 Monster’s founder and CEO in happier times – 11 years ago. Now things are much worse. Photo by giiks on Flickr.
Monster’s founder and CEO in happier times – 11 years ago. Now things are much worse. Photo by giiks on Flickr.
»You can sign up to receive each day’s Start Up post by email (arriving at about 0700GMT each weekday). You’ll need to click a confirmation link, so no spam.«
A selection of 11 links for you. 3G and two bars will do. I’m @charlesarthur on Twitter. Observations and links welcome.
How Russian spies infiltrated hotel Wi-Fi to hack victims up close • Wired
»
some of the most surprising elements of those intrusion operations are the ones that got the Russian hackers caught red-handed: Parking vehicles outside of target buildings, and infiltrating Wi-Fi networks to hack victims.
“When the conspirators’ remote hacking efforts failed to capture log-in credentials, or if those accounts that were successfully compromised did not have the necessary access privileges for the sought-after information, teams of GRU intelligence officers traveled to locations around the world where targets were physically located,” the Justice Department’s indictment reads. “Using specialized equipment, and with the remote support of conspirators in Russia, these on-site teams hacked into Wi-Fi networks used by victim organizations or their personnel, including hotel Wi-Fi networks.”
The new details on those in-person hacking operations illustrate just how brash the GRU’s hackers have become, says John Hultquist, the director of research at security intelligence firm FireEye, who has closely tracked GRU operations for years. “If they’re willing to play like this, they are extremely aggressive,” Hultquist says. “It’s risky and brazen that they’re doing this physically. Obviously your chance of getting caught and exposed in person are higher, but it gives them a whole new avenue to get into networks that might have otherwise been a challenge.”
«
“Honey? Should I join this network called DEFINITELY NOT STEAL UR DATA? It doesn’t need a password.”
link to this extract
The untold story of Stripe, the secretive $20bn startup driving Apple, Amazon and Facebook • Wired
»
Over the past year, 65% of UK internet users and 80% of US users have bought something from a Stripe-powered business, although very few of them knew they were using it. Where PayPal injects itself into the checkout process, Stripe operates like a white-label merchant account, processing payments, checking for fraud and taking a small percentage: 1.4% plus 20 pence for European cards and 2.9% plus 20 pence for all others. The buyer sees the seller’s name on their credit card statement and, unless the merchant specifically chooses to deploy the Stripe logo, that’s all they’ll ever see.
“It’s not the cheapest provider but it does remove all other intermediaries so it’s the only fee you’ll pay,” Hodges explains. “And if that’s all they did, they’d be interesting. It’s what they did next that’s revolutionary.”
“For many years Stripe had been trying to work out how to deal with what seemed like an obvious opportunity,” explains Billy Alvarado, Stripe’s chief business officer. Alvarado grew up in Honduras, where, in 1998, Hurricane Mitch took out all three bridges in the capital city. “Suddenly you had men, women and children, literally in rubber boots with these pads on their shoulders selling piggy backs across the river to men in suits and women in work clothes,” he recalls. “If you go to any country, you see entrepreneurship everywhere. A lot of these entrepreneurs would love to launch a global internet business. They find it difficult to trade on the world market – but these are literally millions of nascent businesses. We were just trying to work out how we can help them do that simply.”
On February 24, 2016 the company launched the Stripe Atlas platform, designed to help entrepreneurs start a business from absolutely anywhere on the planet. The invitation-only platform allows companies from the Gaza Strip to Berwick-upon-Tweed to incorporate as a US company in Delaware – a state with such business-friendly courts, tax system, laws and policies that 60% of Fortune 500 companies including the Bank of America, Google and Coca-Cola are incorporated there for just $500.
