
If you wanted headphones, why get them on a crowdfunding site? Photo by Lubomir Panak on Flickr.
 |
A reminder: you can buy my book Cyber Wars, published in the UK and due out in the US later this week. It investigates hacking incidents such as the Sony Pictures hack, the TalkTalk hack, ransomware, the Mirai IoT botnet, the TJX hack, and more. It looks at how the people in those organisations responded to the hacks – and takes a look at what future hacks might look like.
“A terrifying analysis of the dark cyber underworld.” – Aleks Krotoski |
A selection of 11 links for you. A real news source! I’m @charlesarthur on Twitter. Observations and links welcome.
‘Too inconvenient’: Trump goes rogue on phone security • POLITICO
Eliana Johnson, Emily Stephenson and Daniel Lippman:
»
The president, who relies on cellphones to reach his friends and millions of Twitter followers, has rebuffed staff efforts to strengthen security around his phone use, according to the administration officials.
The president uses at least two iPhones, according to one of the officials. The phones — one capable only of making calls, the other equipped only with the Twitter app and preloaded with a handful of news sites — are issued by White House Information Technology and the White House Communications Agency, an office staffed by military personnel that oversees White House telecommunications.
While aides have urged the president to swap out the Twitter phone on a monthly basis, Trump has resisted their entreaties, telling them it was “too inconvenient,” the same administration official said.
The president has gone as long as five months without having the phone checked by security experts. It is unclear how often Trump’s call-capable phones, which are essentially used as burner phones, are swapped out.
President Barack Obama handed over his White House phones every 30 days to be examined by telecommunications staffers for hacking and other suspicious activity, according to an Obama administration official.
The White House declined to comment for this story, but a senior West Wing official said the call-capable phones “are seamlessly swapped out on a regular basis through routine support operations. Because of the security controls of the Twitter phone and the Twitter account, it does not necessitate regular change-out.”
«
Security experts reckon that for sure those are hacked by now. Trump’s number is not secret to those who want to know it. The model of phone is known. There are exploits. What’s stopping them?
link to this extract
North Korea targeting defectors with Android malware attacks • ExtremeTech
»
North Korea has been caught tinkering with Android malware again, but this time it’s using both Facebook and Google Play to target North Korean defectors living in South Korea.
According to McAfee, North Korea’s Sun Team hackers perpetrated the attack over the last several months. They likely infected around 100 targets, which isn’t a huge number compared with most malware campaigns. However, these were all highly targeted infiltrations to gather intelligence on political opponents. There are currently around 30,000 North Korean defectors living in the south.
The hackers used Facebook to distribute links to the malicious apps, focusing on populations and individuals who would have information about defectors. They created convincing fake profiles, often using images stolen from South Korean users as profile photos. Their posts asked the targets to download and test some Android apps hosted in the Play Store. These apps, however, were not what they appeared.
McAfee researchers found three apps uploaded by Sun Team hackers: 음식궁합 (Food Ingredients Info), Fast AppLock, and AppLockFree. All three were listed as “unreleased” in the Play Store, which kept them from garnering unwanted attention. The hackers only wanted to send specific targets to the listings. Upon installation, the apps would ask for access to contacts, SMS data, and local files before sending it all to the malware operators. This data could lead to more targets for future malware attacks, including both defectors and those who help them escape North Korea. McAfee tied the apps together as part of a single attack from the use of identical developer accounts, emails, and IP addresses.
«
A bit amateurish, that last bit.
link to this extract
Trump denies reaching deal with China on ZTE • The New York Times
Ana Swanson, Jim Tankersley and Raymond Zhong:
»
The fate of ZTE has quickly become a key sticking point in negotiations with China, with lawmakers and others concerned that the administration would ease restrictions on the company after Mr. Trump’s suggestion in a Twitter message on May 13 that he was working with China’s president, Xi Jinping, to give ZTE “a way to get back into business, fast.”
“Too many jobs in China lost. Commerce Department has been instructed to get it done!” Mr. Trump added in the tweet.
That statement, and reports that the administration had discussed easing the penalties during a visit by Chinese trade negotiators last week, have sparked a backlash from lawmakers across the political spectrum. On Tuesday, senators took steps to limit Mr. Trump’s ability to ease restrictions on ZTE, voting to approve an amendment to pending legislation that would block the president from pardoning the company without first confirming to Congress that it was no longer violating the law.
