
Americans are paying more for the components of self-build PCs. Yup, tariffs. Photo by GokuPhoto on Flickr.
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
A selection of 14 links for you. OK, but some are short. I’m @charlesarthur on Twitter. Observations and links welcome.
Data from ‘almost all’ Pakistani banks stolen, says FIA cyber-crime chief in Pakistan • Geo.tv
»
The Federal Investigation Agency’s (FIA) cyber-crime chief set off alarm bells on Tuesday when he revealed that customers’ data from “almost all major Pakistani banks” was stolen in a recent security breach.
“Almost all [Pakistani] banks’ data has been breached. According to the reports that we have, most of the banks have been affected,” Director of FIA Cyber-Crimes wing Captain (retd) Mohammad Shoaib told Geo News.
The FIA official’s comments follow a recent report from Group-IB, a global cyber security firm, that hackers had released a new dump of Pakistani credit and debit cards on dark web forums.
By the end of last week, at least six Pakistani banks had suspended usage of their debit cards outside the country and blocked all international transactions on their cards.
Concerns about a breach of credit and debit card data spread in the banking circles, after a cyber attack on Bank Islami last week that siphoned off at least Rs2.6 million from its accounts.
The cyber-crime chief did not reveal exactly when the security breach took place that had affected most Pakistani banks.
“More than 100 cases [of cyber-attack] have been registered with the FIA and are under investigation. We have made several arrests in the case, including that of an international gang [last month],” Capt (retd) Shoaib said.
«
Android security auditing (investigating unauthorized screenshots) • Michael Altfield’s Tech Blog
»
About six months ago, I discovered something on my smartphone that horrified me: I went to undelete a file in DiskDigger, and I stumbled upon a plethora of unexpected jpegs: screenshots of my activity. Screenshots that I didn’t take. Screenshots of my conversations within my encrypted-messaging-app-of-choice. Screenshots of my news feed. Screenshots showing my GPS position in my open source map app. And screnshots of my bitcoin wallet.
I was perplexed. I was astonished. And, to be honest, I was scared. How did this happen? Was it a vulnerability shipped with LineageOS? Could it be some malicious binary embedded into AOSP? Or is it some exploit in one of those damned closed-source apps that I was forced to install through social pressure (*cough* whatsapp).
This week I was honored to be accepted into a 1-week mini batch at the Recurse Center (formerly “Hacker School”) in Brooklyn, NY. And, finally, I decided to roll-up my sleeves and dig into Android Security Auditing with the ultimate goal of finding out what was responsible for creating (and then deleting) all these screenshots. Well, with no thanks to Google, I did find the source. And the codebase is integrated into AOSP. But (spoiler), it’s not something to sweat about. Though it is a fun journey.
«
The answer – as he says, nothing to sweat about – is surprising.
link to this extract
Africa’s biggest markets drive strong growth in continent’s smartphone shipments • IDC
»
A total of 22.4m smartphones were shipped in Africa during the second quarter of this year (Q2 2018), according to the latest insights from International Data Corporation (IDC). The global technology research and consulting firm’s Quarterly Mobile Phone Tracker shows that Africa’s smartphone shipments increased 9.8% quarter on quarter (QoQ) and 6.0% year on year (YoY) in Q2 2018.
The market’s buoyant performance was spurred by the growing popularity of low-end to mid-range devices. Transsion brands continued to lead the continent’s smartphone space in Q2 2018, accounting 35.4% of shipments. Samsung followed in second place with 23.2% share.
By contrast, the feature phone market was down 1.1% QoQ and 5.8% YoY in Q2 2018, but – with shipments totaling 31.4m units – these devices still constitute a 58.3% share of Africa’s overall mobile phone market as they cater to the needs of the continent’s huge low-income population (mainly in rural areas) by providing basic mobile communications that are priced very competitively.