«
Would be great if Delaware would also reform itself so that you could trace ownership of businesses registered there, and bring dirty money to account. Hardly Stripe’s fault it would use it, though.
link to this extract
Some Apple Watch Series 4 models repeatedly crashing and rebooting due to daylight saving time bug • 9to5Mac
»
A bug with the complications on the new Infograph faces in Apple Watch Series 4 is causing some very unhappy Watch owners today. Users in Australia have just experienced the daylight saving time change and are finding their Watches are now stuck in reboot loops.
Specifically, it seems the large Activity complication on the Infograph Modular face is not handling the loss of an hour elegantly, and instead causing the entire device to crash and reboot …
The Activity complication on the Infograph Modular face draws a timeline graph of the current day, showing hour-by-hour data for Move calories, Exercise minutes, and Stand Hours that make up the Activity rings.
In a typical day, there are obviously 24 hours. Although the exact problem has not yet been diagnosed, it appears that the large Activity complication simply cannot handle drawing its graph with one of those twenty four hour missing.
«
It would be hard to think of something guaranteed to throw off computers than daylight saving time.
link to this extract
Apple insiders say nobody internally knows what’s going on with Bloomberg’s China hack story • Buzzfeed News
»
Reached by BuzzFeed News, multiple Apple sources — three of them very senior executives who work on the security and legal teams — said that they are at a loss as to how to explain the allegations. These people described a massive, granular, and siloed investigation into not just the claims made in the story, but into unrelated incidents that might have inspired them.
“We tried to figure out if there was anything, anything, that transpired that’s even remotely close to this,” a senior Apple security executive told BuzzFeed News. “We found nothing.”
A senior security engineer directly involved in Apple’s internal investigation described it as “endoscopic,” noting they had never seen a chip like the one described in the story, let alone found one. “I don’t know if something like this even exists,” this person said, noting that Apple was not provided with a malicious chip or motherboard to examine. “We were given nothing. No hardware. No chips. No emails.”
Equally puzzling to Apple execs is the assertion that it was party to an FBI investigation — Bloomberg wrote that Apple “reported the incident to the FBI.” A senior Apple legal official told BuzzFeed News the company had not contacted the FBI, nor had it been contacted by the FBI, the CIA, the NSA, or any government agency in regards to the incidents described in the Bloomberg report. This person’s purview and responsibilities are of such a high level that it’s unlikely they would not have been aware of government outreach.
«
Apple has been very firm in denying all this, as has Amazon. Quite where this goes next – lawsuits? – is unclear.
link to this extract
Apple’s secret repair kill switch hasn’t been activated—yet • iFixit
»
Apple’s [Mac repair] bulletin states that repairs to a laptop’s display assembly, logic board, upper case, and Touch ID board will require Apple’s secret software toolkit. In case you weren’t counting, that’s pretty much everything but the battery. On desktops, the logic board and flash storage are affected. But how?
Here’s how Apple describes the new process: After replacing a part, a technician must run the configuration suite, which connects to Apple’s Global Service Exchange (GSX) server to perform performance and compatibility checks for the new parts. Without this software, an internet connection, and approval from Apple’s servers, the repair is considered incomplete and the computer is rendered inoperative.
AST 2 is only provided to Apple stores and a very few select ‘Authorized Apple Service Providers’ (AASPs) that are under strict confidentiality and business contracts mandating what parts they can use and what they charge. This shift will leave third-party repair shops out to dry, not to mention the rest of us that are accustomed to fixing our own hardware. It is unclear whether this software is available to certified self-servicing accounts—if not, schools and businesses are out of luck too.
This service document certainly paints a grim picture, but ever the optimists, we headed down to our friendly local Apple Store and bought a brand new 2018 13” MacBook Pro Touch Bar unit. Then we disassembled it and traded displays with our teardown unit from this summer. To our surprise, the displays and MacBooks functioned normally in every combination we tried. We also updated to Mojave and swapped logic boards with the same results.
That’s a promising sign, and it means the sky isn’t quite falling—yet. But as we’ve learned, nothing is certain.