In a 23-2 vote, lawmakers approved the amendment, which will now be included in a bill related to foreign investment controls that was offered by Senator Chris Van Hollen, Democrat of Maryland. The amendment would require the president to certify that the company was no longer violating United States law, had not done so for a year and was fully cooperating with investigators before changing its penalties. The bill is expected to come to a vote this summer.
Senator Marco Rubio, a Florida Republican, blasted the idea of a deal with ZTE, saying on Twitter: “Here is #ZTE timeline: Violated U.S. sanction laws & got caught lying & covering up. Paid $1billion fine & agreed to discipline employees. But then lied again & instead of discipline gave those employees bonuses. Now we are offering same deal of fine & employee discipline?”
«
Thought exercise: same situation, but Obama (or Clinton) is president, and is negotiating with China about trade, including ZTE. What would s/he do differently? I suspect much would be the same – except for the tweets, which undermine the US’s position. Even so, it’s contradictory: ZTE broke sanctions on Iran. Which Trump doesn’t like.
link to this extract
Amazon teams up with law enforcement to deploy dangerous new face recognition technology • ACLU of Northern CA
»
Marketing materials and documents obtained by ACLU affiliates in three states reveal a product that can be readily used to violate civil liberties and civil rights. Powered by artificial intelligence, Rekognition can identify, track, and analyze people in real time and recognize up to 100 people in a single image. It can quickly scan information it collects against databases featuring tens of millions of faces, according to Amazon.
Amazon is marketing Rekognition for government surveillance. According to its marketing materials, it views deployment by law enforcement agencies as a “common use case” for this technology. Among other features, the company’s materials describe “person tracking” as an “easy and accurate” way to investigate and monitor people. Amazon says Rekognition can be used to identify “people of interest” raising the possibility that those labeled suspicious by governments — such as undocumented immigrants or Black activists — will be seen as fair game for Rekognition surveillance. It also says Rekognition can monitor “all faces in group photos, crowded events, and public places such as airports” — at a time when Americans are joining public protests at unprecedented levels.
Amazon’s Rekognition raises profound civil liberties and civil rights concerns. Today, the ACLU and a coalition of civil rights organizations demanded that Amazon stop allowing governments to use Rekognition.
«
I think this horse has long since left the stable. If not Amazon, then it will be Facebook; or a Chinese company; or someone else. We’re already in the age of facial recognition; it’s just going to get better.
link to this extract
10,200 people gave this Kickstarter start-up for 3-D headphones nearly $3m. They have nothing to show for it. • The Washington Post
»
In a letter to backers on its Kickstarter page, the tech company Ossic wrote that it was shutting down and would not deliver any remaining orders for Ossic X headphones. The company said it had explored other financing options over the past 18 months but would still need more than $2 million more to complete mass production.
Ossic’s flameout also highlighted the challenges faced by tech companies in mass producing innovative products — from robots to smartwatches to 3-D printers — through crowdfunding sources, even as experts say platforms such as Kickstarter can be effective tools for getting a company off the ground.
“Hardware is particularly seductive in a lot of ways,” said Ethan Mollick, professor of management at the University of Pennsylvania’s Wharton School. “[Backers] see an example of the thing, and it feels safer preordering. Those all come together to make these things seem easier than they might be.”
A video on Ossic’s Kickstarter page showed people testing out prototypes of what the company dubbed the “first 3D audio headphones.” The company told backers on Saturday that it had completed 250 of them and began deliveries to some Kickstarter backers. But as of Saturday, Ossic was out of money and shutting down “effective immediately.” It was unclear whether backers would be refunded.
«
Ossic said “OSSIC X is the world’s first headphone that instantly calibrates to your anatomy for the most accurate and immersive 3D audio”. This stuff is overplayed. (I got some nura headphones via Kickstarter. They’re ok, but too heavy to wear for any length of time, which is a drawback in headphones.) And honestly? You can buy good headphones anywhere. Avoid “stuff you can get elsewhere” on crowdfunding sites.
link to this extract
Yelp files new EU complaint against Google over search dominance
Rochelle Toplensky and Hannah Kuchler:
»
Yelp has filed a complaint with the EU’s antitrust watchdog against Google, arguing that the search company has abused its dominance in local search and pressuring Brussels to launch new charges against the tech giant.