«
That’s just to give you the contrast of the size of the market. Africa’s total population is about 1.3bn; China, with about 1bn population, the Q3 figure was 305m, or about 13x bigger.
link to this extract
Cesar Sayoc and others on Twitter are behaving like bots • Slate
»
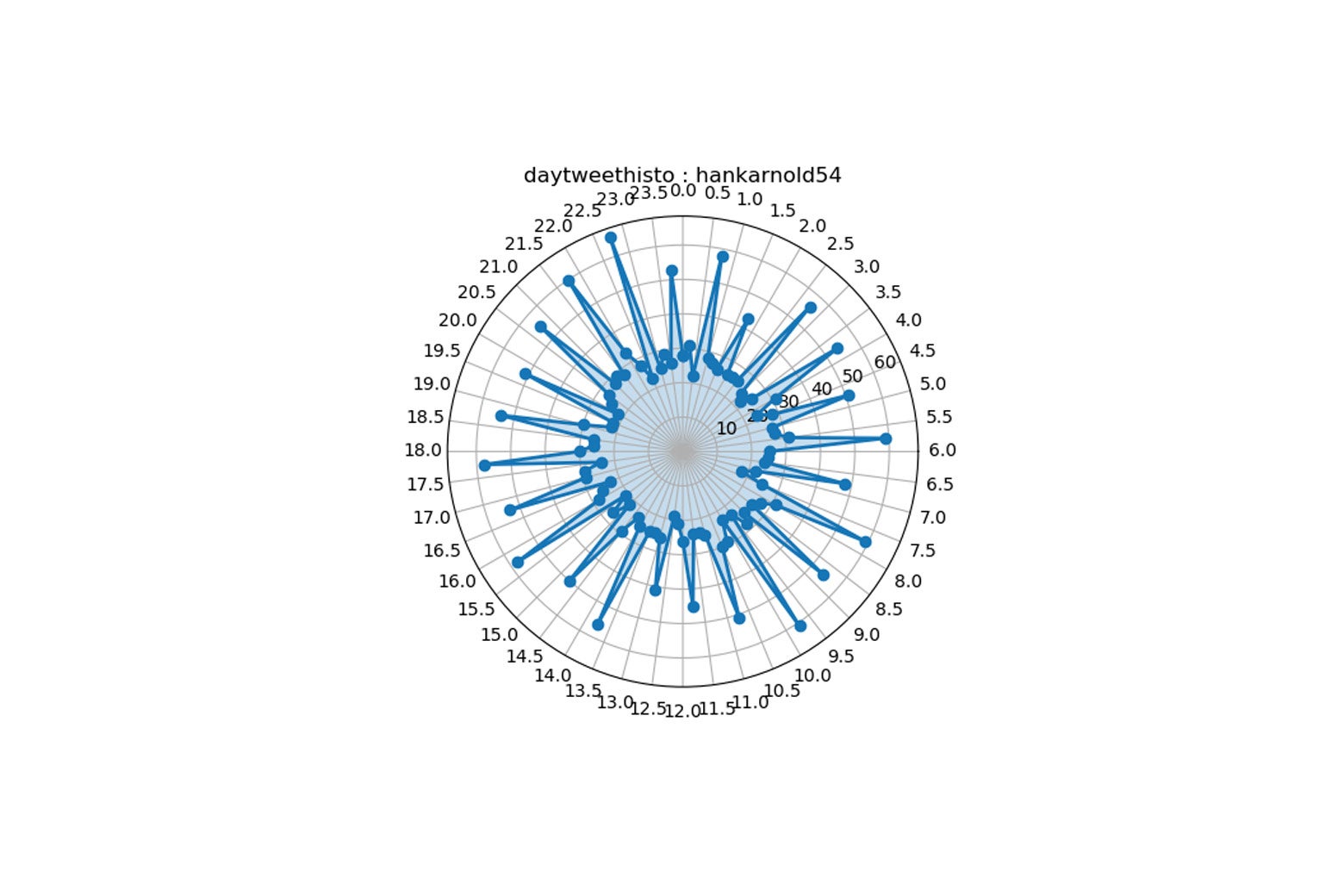
If you plot the time of the account’s tweets on a 24-hour clock (midnight at top, noon at bottom), you see that it never seems to sleep, and its predilection for posting on the half-hour makes a sunburst pattern. I’m very comfortable saying this is a bot. (I tweeted to ask but have received no response, even as the account continued to post right-wing news.)