«
There’s a lot of noise about supply chain infiltration recently. I wonder if anyone at iFixit has considered that this might be Apple looking to offer customers protection against (1) counterfeit items (2) surveillance items and (3) people trying to hook covertly into the Secure Enclave? That was what Error 53 was about too. Apple is nothing if not consistent.
link to this extract
Microsoft pulls Windows 10 October 2018 update after reports of documents being deleted • The Verge
»
Microsoft is now recommending that affected users contact the company directly, and if you’ve manually downloaded the October update then “please don’t install it and wait until new media is available.” Other Windows 10 users have been complaining that the Microsoft Edge browser and other store apps have been unable to connect to the internet after the October 2018 Update, and the update was even blocked on certain PCs due to Intel driver incompatibilities.
It’s not clear how many Windows 10 users are affected by the problem, but even if it’s a small percentage it’s still surprising this issue was never picked up during Microsoft’s vast testing of the October update. Millions of people help Microsoft test Windows 10, but the company has struggled with the quality of Windows updates recently. Microsoft delayed its Windows 10 April 2018 Update earlier this year over Blue Screen of Death issues, but those problems were picked up before the update reached regular consumers and businesses.
Microsoft was planning to push the latest October update out to all Windows 10 users next Tuesday, but that’s now likely to be put on hold while investigations continue into this major deletion problem.
«
Warren pointed out on Twitter that Microsoft had been warned about this via the Windows Insider program, yet seems to have thought it fixed.
link to this extract
Making sense of the SuperMicro motherboard attack • Light Blue Touchpaper
Theo Markettos, who is on the security team at Cambridge University’s Computer Lab, considers whether what’s described in the attack is feasible:
»
there’s another trick a bad BMC can do — it can simply read and write main memory once the machine is booted. The BMC is well-placed to do this, sitting on the PCI Express interconnect since it implements a basic graphics card. This means it potentially has access to large parts of system memory, and so all the data that might be stored on the server. Since the BMC also has access to the network, it’s feasible to exfiltrate that data over the Internet.
So this raises a critical question: how well is the BMC firmware defended? The BMC firmware download contains raw ARM code, and is exactly 32MiB in size. 32MiB is a common size of an SPI flash chip, and suggests this firmware image is written directly to the SPI flash at manufacture without further processing. Additionally, there’s the OpenBMC open source project which supports the AST2400. From what I can find, installing OpenBMC on the AST2400 does not require any code signing or validation process, and so modifying the firmware (for good or ill) looks quite feasible.
Where does this leave us? There are few facts, and much supposition. However, the following scenario does seem to make sense. Let’s assume an implant was added to the motherboard at manufacture time. This needed modification of both the board design, and the robotic component installation process. It intercepts the SPI lines between the flash and the BMC controller. Unless the implant was designed with a very high technology, it may be enough to simply divert the boot process to fetch firmware over the network (either the Internet or a compromised server in the organisation), and all the complex attacks build from there — possibly using PCI Express and/or the BMC for exfiltration.
If the implant is less sophisticated than others have assumed, it may be feasible to block it by firewalling traffic from the BMC — but I can’t see many current owners of such a board wanting to take that risk.
So, finally, what do we learn? In essence, this story seems to pass the sniff test.
«
A change in the code (even later reversed) would show up in the repository, surely? Notable, though, that technical people think this attack entirely feasible.
link to this extract
Supply chain security is the whole enchilada, but who’s willing to pay for it? • Krebs On Security
»
Most of what I have to share here is based on conversations with some clueful people over the years who would probably find themselves confined to a tiny, windowless room for an extended period if their names or quotes ever showed up in a story like this, so I will tread carefully around this subject.
The U.S. Government isn’t eager to admit it, but there has long been an unofficial inventory of tech components and vendors that are forbidden to buy from if you’re in charge of procuring products or services on behalf of the U.S. Government. Call it the “brown list, “black list,” “entity list” or what have you, but it’s basically an indelible index of companies that are on the permanent Shit List of Uncle Sam for having been caught pulling some kind of supply chain shenanigans.