European antitrust authorities fined Google €2.4bn in June 2017 for favouring its own shopping service over rival offerings in its search results. Google denied wrongdoing and has appealed that decision.
Now Yelp, which provides user ratings, reviews and other information about local businesses, wants Margrethe Vestager, the EU Competition Commissioner, to take action against Google for similar alleged abuse in the local search market, according to a copy of the complaint seen by the Financial Times…
…Yelp wrote the new complaint to make the case for local search services, arguing that Google is harming both competitors and consumers by giving preferred placement to its own offerings over rivals’. It said the search giant displays Google Local Search information at the top of the results page, while links to Yelp, TripAdvisor and other services are displayed further down, where they are rarely clicked.
The company is requesting quick action to remove the alleged favouritism, which could enable it to reopen its division in Europe.
Local search services were originally covered by a European antitrust probe launched in 2010, over how Google treated its own services in search results versus links to rivals. That investigation covered a number of specialist search services, including travel, local business and price comparison. But in 2015, Ms Vestager focused her charge sheet on price comparison services culminating in last summer’s fine.
Google declined to comment on the most recent complaint.
«
I don’t have much confidence that Vestager will act quickly on this. Not because she won’t think that it’s important or merited, but because her office is astonishingly slow to act. The fine over shopping was a start, but Google’s response has been to do exactly what complainants said would harm them, and Vestager hasn’t done a thing.
link to this extract
News Lit Quiz • News Literacy Project
»
Which is Legit?
Test your ability to recognize and distinguish “fake news” sites from those of legitimate, standards-based news organizations.
«
10 pairs of fake and real sources; a turn-based quiz. Dive in. As much as anything, reveals how important it is to be able to parse a URL.
link to this extract
Overall Q1 US smartphone sales dip 11% YoY, Apple grows a record 16% YoY • Counterpoint Research
»
Research Director Jeff Fieldhack said, “Dips in sales coming off a holiday period are to be expected, however there are several other factors that make this the weakest Q1 in recent years. For one, postpaid device promotions were not as enticing in the first quarter—most requiring a new line. In addition, prepaid did not receive its usual February and Q1 bump as prepaid service promos cooled. The ramp-down of government subsidized ‘Lifeline’ programs have cut into prepaid device volumes. BYOD and refurbished devices also continue to impact new device sales.”
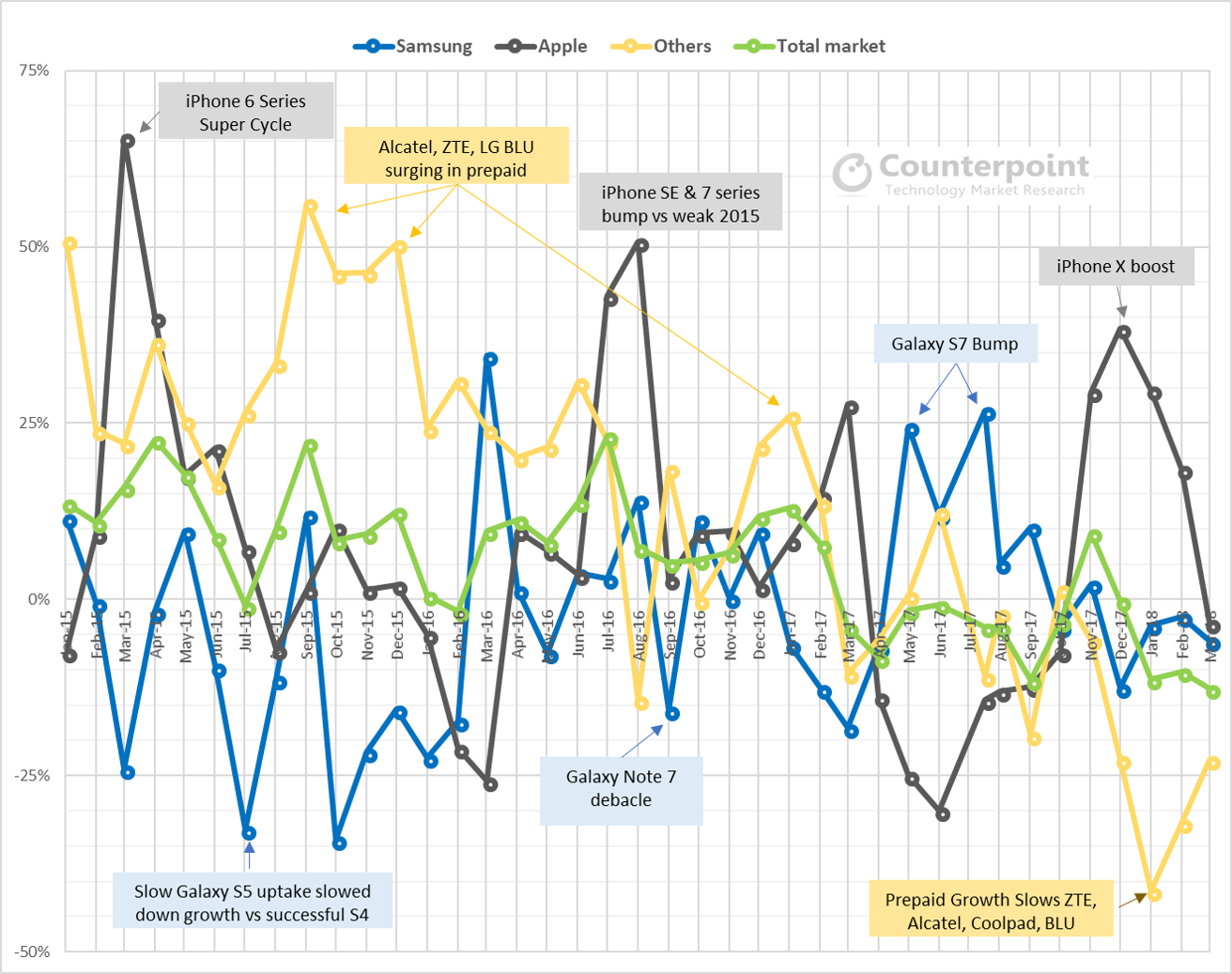