Compare that to a typical humanoid—such as me. Below, you can see a seven-to eight-hour period when I stop my online activity, and you can tell that my sleep pattern is pretty normal.
Sayoc’s sleep pattern was apparently not ordinary; the carve-out in his daily clock is quite short and in the wrong place. It looks like Sayoc wasn’t getting much sleep, and when he did, it was in the middle of the day.
And, on the other hand, a bot can pretend to sleep, and a lot of bots, in fact, have a diurnal pattern. In many cases, they seem more natural than Sayoc’s.
«
I like the polar plot – a clever way to visualise it. He also looks at “time between tweets” – another element you’d think would be a giveaway. Not so.
link to this extract
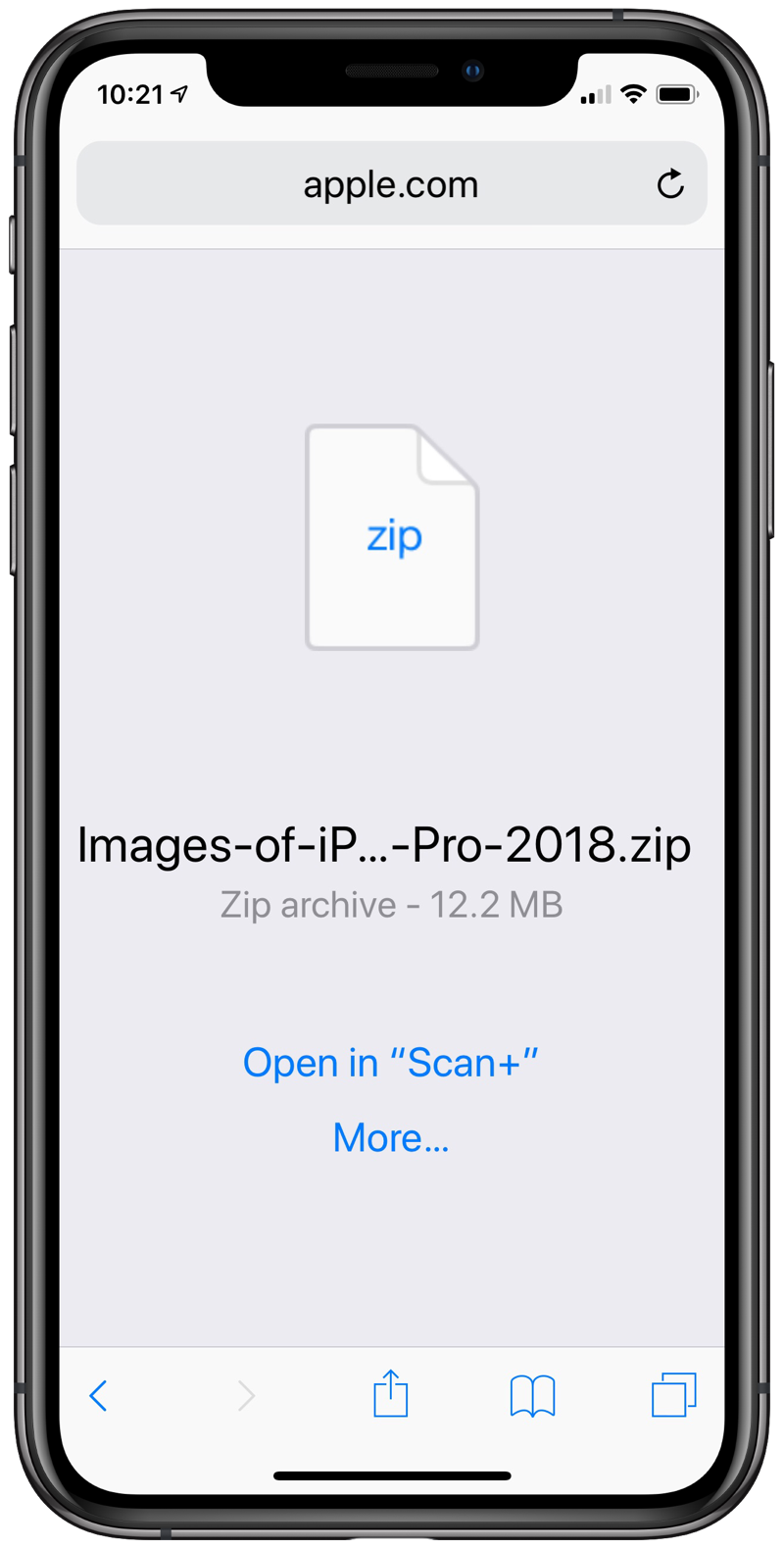
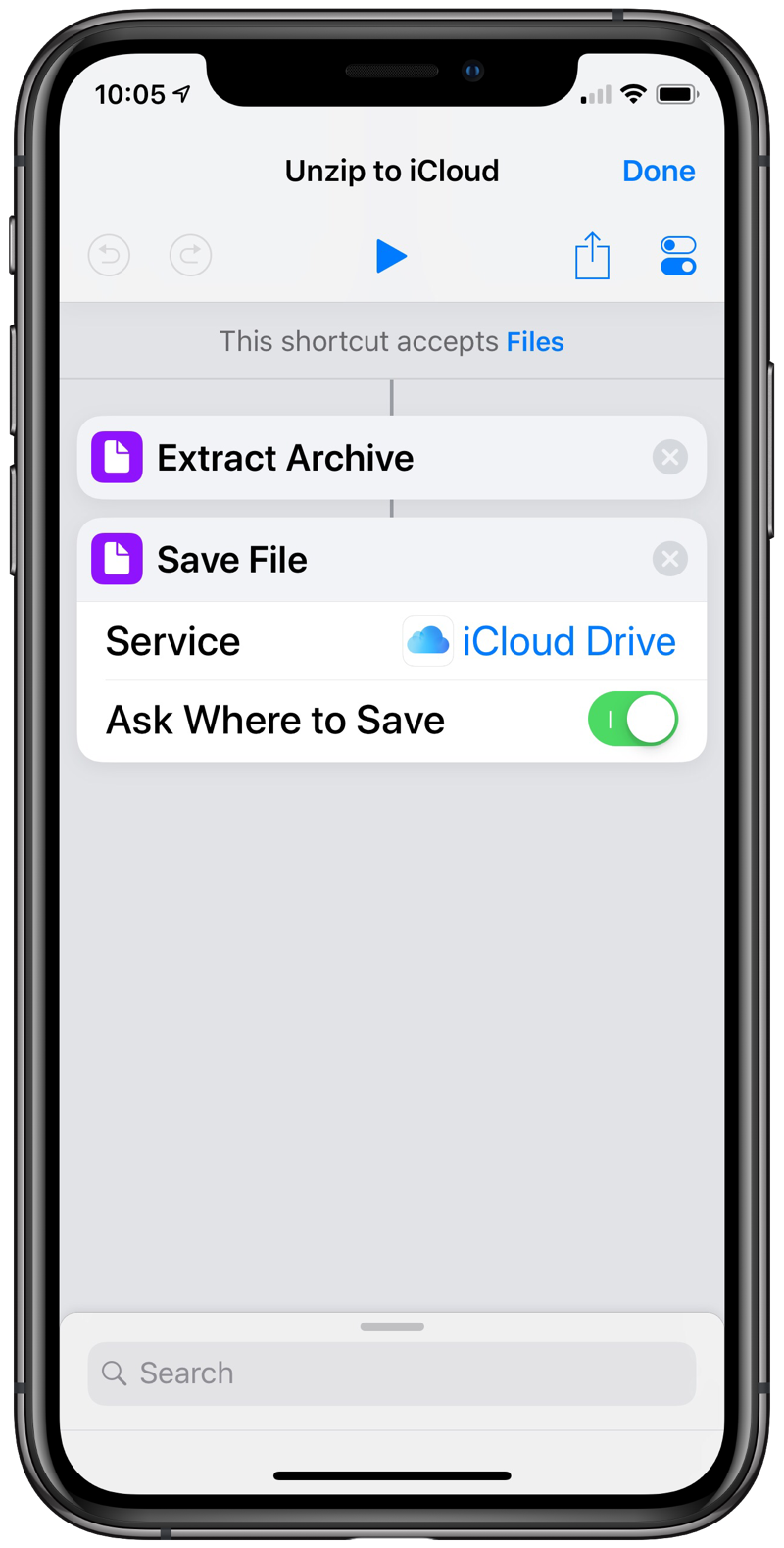
An unzipping shortcut • All this
Dr Drang (who works in engineering, usually calculating how to stop bridges falling down, etc) likes noodling with scripts; here he tackles a problem many people face: how do you handle ZIP files on iOS?
»
Apple provides the product images as zipped archives, so when I clicked on the link in the press release, I was confronted with this “what do I do?” screen in Safari.
The efficient thing would have been to walk ten feet over to my iMac and download the zip files there, where they can be expanded with almost no thought. But I took the procrastinator’s way out, deciding to solve the problem of dealing with zip files on iOS once and for all.
