
Good news! Windows 10’s update won’t do this now. Photo by Delete on Flickr.
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
A selection of 12 links for you. Friday, it is. I’m @charlesarthur on Twitter. Observations and links welcome.
Facebook purged over 800 accounts and pages pushing political messages for profit • The Washington Post
Elizabeth Dwoskin and Tony Romm:
»
Facebook said on Thursday that it has purged more than 800 U.S. publishers and accounts for flooding users with politically oriented content that violated the company’s spam policies, a move that could reignite accusations of political censorship.
The accounts and pages, with names such as Reasonable People Unite and Reverb Press, were probably domestic actors using clickbait headlines and other spammy tactics to drive users to websites where they could target them with ads, the company said. Some had hundreds of thousands of followers and expressed a range of political viewpoints, including a page that billed itself as “the first publication to endorse President Donald J. Trump.” They did not appear to have ties to Russia, company officials said.
Facebook said it was not removing the publishers and accounts because of the type of content they posted but because of the behaviors they engaged in, including spamming Facebook groups with identical pieces of content, unauthorized coordination and using fake profiles.
“Today, we’re removing 559 Pages and 251 accounts that have consistently broken our rules against spam and coordinated inauthentic behavior,” the company said in a blog post. “People will only share on Facebook if they feel safe and trust the connections they make here.”
But the move to target U.S. politically oriented sites, just weeks before the congressional midterms, is sure to be a flash point for political groups and their allies, who are already accusing the tech giant of political bias and arbitrary censorship of political content.
«
The content is pretty shocking, though. It’s the absolute definition of “fake news”: utterly untrue crap intend to create outrage, derision and mistrust. How might that show itself in society, do you think?
link to this extract
I was reported to police as an agitated black male — for simply walking to work • Medium
»
on September 14, campus police were waiting for me when I arrived at the reception desk at Whitmore. I had no idea why but I knew it couldn’t be good. My heart started pounding.
Two university detectives sat me down me in an office and closed the door. Bewildered, I asked what was happening. They refused to answer, as they peppered me with questions.
“What time did you wake up?” “What were you doing at the campus recreation center?” “Did you come into the building agitated?” I felt confused, powerless, and scared, but made sure to maintain my composure. I remembered that even unarmed Black people disproportionately get killed during police encounters, and it was incumbent on me as an innocent Black man to show that I wasn’t a threat. It wasn’t until the end of their interrogation that they revealed why I was being questioned.Someone had called the university’s anonymous tip line, reporting that they had seen an “agitated Black male” who was carrying a “a heavy backpack that is almost hitting the ground” as he approached the Whitmore Administration Building. I — the “agitated Black male” — apparently posed such a threat that police put the entire building on lockdown for half an hour.
I have no idea how the caller come to the conclusion that I was “agitated,” considering they hadn’t interacted with me. I do know that Black people are often stereotyped as angry, armed, or dangerous.
I’ve had to answer to the police before for being a Black man at UMass Amherst.
«
Sometimes America’s problems feel intractable. Another story going around on Thursday: “Georgia woman calls police on black man babysitting white kids: Corey Lewis, who runs a youth mentoring program, was followed by a white woman from a Walmart to his mother’s home.”
link to this extract
Leaked Google research shows company grappling with censorship and free speech • The Verge
»
Google’s presentation acknowledges that “censorship can give governments — and companies — the tools to limit the freedom of individuals.” But it also lays out all the reason why tech platforms like Google search and YouTube are responsible for policing what happens on their apps and websites. The slides give a history of how parts of the internet have become dominated by bad actors, and how both tech companies and governments have failed to address the issues. With regard to censorship, Google notes in the slides how government takedown requests have tripled in the last two years, and how YouTube is now the target of a majority of these requests, with Google Search behind it.
The presentation concludes that tech companies “are performing a balancing act between two incompatible positions,” and that’s the reason why censorship is on the rise as companies like Google, Facebook, and Twitter take more heavy-handed approaches to moderation in response to heightened criticism. The slides conclude that transparency, consistency, and responsiveness are paramount in addressing this ongoing imbalance, and that there is not a “right amount of censorship” that will please everyone and solve these issues.
«
The presentation (linked above) is very finely balanced; it recognises many of the problems that have emerged. Definitely worth reading.