Exhibit 1: Monthly market pulse – OEM & market sales growth (YoY %) Trends
• Apple growth percentage is declining during launch periods. However, it has gained overall US market share because of its increasing installed base and B2B and prepaid channel improvements
• Samsung growth curve is slipping. There is increased difficulty maintaining momentum through product lifecycles
• During periods of prepaid [PAYG] weakness, ‘others’ performance declines. “Others” saw a drastic dip during the first quarter.
• The overall US market growth is on a downward slope outside of Apple launch periods.«
Down to 38.7m in the first quarter; the first time it has been below 40m for three years. The peak has passed.
link to this extract
The Verge [cryptocurrency] hack, explained • The Abacus
Daniel Goldman on a cryptocurrency hack where a hacker began spoofing the time on “blocks”, suggesting they’d happened earlier than they had:
»
The algorithm that Verge [the crryptocurrency, unrelated to the tech news website] uses to calculate the current difficulty [of mining] is known as Dark Gravity Wave; it involves taking a weighted average of the rate of block confirmations over a moving two-hour window. It’s a bit complex, and the details don’t really matter here — what matters is this: mining difficulty is a function of recent block frequency, and running calculations on block frequency naturally involves looking at blocks’ timestamps.
And hence the problem: if enough faulty timestamps are getting created, all bets are off. And this is what the hacker did — examining the blockchain data reveals that throughout the duration of the hack(s), every other block was submitted with a timestamp roughly one hour before the present time, tragically confusing the protocol’s mining adjustment algorithm. If the protocol were sentient and fluent in English, it would be saying something like “Oh no! Not enough blocks have been submitted recently! Mining must be too difficult — let’s make it easier!” Since timestamps were continuously being spoofed, the protocol continuously lowered the difficulty, until mining got laughably easy. To give a general idea, the average difficulty in the hours before the initial attack was 1393093.39131, while during the attack, it got as low as 0.00024414, a decrease in difficulty of over 99.999999%. Lower difficulty in submitting a block means more blocks get submitted— in this case, roughly a block every second.
The cleverness of this attack is in how it circumvents the barrier of mining difficulty instead of attempting to burst through it. If the security provided by mining power is a gate surrounding the network — a gate that’s far too strong to break through and too high to climb over — this hack gets past it by finding a way to lower it so close to the ground that it can be stepped over.If it isn’t already obvious, this is, in and of itself, bad news.