In the past, I’ve tried out a few zipping/unzipping apps, and they’ve all sucked, with user interfaces that are clumsy to navigate and look like something out of Windows 3.1. What I wanted was a clean, one-click solution similar to what we have on a Mac. A shortcut, if you will…
I went to the Shortcuts Gallery and searched on “zip,” “unzip,” and “archive.” There was a shortcut for zipping up a bunch of files and putting them into an email message, but nothing for unzipping and saving. I also couldn’t find anything by Googling. So I made my own.
«
It will take you 30 seconds to write this Shortcut, perhaps less to download it from him. Anyway, that’s another obstacle to “real work” solved.
link to this extract
The US is in a state of perpetual minority rule • The Washington Post
Daniel Markovits and Ian Ayres (who teach law, economics and politics at Yale Law School) on the inbuilt bias of the state-oriented, first-past-the-post system in the US:
»
The electoral college system extends these biases into presidential elections. Donald Trump himself also lost the popular vote — by 2 percentage points, or nearly 3 million votes — in 2016. This difference represents the greatest popular-vote loss suffered by any winning president in history.
President Trump and the Republican senators have used their offices to remake the judiciary in their own image. Justices Neil M. Gorsuch and Brett M. Kavanaugh entrench a reliable conservative majority at the Supreme Court, in spite of being nominated by a popular-vote-losing president and confirmed by senators who, our research shows, collectively won (in each case) about 24 million fewer votes than the senators who voted against the nominations.
All in all, then, a Democratic Party that has dominated the popular vote across all federal offices enjoys only a narrow elective majority in one half of one branch of the federal government. And Trump and Republican senators are using their control of the rest of the government to promote policies that will extend and entrench the Republican skew in elections. The Supreme Court will likely soon hear a series of cases in election law that review the very practices that underwrite Republican power.
Finally, these patterns follow a dark demographic logic. White men — roughly one-quarter of the total US population — constitute Trumpism’s core constituency. Exit polls showed they favoured Trump over Hillary Clinton by 62% to 31% and favoured Republicans over Democrats in this year’s midterms by 60% to 39%. No other major demographic group supports the Trump agenda with anything approaching this enthusiasm. We’ve estimated that if white men voted like the rest of America, Democrats would have won the 2016 presidential election by 19% and would, following the midterms, control a majority of the Senate with at least 20 more seats.