More than a decade ago when I was a reporter with The Washington Post, I heard from an extremely well-placed source that one Chinese tech company had made it onto Uncle Sam’s entity list because they sold a custom hardware component for many Internet-enabled printers that secretly made a copy of every document or image sent to the printer and forwarded that to a server allegedly controlled by hackers aligned with the Chinese government.
That example gives a whole new meaning to the term “supply chain,” doesn’t it? If Bloomberg’s reporting is accurate, that’s more or less what we’re dealing with here in Supermicro as well.
But here’s the thing: Even if you identify which technology vendors are guilty of supply-chain hacks, it can be difficult to enforce their banishment from the procurement chain. One reason is that it is often tough to tell from the brand name of a given gizmo who actually makes all the multifarious components that go into any one electronic device sold today.
«
Wikipedia bans right wing site Breitbart as a source for facts • Motherboard
»
Wikipedia editors voted to ban Breitbart as a source of fact in it articles. The consensus, reached late last month, agreed that the outlet “should not be used, ever, as a reference for facts, due to its unreliability.” Wikipedia editors also decided that InfoWars is a “conspiracy theorist and fake news website,” and that the “use of InfoWars as a reference should be generally prohibited.
Breitbart, a far-right conservative media website, has come under scrutiny—such as when it vehemently supported Alabama politician and alleged pedophile Roy Moore, when it shilled for scam cryptocurrencies through its newsletter, or when it fueled racist narratives about black NFL players. Wikipedians decided that because fact checkers have found much of Breitbart’s coverage to be “misleading, false or both,” they won’t abide it as a source of fact anymore.
“We have something over 2,500 links to Breitbart, many of them as sources in articles,” the editor who nominated the rule wrote in the vote. “I think that Breitbart is not a reliable source […] It’s my view that we should not source anything to Breitbart other than strictly factual and uncontroversial facts about Breitbart on the articles related to Breitbart and its people.”
The ensuing discussion about whether Breitbart should be considered a factual source went on for dozens of comments, many of them impassioned. But, overwhelmingly, editors believed it should be banned except when used as a source to attribute opinions or relevant commentary. It has been “deprecated” for English articles, and will no longer be used as a reliable source for facts on the English version of the online encyclopedia.
«
Wikipedia: still better at this sort of thing than most of the internet (and many bits of media), and still largely immune from cat-and-laser pointer attempts to distract it.
link to this extract
The iPhone XS & XS Max review: unveiling the silicon secrets • Anandtech
»
Apple promised a significant performance improvement in iOS12, thanks to the way their new scheduler is accounting for the loads from individual tasks. The operating system’s kernel scheduler tracks execution time of threads, and aggregates this into an utilisation metric which is then used by for example the DVFS mechanism. The algorithm which decides on how this load is accounted over time is generally simple a software decision – and it can be tweaked and engineered to whatever a vendor sees fit.