However a couple of points it doesn’t consider: 1) that it’s the concentration (Facebook, Google-YouTube, Twitter) that causes the problem; if all the discussion were happening on a gazillion sites, as happened before 2004, it would be less of an issue; 2) that their algorithms aren’t beautiful indifferent beasts which connect people with precisely the information they want, but instead are actively part of the problem, particularly in the case of YouTube’s recommendation algorithm.
link to this extract
Windows 10 October 2018 Update no longer deletes your data • Ars Technica
»
Microsoft has figured out why the Windows 10 October 2018 Update deleted data from some systems and produced a fixed version. The severity of the bug caused the company to cease distribution of the update last week; the fixed version is now being distributed to Windows Insiders for testing, ahead of a resumption of the wider rollout…
…The software giant claims that only a small number of users were affected and lost data and has published an explanation of the problem.
The storage location of the Known Folders can be changed, a capability called Known Folder Redirection (KFR). This is useful to, for example, move a large Documents folder onto a different disk. Software asking for the Documents Known Folder location will be given the redirected location so it’ll seamlessly pick up the redirection and use the correct place. This is why programs shouldn’t just hardcode the path; it allows this kind of redirection to work.
Redirecting one or more Known Folders does not, however, remove the original folder. Moreover, if there are still files in the original folder, redirecting doesn’t move those files to the new location. Using KFR can thus result in your files being split between two locations; the original folder, and the new redirected folder.
The October 2018 Update tried to tidy up this situation. When KFR is being used, the October 2018 Update will delete the original, default Known Folder locations. Microsoft imagined that this would simply remove some empty, redundant directories from your user profile. No need to have a Documents directory in your profile if you’re using a redirected location, after all. The problem is, it neither checked to see if those directories were empty first, nor copied any files to the new redirected location. It just wiped out the old directory, along with anything stored within it. Hence the data loss.
«
“No longer deletes your data” – looks like the marketing department has found its new tagline.
link to this extract
Outline: secure access to the open web • Google Open Source Blog
Vinicius Fortuna on Google’s Jigsaw project, which aims to protect high-profile targets from surveillance:
»
Censorship and surveillance are challenges that many journalists around the world face on a daily basis. Some of them use a virtual private network (VPN) to provide safer access to the open internet, but not all VPNs are equally reliable and trustworthy, and even fewer are open source.
That’s why Jigsaw created Outline, a new open source, independently audited platform that lets any organization easily create and operate their own VPN.
Outline’s most striking feature is arguably how easy it is to use. An organization starts by downloading the Outline Manager app, which lets them sign in to DigitalOcean, where they can host their own VPN, and set it up with just a few clicks. They can also easily use other cloud providers, provided they have shell access to run the installation script. Once an Outline server is set up, the server administrator can create access credentials and share with their network of contacts, who can then use the Outline clients to connect to it.
«
Very smart, letting them create their own VPN.
link to this extract
Chrome OS grows from underdog to attack dog • ZDNet
»
…at a time when only a handful of major companies (Samsung and Huawei) continue to pursue larger Android tablets. Google has apparently decided to step in with a version of its “desktop” OS. This buys Google a few advantages. First, when its circular-buttoned keyboard is attached, the Pixel Slate can switch from more of a tablet mode to a desktop mode. This is similar to what Surface can do, except Google can rely on a huge library of tablet-friendly (if often not optimized) Android apps.
Second, either mode can take advantage of the full desktop version of Chrome, an advantage over iOS (and Android). And third, Chrome OS’ extensive history with mouse and keyboard make it a good match for a desktop mode when connected to an external monitor. There have been questions around the breadth of this need at least since Microsoft launched Continuum for Windows Phones, but it should provide a more familiar experience than, say, Samsung’s DeX.
On the other hand, the Pixel Slate faces many obstacles. Among these are general continued softness in the general tablet market, Google’s limited retail footprint and enterprise channels, and little awareness or momentum of Chrome OS beyond education, much less acceptance of it as a tablet operating system. A larger tablet, the Pixel Slate with its keyboard cover will cost about $800 with a Celeron, about the same price as the smaller 10.5-inch iPad Pro with an Apple keyboard cover (and $150 less than a keyboard-equipped 12.9-inch model).
It’s less than a similarly sized Surface Pro 6 with Keyboard Cover ($1,060) although that device’s minimum configuration includes a Core i5 processor and more RAM offset by Windows’ larger footprint. So, all in all, the Pixel Slate is competitively priced, although not dramatically cheaper versus the main keyboard-equipped tablets from its main ecosystem rivals.