«
The urban-rural divide in the US is going to create increasing rifts unless the US revises its representation system. That Wyoming, with fewer than 600,000 inhabitants, sends as many senators as California, with 37m, is crazy. Reform might even allow a third party to emerge and influence change.
link to this extract
Getting the iPad to Pro • Craig Mod
»
Let’s assume — as all the marketing seems to imply — that Apple wants us to treat these machines as primary computers. And assume we’re professional computer folk, who do complicated computer things. [Footnote: I would not be surprised to see iPads run both iOS and macOS, and switch between OSes when plugged into external monitors, thus fixing the weird UX snafu of touchscreen on a screen without touch.]
Having used the heck out of iPads these past few years, I believe there are two big software flaws that both make iOS great, and keep it from succeeding as a “pro” device: [Footnote: Contrary to a lot of complaints I see about iPads, I don’t find the lack of a track pad / pointer to be an issue. Touch / Pencil and a Smart Keyboard have worked really well for me.]
1. iOS is primarily designed for — and overly dependent on — single-context computing
2. Access to a lower level (i.e., a file-like system) components is necessary for professional edge-tasksAnd one big general flaw that keeps it from being superb:
1. Many software companies still don’t treat the iPad as a first class computing platform [Footnote: Including Apple! I asked for (the quite excellent) archive of all the data Apple has collected about me (fascinating, well-structured, illuminating, worth retrieving) and, when my archive was ready, upon visiting the archive download page on an iPad was told: This device is not supported.]
Let’s dig into real-world examples of where these issues present problems…
«
Excellent piece.
link to this extract
CNN headlines, according to a neural net • Letting neural networks be weird
»
After much more training (about 30 min total on a fast GPU), it grew confident enough to use actual words more often. It had learned something about business as well.
Why the Stock Market is Trying to Get a Lot of Money
The US China Trade War is so Middle Class
Bank of the Stock Market is Now Now the Biggest Ever
The Best Way to Avoid Your Money
How Much You Need to Know About the New York City
How to Make a New Tax Law for Your Boss
The Stock Market Market is the Most Powerful Money
Goldman Sachs is a New Super Bowl
Facebook is Buying a Big Big Deal
Why Apps in the Country
5 Ways to Trump on Chipotle Industry is the Random Wedding
Premarket Stocks Surge on Report of Philadelphia Starbucks Starbucks StarbucksOne curious pattern that emerged: companies behaving badly.
Walmart Grilled With a New Leader in Murder Tech
Coca-Cola is Scanning Your Messages for Big Chinese Tech
Amazon Wants to Make Money Broadcasting from Your Phone
Should I Pay My Workers
Amazon is Recalling 1 Trillion JobsMy favorite headlines, though, were the most surreal.
Star Wars Episode IX Has New Lime Blazer
Mister Rogers in Washington
Black Panther Crushes the iPhone XS and XS Max Max
How to Build a Flying Car Car
You Make Doom Stocks
The Fly Species Came Back to Life
India Gets a Bad Mocktail Non Alcoholic Spirit
How to Buy a Nightmare«
I think “Star Wars Episode IX Has New Lime Blazer” is my favourite because I feel pretty sure I’ve read it somewhere. Next train it on clickbait? Speaking of which…
link to this extract
Meeting Kosovo’s clickbait merchants • BBC News
Carl Miller spoke to Kosovan fake news generators a year ago; now he has gone back to see how the crackdown by Facebook et al is going:
»
although less profitable, the practice was still widespread. “Forty% of Kosovan youth are doing this,” one merchant told me. “Thousands upon thousands,” said another.
And it’s little wonder. 100 euros a day is still life-changing for someone, like him, who’d earned seven euros a day as a waiter before he started. The “why” was clear. In the face of Facebook’s reforms, the bigger surprise was “how”.