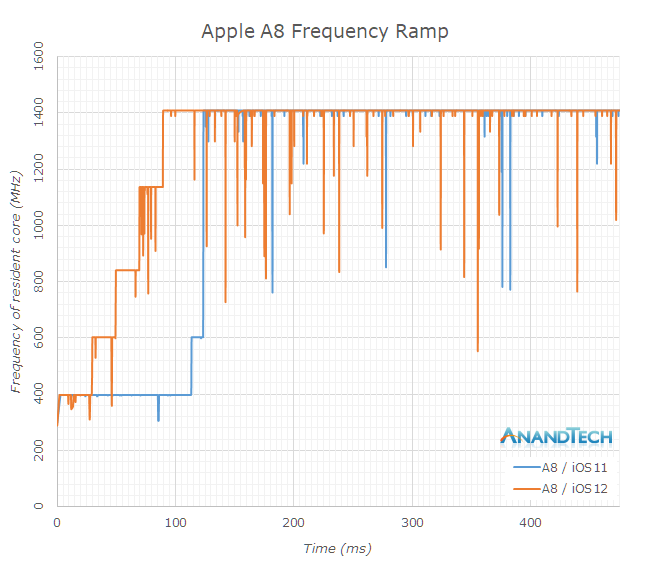
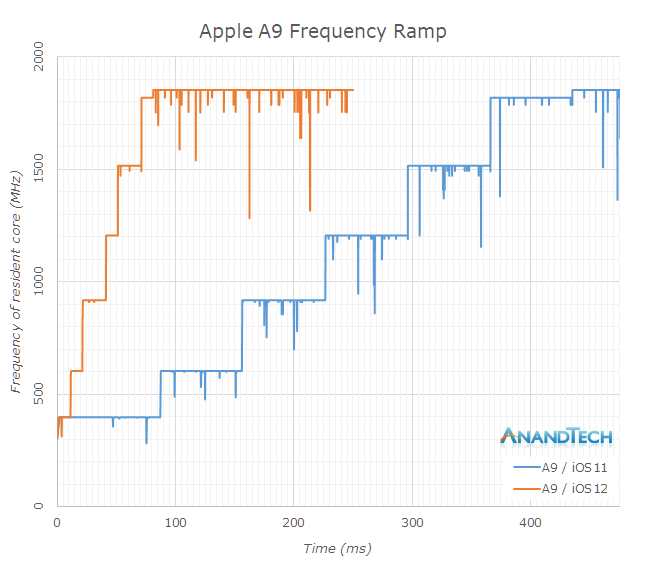
Because iOS’s kernel is closed source, we’re can’t really see what the changes are, however we can measure their effects. A relatively simple way to do this is to track frequency over time in a workload from idle, to full performance. I did this on a set of iPhones ranging from the 6 to the X (and XS), before and after the iOS12 system update.
Starting off with the iPhone 6 with the A8 chipset, I had some odd results on iOS11 as the scaling behaviour from idle to full performance was quite unusual. I repeated this a few times yet it still came up with the same results. The A8’s CPU’s idled at 400MHz, and remained here for 110ms until it jumped to 600MHz and then again 10ms later went on to the full 1400MHz of the cores.
iOS12 showcased a more step-wise behaviour, scaling up earlier and also reaching full performance after 90ms.
The iPhone 6S had a significantly different scaling behaviour on iOS11, and the A9 chip’s DVFS was insanely slow. Here it took a total of 435ms for the CPU to reach its maximum frequency. With the iOS12 update, this time has been massively slashed down to 80ms, giving a great boost to performance in shorter interactive workloads.
«
Most of this multi-page review is just benchmark gobbledygook to me, but this page and those graphics really stand out because it shows iOS 12 getting performance improvements of as much as 50% on old hardware, through tweaks to the core OS.
link to this extract
A Monster fall: how the company behind Beats lost its way • SF Chronicle
»
There was a time, not long ago, when Monster was on everyone’s ears. From 2009 to 2012, its sales of headphones, audio equipment and cables grew tenfold. That year, the company sold a billion dollars of gear, including the hit Beats brand. CEO Noel Lee hung out with music royalty like Lady Gaga and Mary J. Blige.
Now Monster is ailing, as is Lee, amid a fight with a former executive. Its sales have plummeted nearly 95% in five years. Retail stores such as Circuit City and RadioShack that once sold its wares have gone belly-up. Its partnership with Beats dissolved before the headphone maker saw a $3.2bn payday in its sale to Apple. A February Super Bowl ad, the company’s first ever, was a dud, with Marketing Week rating it a “loser.” And new ventures into online gambling and cryptocurrency have gone nowhere.
A company that once hung its name on San Francisco’s Candlestick Park is fighting for its life. While Lee proclaims that the company he founded four decades ago will see another 40 years, the company started laying people off in September.
Its South San Francisco headquarters now occupy just part of one floor of an office building. It shut a distribution center in Las Vegas late last year. In May, it reported having 139 employees, down from 800 a decade ago; the company won’t say how many remain.