«
Rather depends on its ability to persuade people that they want the minimalism of ChromeOS compared to the variety of iOS apps (includes Microsoft Office) or, well, full Windows. Works for schools, of course.
link to this extract
Hackers are using stolen Apple IDs to swipe cash in China • Bloomberg
»
Alipay, whose parent also operates the world’s largest money market fund, said on its Weibo blog that it contacted Apple and is working to get to the bottom of the breach. It warned users that’ve linked their Apple identities to any payment services, including Tencent’s WePay, to lower transaction limits to prevent further losses. Tencent said in a separate statement it too had noticed the cyber-heist and reached out to the iPhone maker.
China’s two largest companies both recommended that users of their digital wallets take steps to safeguard their Apple accounts, including by changing passwords. It’s unclear how the attackers may have gotten their hands on the Apple IDs, which are required for iPhone users that buy content such as music from iTunes or the app store. Apple representatives haven’t responded to requests and phone calls seeking comment.
“Since Apple hasn’t resolved this issue, users who’ve linked their Apple ID to any payments method, including Alipay, WePay or credit cards, may be vulnerable to theft,” Alipay said in its blogpost.
Digital payments services have become a tempting target for cyber-thieves as their popularity surges around the world. Ant Financial, which is controlled by billionaire Alibaba co-founder Jack Ma, is estimated to handle more than half of China’s $17 trillion in annual online payments. Formally known as Zhejiang Ant Small & Micro Financial Services Group, it leveraged Alipay’s popularity to expand into everything from asset management to insurance, credit scoring and lending. It serves more than 800 million customers. Tencent’s rival payments offering is a key component of the social media service WeChat, which has a billion-plus users.
«
Wonder how many of the hacked accounts used two-factor authentication? By the way, do you use it on (check) Facebook, Twitter, Dropbox, Gmail/Hotmail/Yahoo Mail, Amazon?
link to this extract
Microsoft pulls ‘Minecraft’ for Apple TV due to low demand • Yahoo News
»
You probably didn’t have a hankering to build Minecraft worlds on your Apple TV, and Microsoft has quietly acknowledged that reality. The company recently started notifying players that it had stopped updating and supporting the Apple TV version of the game on September 24th in order to “reallocate resources to the platforms that our players use the most.” To phrase it differently, there weren’t enough people playing to justify the investment. The game will continue to work, including Marketplace purchases, but you won’t see new features. It’s not available in the App Store, either.
If you made any Minecraft purchases for Apple TV within 90 days of the original announcement, you can ask for refunds.
It’s somewhat telling that people didn’t even draw attention to Minecraft’s fate on Apple TV until well after the 24th – you’d have heard about it right away on most other platforms. You can likely attribute it to a combination of the device’s limitations with Microsoft’s priorities. Minecraft effectively required a Bluetooth gamepad, severely restricting the audience – were you going to spend that extra money just so that you could construct towers and fend off Creepers? The Apple TV version was also late to key features like the Realms multiplayer system, making it the last place you’d want to go if you insisted on playing the hottest new content.
«
Apple’s strategy around Apple TV and games is terrifically unobvious. Its idea two years ago that “TV is about apps” seems to have gone nowhere. Its TV content strategy hasn’t quite happened. TV is difficult in the US because of content costs, but Netflix does OK on £10 or so per month.
link to this extract
Lenovo reclaims the #1 spot in PC rankings in Q3 2018 • IDC
»
Preliminary results for the third quarter of 2018 (3Q18) show that shipments of traditional PCs (desktop, notebook, and workstation) totaled nearly 67.4m units, marking a decline of 0.9% in year-on-year terms, according to the International Data Corporation (IDC) Worldwide Quarterly Personal Computing Device Tracker. Unlike 2Q18, which grew, the 3Q18 results nonetheless outperformed the forecast which called for a decline of 3.0% due to several factors…
…”Q3 came in better than expected,” said Jay Chou, research manager with IDC’s P ersona l C omputing Device Tracker. “But the outlook remains uncertain as we head into the holiday season, when volume will be boosted by many consumer-oriented promotions in entry-level SKUs. AMD supply could help with processor demand somewhat, but it will also take time for OEMs to spec in more models.”
“Despite looming concerns around CPU shortages, the PC market in the U.S. turned in a good quarter backed by strong results in the notebook segment,” said Neha Mahajan, senior research analyst, US Devices & Displays. “Healthy business PC volume, steady Chromebook shipments to U.S. K-12, and a growing gaming consumer base have been the key reasons for the optimism around the U.S. PC markets.”
