems to generate some legitimate-looking content.
White House eliminates top cyber adviser post • POLITICO
»
The Trump administration has eliminated the White House’s top cyber policy role, jettisoning a key position created during the Obama presidency to harmonize the government’s overall approach to cybersecurity policy and digital warfare.
POLITICO first reported last week that John Bolton, President Donald Trump’s new national security adviser, was maneuvering to cut the cyber coordinator role, in a move that many experts and former government officials criticized as a major step backward for federal cybersecurity policy.
According to an email sent to National Security Council staffers Tuesday, the decision is part of an effort to “streamline authority” for the senior directors who lead most NSC teams. “The role of cyber coordinator will end,” Christine Samuelian, an aide to Bolton, wrote in the email to NSC employees, which POLITICO obtained from a former U.S. official.
The NSC’s cyber team has two senior directors, Samuelian wrote, and thus “cyber coordination is already a core capability.”
…“I don’t see how getting rid of the top cyber official in the White House does anything to make our country safer from cyber threats,” Senate Intelligence ranking member Mark Warner (D-Va.) tweeted Tuesday.
«
If they’re not being listened to (and can you believe they were?) it probably doesn’t make any difference if they’re there or not.
link to this extract
How Fortnite captured teens’ hearts and minds • The New Yorker
Nick Paumgarten on the huge hit, which (if you didn’t know) is like a cross between the Hunger Games and Minecraft; 100 of you start, only one can survive:
»
It was hard to do homework on a night like this; Gizzard Lizard returned to the game. He played on a PC he’d built at school. It didn’t have a graphics card. He’d never been a big gamer—his parents were fairly strict about screens and had never consented to an Xbox or even a Wii—though he’d played Minecraft for a while. This level of obsession was something new. He saw on his find-your-friends bar that a bunch of schoolmates were playing, so he FaceTimed one who goes by ism64. They teamed up and hit Lucky Landing. Gizzard Lizard wore an earbud under a set of earphones, so that he could talk with ism64 while listening for the sound of approaching enemies. From a distance, it appeared that he was talking to himself: “Let’s just build. Watch out, you’re gonna be trapped under my ramp. I’m hitting this John Wick. Oh my God, he just pumped me. Come revive me. Build around me and come revive me. Wait, can I have that chug jug? Thank you.”
I’d been struck, watching Gizzard Lizard’s games for a few days, by how the spirit of collaboration, amid the urgency of mission and threat, seemed to bring out something approaching gentleness. He and his friends did favors for one another, watched one another’s backs, offered encouragement. This was something that I hadn’t seen much of, say, down at the rink. One could argue that the old arcade, with the ever-present threat of bullying and harassment and the challenge of claiming dibs, exposed a kid to the world—it’s character-building!—but there was something to be said for such a refuge, even if it did involve assault rifles and grenades.
And then the John Wick was upon him. “Oh God! Oh God!” Foiled again.
A John Wick was an accomplished player who had earned a skin that bears a resemblance to the character played by Keanu Reeves in the “John Wick” movies. (Officially, the skin is called the Reaper, presumably to avoid licensing fees, but players call it John Wick.) It was available to anyone who had attained all hundred tiers of the game in Season 3—a combination of achievement and experience which would have required playing for between seventy-five and a hundred and fifty hours.
«
HTC Exodus: Blockchain powered smartphone for decentralized networks • Business Insider
»
On Tuesday, HTC unveiled the HTC Exodus — a phone that it’s describing as “the world’s first native blockchain phone.”
The HTC Exodus, will be similar to HTC’s other Android smartphones. The difference is that will be designed to support for blockchain-based distributed apps, and feature what the company describes as “built-in secure hardware.”
Details, including price, are currently scant. The big-picture idea, says HTC, is that this is a phone for the privacy-minded user. By using blockchain tech, HTC promises that the Exodus can give privacy-minded users control over their data, without having to rely on the major technology companies for cloud storage.
Furthermore, the phone will come with a built-in cryptocurrency wallet. Ultimately, HTC says that each Exodus will act as a node for the bitcoin and ethereum blockchains — so that every phone increases the overall size and scope of the network.