«
Amazing; it relied on retail outlets for its products (which always promised far more than they could offer). That 95% fall in sales, though? They should be paired with HTC – which was also involved in Beats’s early years.
link to this extract
Errata, corrigenda and ai no corrida: none notified.

re. Handling DST: time and date on cimputers are fun: http://www.creativedeletion.com/2015/01/28/falsehoods-programmers-date-time-zones.html
re. Apple repairs: I understand the need to check and maintain absolute integrity on *some* computers. I think Apple’s position is both overkill and self-serving fopr *most*: this prevents people from fixing issues themselves or via 3rd-parties, and from switching.
And it hurts users. I currently have 2 open “Apple” issues:
– a very old lady who lost her husband 3 yrs back, forgot her iPad and iCloud and all passwords and messed it up several times so it’s locked down, with all her latest pics of him on it. I got the iPad, she just found the invoice… My plan is to go beg Apple support for help ? Just the pics back, never mind the iPad and the rest of the data ? She’s very distraught.
– a 69 yo relative who’s messed up his Apple and Mail accounts and can’t remember his me.com mail password, and used a forgotten mail account as backup, and can’t seem to type the security questions *exactly* as he typed them in initially. So now he’s carrying 3 phones ‘coz he lives in 2 countries + needs access to his mail. The plan was consolidate all that to a single dual-SIM phone. Apple security is the ultimate lock-in in this case.
There can be too much security. I’m glad I can get back into my home by borrowing a ladder when I forgot my keys, I woudln’t want to be locked out of it definitively.
And strong client security is a misdirection, when you host servers in iffy countries. Hasn’t every iDevice they ever wanted to hack, always been hacked in the end ?
re. the chip hack. Linux considers that no computer is safe once you have physical access to it, even just its keyboard.That chip is “embedded physical access”, and more.
re. Supply chain integrity: that’s a pipe dream: someone at Amazon just got caught selling secrets ? You can’t just certify companies, you’ve got to certify employees, subcontractors, trainees, their partners, janitors. My dad used to work on a project with Russia 35 yrs ago… what did the janitor in was the burning hot photocopier early in the morning. That was back when things where on paper, probably easier to track and lock down.
Re. Anandtech’s XS review: it never hurts to focus on the conclusion instead of on a specific item: https://www.anandtech.com/show/13392/the-iphone-xs-xs-max-review-unveiling-the-silicon-secrets/13
I’ll focus on the negatives, since you focused on the positive.
– Camera pulls up to last year’s Androids in full light, but not in low light
– GPU heats up a lot and sucks lots of power, so sustained gaming is an issue. (*)
– Battery life still not that great. Will probably be less bad on the XR.
That humongous chip is really begging to be used on a desktop/laptop ;-p
I’m not on board with the trend to extreme computational photography. There are too many misfires; it’s OK as an optional mode, but not OK as a substitute for solid optics, which not only Apple but most OEMs seem to be saving money and space on. We’re getting fake (often messed up bokeh), with subpar color fidelity, dynamic range, width of field, and color fidelity. That’s backwards, that bokeh is a cheap misdirection. Again, not only Apple !
(*) that’s sad because iOS has really excellent games and hardware. I think there’s something to Androids getting “gamer” phones with heatpipes, large batteries, lower-rez screens that prioritize smoothness over details, and a few software tricks (automatic DND mode and cleaning of background processes which Android isn’t normally aggressive about…). Not right for most people, but right for gaming.
Re: Monster: but we’ve got Anker now. Anker does everything Monster used to do, but with less marketing fluff, better product, and much, much better value (except that “Nintendo” battery pack, licensing is a con). Creative destruction FTW !
Anker is like Xiaomi to me: I’ve yet to de disappointed by one of their products. Plus I’ve had the opportunity to test their after-sales service (I haven’t Xiaomi’s), and its excellent,