«
Hooray! Only down a bit rather than a lot! Notable: Apple sales quite a long way down (11%), though this is an estimate. Equally, IDC’s estimates tend to be higher than Apple’s actual figures.
Gartner, meanwhile, puts the market at “flat growth” (huh?) with 0.1% growth, to 67.2m units. So that’s some agreement.
link to this extract
Discord is a safe space for white supremacists • Slate
»
White-supremacist groups aren’t turning up publicly, in force, like they did in Charlottesville last year, but they’re still out there. And Discord in particular remains a very popular destination for communities of neo-Nazis and white supremacists to socialize, share hateful memes, boost the ideas that undergird their movements, inculcate strangers, and plan activities that take place elsewhere online. In the course of an afternoon, I found and joined more than 20 communities on the platform that were either directly about Nazism or white supremacy or reveled in sharing anti-Semitic and racist memes and imagery. “Discord is always on and always present among these groups on the far-right,” says Joan Donovan, the lead researcher on media manipulation at the Data & Society Research Institute. “It’s the place where they do most of the organizing of doxing and harassment campaigns.”
One reason that this might be worrying is that Discord is a far more important internet platform—especially for people who want to be part of hateful online communities—than its frequency in the headlines would suggest. Discord’s user base of more than 150 million may mostly consist of gamers chatting about gaming, but in certain corners of the platform, swastikas are exchanged like high-fives. The groups have names like “Nazism ’n’ Chill,” “Reich Lords,” “Rotten Reich,” “KKK of America,” “Oven Baked Jews,” and “Whitetopia.” They appear to have thousands of participants who trade memes and jokes, share links, condemn “social justice warriors,” and transmit the revisionist histories that bolster their rationalizations of Nazism and white supremacy. I found these communities mostly through Discord search sites (like Discordservers.com, Discord.me, and Disboard.org) as well as through invites posted in some of the Discord groups.
«
It’s meant to be for gamers. However…
link to this extract
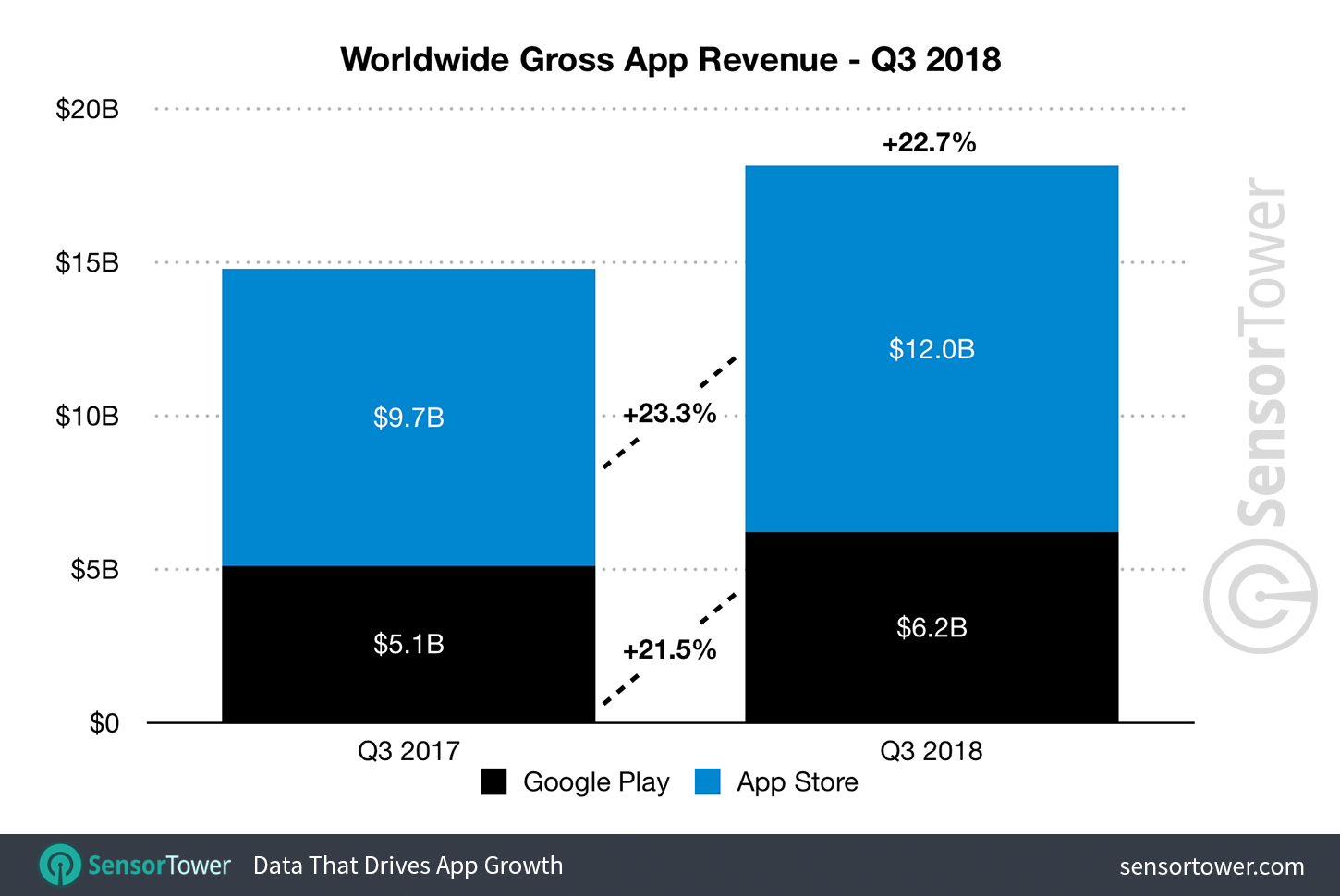
App Store generated 93% more revenue than Google Play in Q3 • TechCrunch
»
Based on Sensor Tower’s chart of top-grossing apps across both stores, subscriptions are continuing to aid in this revenue growth. Netflix remained the top-grossing non-game app for the third quarter in a row, bringing in an estimated $243.7m across both platforms. Tinder and Tencent Video remained in the second and third spots, respectively.