«
“The folks in marketing have had another brainwave. Yeah, I know. No, this one doesn’t involve paying huge sums to Robert Downey Jr…”
link to this extract
Wisconsin’s voter-ID law suppressed 200,000 votes in 2016; Trump won by 22,748 • The Nation
»
Prior to the 2016 election, Eddie Lee Holloway Jr., a 58-year-old African-American man, moved from Illinois to Wisconsin, which implemented a strict voter-ID law for the first time in 2016. He brought his expired Illinois photo ID, birth certificate, and Social Security card to get a photo ID for voting in Wisconsin, but the DMV in Milwaukee rejected his application because the name on his birth certificate read “Eddie Junior Holloway,” the result of a clerical error when it was issued. Holloway ended up making seven trips to different public agencies in two states and spent over $200 in an attempt to correct his birth certificate, but he was never able to obtain a voter ID in Wisconsin. Before the election, his lawyer for the ACLU told me Holloway was so disgusted he left Wisconsin for Illinois.
Holloway’s story was sadly familiar in 2016. According to federal court records, 300,000 registered voters, 9% of the electorate, lacked strict forms of voter ID in Wisconsin. A new study by Priorities USA, shared exclusively with The Nation, shows that strict voter-ID laws, in Wisconsin and other states, led to a significant reduction in voter turnout in 2016, with a disproportionate impact on African-American and Democratic-leaning voters. Wisconsin’s voter-ID law reduced turnout by 200,000 votes, according to the new analysis.
Donald Trump won the state by only 22,748 votes…
…It’s important to note that this study was conducted by a Democratic Party–affiliated group and has not been peer-reviewed or gone through the typical academic vetting process. While some studies have shown big reductions in turnout among minority voters because of voter-ID laws, others have not. But the Priorities USA study is consistent with a 2014 study by the Government Accountability Office, which found that strict voter-ID laws in Kansas and Tennessee reduced turnout by 2%, enough to swing a close election, with the largest drop-off among newly registered voters, young voters, and voters of color.
«
You won’t be surprised to hear that those disadvantaged by this tended to be African-American, and tended to be Democrat voters.
link to this extract
Twitter will start hiding tweets that “detract from the conversation” • Slate
»
Are you the sort of person who annoys, frustrates, and offends lots of people on Twitter—but manages to avoid technically violating any of its policies on abuse or hate speech? Then Twitter’s newest feature is for you. Or, rather, it’s for everyone else but you.
Twitter is announcing on Tuesday that it will begin hiding tweets from certain accounts in conversations and search results. To see them, you’ll have to scroll to the bottom of the conversation and click “Show more replies,” or go into your search settings and choose “See everything.” Think of them as Twitter’s equivalent of the Yelp reviews that are “not currently recommended” or the Reddit comments that have a “comment score below threshold.”
But there’s one difference: When Twitter’s software decides that a certain user is “detract[ing] from the conversation,” all of that user’s tweets will be hidden from search results and public conversations until their reputation improves. And they won’t know that they’re being muted in this way; Twitter says it’s still working on ways to notify people and help them get back into its good graces. In the meantime, their tweets will still be visible to their followers as usual and will still be able to be retweeted by others. They just won’t show up in conversational threads or search results by default.
You’ve heard of Twitter jail? Let’s call this Twitter purgatory. (Note: This is not Twitter’s preferred nomenclature, as the company’s representatives made clear to me when I suggested the term in a phone call Monday. “That kind of makes me cringe,” a spokesperson said.)
«
“Twitter purgatory” is a neat way to put it. The company blogpost is here; it’s the first work I know that Del Harvey has been involved in since she returned from maternity leave. And it’s good.
link to this extract
Errata, corrigenda and ai no corrida: none notified
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.

It’s hard to disentangle what made Nokia’s current re-success between branding, hardware, and software, but “stock Android with updates” is mentioned in any piece more than 3 sentences long.
I can’t fathom why other OEMs aren’t also doing just that.