There is another side to this fake news and clickbait industry that isn’t visible to us. I learned that a network of closed groups exist, with memberships that can number from a few hundred to several thousand. To be part of such a closed group, you have to be invited.
But inside, it was clear that Facebook wasn’t just the place where they harvested audiences. It was also where the fake news merchants themselves traded with each other.
I saw Facebook pages with hundreds of thousands of likes traded for thousands of dollars. Others sold fake likes, or fake accounts, or offered advice on how to get around Facebook’s enforcement.
We even found a “fake news starter pack” for a beginner, complete with a collection of Facebook pages to gather an audience, along with websites to monetise your activity. This was a service sector economy for misinformation.
It wasn’t just Facebook that was innovating, the misinformation merchants were too. Some were specialised in growing pages and selling them on. Others would sell content, and more still concentrated on getting around Facebook’s enforcement.
Even within small groups, this was happening routinely and dozens of times a day. It was industrial-scale gaming of Facebook’s policies and systems.
Around the world, there are thousands of people like those I spoke to. Usually young, male and digitally savvy, they are willing to share any content for the clicks. And in the chase for clicks online, the horrifying, shocking, exaggerated, or divisive wins out again and again.
«
Why PC builders should stock up on components now • PCMag UK
»
NZXT is a popular PC desktop case vendor, but the California-based company recently had to raise its prices.
The reason? The new US tariffs on Chinese imports includes PC cases. In September, the Trump administration imposed the 10% duty, which also cover motherboards, graphics cards, and CPU coolers from the country. As a result, NZXT had to introduce a 10% price increase on PC cases to deal with the added costs, VP Jim Carlton told PCMag in an interview.
And building a PC could get even more expensive in 2019; US tariffs on Chinese-made goods will rise from 10% to 25% in January.
“If I needed to build a system in the next six months, I’d definitely build it before the end of the year,” Carlton told us.
For PC builders, the tariffs risk adding a few hundred dollars to the total cost of components for a custom desktop. “If it’s a $2,000 purchase on 25% tariffs, it’s going to be a $2,500 purchase,” Carlton said. “So we are very concerned with the direction of where this is going.”
“I don’t have a 10% [profit] margin I can just throw away and absorb the tariffs,” he added. “And certainly no one has a margin for 25%.”
But retail consumers won’t be the only buyers affected by the tariffs. MBX Systems is another US provider of hardware systems, which focuses on enterprise customers. The Illinois-based company specializes in assembling servers, which are then resold by its clients, such as cybersecurity firms.
Last month, the company told its customers the bad news; more than 30 component suppliers—including Intel, Samsung, and Seagate—had been affected by the tariffs, forcing server component costs to go up.
“We’ve seen anywhere from reluctant acceptance by the customer—where they’re not going to increase the cost to the end user—to others that will push back heavily,” MBX Systems president Chris Tucker told PCMag.
«
Looking outside China doesn’t help: manufacturing prices are higher.. by at least the tariff amount. Trade wars: not so easy to win.
link to this extract
Researchers claim to have permanently neutralized ad-blocking’s most promising weapons • Boing Boing
»
Last year, Princeton researchers revealed a powerful new ad-blocking technique: perceptual ad-blocking uses a machine-learning model trained on images of pages with the ads identified to make predictions about which page elements are ads to block and which parts are not.
However, a new paper from a group of Stanford and CISPA Helmholtz Center researchers reveals a powerful machine learning countermeasure that, they say, will permanently tilt the advantage toward advertisers and away from ad-blockers.
The team revealed a set of eight techniques to generate adversarial examples of slightly modified ads that completely flummoxed the perceptual ad-blocker’s model: from overlaying a transparent image to modifying a few pixels in the logo used to demarcate an ad.
What’s more, the team showed that they could cause the perceptual blocker’s model to erroneously identify a page’s actual content as an ad and block it, while leaving the ads unblocked.
The team says that these techniques will always outrace the ability of perceptual blocking models to detect them, suggesting that perceptual blocking may be a dead letter.