Mobile game spending also helped fuel the revenue growth, with spending up 14.9% year-over-year during the quarter to reach $13.8bn. In fact, it accounted for 76% of all app revenue across both platforms in the quarter, with $8.5bn coming from the App Store and $5.3bn from Google Play.
In terms of app downloads, however, Google Play still has the edge thanks to rapid adoption of lower-cost Android devices in emerging markets, the report said. App installs grew 10.9% across both stores, reaching 27.1 billion, up 24.4% from Q3 2017.
«
I recall, some years ago when I used to write this story every quarter, people – well, commenters – assuring me that it wouldn’t be long before revenues from Google Play would overhaul those in the App Store. (Here’s a classic example, right from the very first comment.) And yet six years on, hasn’t happened.
Probably the key point is that Sensor Tower (and others) can’t see the revenues that developers and Google get from in-app advertising. However, that’s very much the smallest part – maybe 12%? – of the three monetisation strategies (paid-for, in-app, advertising), according to this report which covers 2011-2017. Any more recent data welcome.
link to this extract
Hardware Unboxed analyzes Intel’s commissioned core i9-9900k benchmarks • HardOCP
»
Hardware Unboxed did a short analysis of a few of the benchmarks as their team felt that the i7-8700K benchmarks and the AMD Ryzen 2700X numbers were incorrect. They found that Principled Technologies had allegedly gimped the AMD CPUs by using different coolers, incorrect ram timings, and possibly even disabled some of the cores on the AMD Ryzen 2700X. To put this into perspective, on the Ashes of the Singularity benchmark that Hardware Unboxed ran, the AMD Ryzen 2700X was 18% faster and the i7-8700K was 4% slower, than the commissioned testing that Intel has published. They even showed how over a suite of games that the i7-8700K was only 9% faster than the AMD Ryzen 2700X in previous pure gaming benchmarks conducted by Hardware Unboxed. Yet in Intel’s commissioned benchmark results, the AMD Ryzen 2700X was far, far, behind the Intel i7-8700K in performance metrics. This is why we never trust a manufacturer’s benchmarks. Always wait for the review before buying hardware.
«
So Intel is “choosing” who benchmarks its processors for broader publication so that they will come out ahead of AMD. It feels weird to be living in a time when Intel cares again about AMD being competitive.
That said, unless you’re building a PC from scratch, you don’t have much choice about your processor, do you? (Thanks Stormyparis for the link.)
link to this extract
Errata, corrigenda and ai no corrida: none notified






:no_upscale()/cdn.vox-cdn.com/uploads/chorus_asset/file/13208165/androidwindows10.JPG)










:no_upscale()/cdn.vox-cdn.com/uploads/chorus_asset/file/13170411/twarren_180919_2986_1911.jpg)