«
Yeah, it was obvious. It’s also obvious that there’s no obvious way to fix this (though it’s more complicated just than this; there’s also an algorithmic attack). Anyone determined enough can do the exact same hack again – though the hacker here clearly got a lot of ducks in a row.
link to this extract
The $299 Razer Core X is the cheapest way to give your MacBook the graphics card it deserves • BGR
»
The obvious solution [to the MacBook’s lack of graphics power] is to use an external graphics card, which is now feasible thanks to software changes in recent versions of macOS, and the magic of the Thunderbolt 3 connectors that are fast and flexible enough to allow for external graphics. Razer’s Core (and the newly updated Core V2) are some of the most popular enclosures around, but they don’t come cheap: the Core V2 is $499, and you still have to supply your own graphics card, which can be hundreds of dollars more. Luckily, there is now a cheaper way.
The Razer Core X is exactly the same concept as the Core V2 — a big box into which you can stuff your graphics card — but with a few key differences. Mostly, it’s $299 rather than $499, which makes it a much more palatable option as an accessory. There’s also a slightly more powerful 650W power supply and space for a bigger graphics card. Best of all, the Core X can supply 100W of power over the USB-C cable to a connected laptop, meaning one cable charges your laptop and connects you to the external graphics. The Core V2 supplied power as well, but that maxed out at 65W, below the 80-85W that some laptops require.
That said, you do lose something, specifically the USB-A and Ethernet ports that the Core V2 had.
«
That’s a graphics card which has a SIX HUNDRED AND FIFTY WATT power adapter. Run it for two hours and you’ve used more than a kilowatt. That’s crazy, given that the MacBook adapter is around 80W max. The tail is wagging the dog, power-wise. Although if you needed to edit video in specific locations, yet also wanted something light to take around, it could fit the bill.
link to this extract
A new look inside Theranos’ dysfunctional corporate culture • WIRED
John Carreyrou, with another extract from his book Bad Blood:
»
The biggest problem of all was the dysfunctional corporate culture in which it was being developed. [CEO and founder Elizabeth] Holmes and [COO Sunny] Balwani regarded anyone who raised a concern or an objection as a cynic and a nay-sayer. Employees who persisted in doing so were usually marginalized or fired, while sycophants were promoted.
Employees were Balwani’s minions. He expected them to be at his disposal at all hours of the day or night and on weekends. He checked the security logs every morning to see when they badged in and out. Every evening, around 7:30, he made a flyby of the engineering department to make sure people were still at their desks working.
With time, some employees grew less afraid of him and devised ways to manage him, as it dawned on them that they were dealing with an erratic man-child of limited intellect and an even more limited attention span. Arnav Khannah, a young mechanical engineer who worked on the miniLab, figured out a surefire way to get Balwani off his back: answer his emails with a reply longer than 500 words. That usually bought him several weeks of peace because Balwani simply didn’t have the patience to read long emails. Another strategy was to convene a biweekly meeting of his team and invite Balwani to attend. He might come to the first few, but he would eventually lose interest or forget to show up.
While Holmes was fast to catch on to engineering concepts, Balwani was often out of his depth during engineering discussions. To hide it, he had a habit of repeating technical terms he heard others using. During a meeting with Khannah’s team, he latched onto the term “end effector,” which signifies the claws at the end of a robotic arm. Except Balwani didn’t hear “end effector,” he heard “endofactor.” For the rest of the meeting, he kept referring to the fictional endofactors. At their next meeting with Balwani two weeks later, Khannah’s team brought a PowerPoint presentation titled “Endofactors Update.” As Khannah flashed it on a screen with a projector, the five members of his team stole furtive glances at one another, nervous that Balwani might become wise to the prank. But he didn’t bat an eye and the meeting proceeded without incident. After he left the room, they burst out laughing.
«
This is just the light relief, though; there’s plenty of refusal to engage with basic reality too.
link to this extract
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
Errata, corrigenda and ai no corrida: none notified

650W is the maximum draw, if you put a reasonable vidcard in there it will draw a lot less power. I guess Razer figured that might as well plan for edge cases and budget enough power for a humongous card. An nVidia 1070 typically draws 150W, a 1080 200W. Anything more than that you’re really getting into specialty card territory.