«
Dead letter? Dead end maybe. Please now view this advert for “arms race”.
link to this extract
Facebook Portal non-review: why I didn’t put Facebook’s camera in my home • WSJ
Joanna Stern refused to review the Portal in her house, citing privacy concerns, though she did use it in the office:
»
When I asked about the popular Facebook mic conspiracy, Mr. Bosworth assured me that “it is not true, it will continue to not be true.” On the Portals, specifically, he made a number of privacy and security assurances:
• You can disable the camera and microphone by pressing the button on top of the device. This physically disconnects them so even if the Portal were hacked, they wouldn’t be accessible.
• As an added measure, you can block the camera lens with an included plastic camera cover.
• All the smart-camera technology—the person detection, etc.—happens locally on Portal, not on Facebook servers. Portal’s camera doesn’t use facial recognition to identify people on the call.
• Like all Messenger calls and messages, all communications are encrypted.
• Like Amazon Echo or Google Home, Portal only sends voice commands to Facebook servers after you say, “Hey Portal.” You can delete Portal’s voice history in your Facebook Activity Log.However, because this is using Facebook Messenger, the data that is typically collected from a call is still collected. That includes your call history, how long you spent talking to certain contacts, etc. Also, the sheer use of the device indicates to Facebook you’re interested in video calling, so you may be targeted for that. Speaking of ads, Facebook said there are no ads on the Portal’s screen, and the company doesn’t have plans to show ads there.
Facebook’s Promise: The Portal was designed so you’re always in control of your privacy and security.
My Assessment: It’s hard to believe we really have any control of our Facebook data and privacy given the last year.
«
Facebook execs are clearly sincere about their desire to make the Portal private. But it’s the scorpion riding on the frog’s back: it’ll sting you somehow eventually. That’s just its nature. At the same time, the technology is smart. But will the people who can afford it be the ones prepared to let go of their privacy?
link to this extract
Apple pumps up its Amazon listings with iPhones, iPads and more • CNET
»
Amazon has signed a deal to expand the selection of Apple products on its sites worldwide.
The world’s largest e-commerce company said Friday it’ll soon start selling more Apple products directly and have access to Apple’s latest devices, including the new iPad Pro, iPhone XR, iPhone XS, and Apple Watch Series 4, as well as Apple’s lineup of Beats headphones. The Amazon-Apple deal encompasses the US, UK, France, Germany, Italy, Spain, Japan and India, with the new products hitting Amazon sites in the coming weeks.
Only Apple-authorized resellers will now be allowed to sell Apple and Beats products on Amazon’s marketplace.
Currently, many of these Apple products are either unavailable on Amazon or are on sale only through its third-party marketplace at varied prices and conditions. Amazon does already directly sell some Apple devices, such as MacBook laptops and Beats headphones.
«
Pull in those marginal sales at a time when things might be getting tough.
link to this extract
Creation and consumption • Benedict Evans
»
It seems to me that when people talk about what you ‘can’t’ do on a device, there are actually two different meanings of ‘can’t’ in computing. There is ‘can’t’ as meaning the feature doesn’t exist, and there is ‘can’t’ as meaning you don’t know how to do it. If you don’t know how to do it, the feature might as well not be there. So, there is what an expert can’t do on a smartphone or tablet that they could do on a PC. But then there are all of the things that a normal person (the other 90% or 95%) can’t do on a PC but can do on a smartphone, because the step change in user interface abstraction and simplicity means that they know how to do it on a phone and didn’t know how to do it on a PC. That is, the step change in user interface models that comes with the shift from Windows and Mac to iOS and Android is really a shift in the accessibility of capability. A small proportion of people might temporarily go from can to can’t, but vastly more go from can’t to can.
Meanwhile, while there are 1.5bn PCs, many of them shared, there are today around 3bn smartphones, and this will rise to 5bn or more in the next few years, out of 5.5bn people on Earth aged over 14… the price and distribution of smartphones means that billions more people will use smartphones for something than ever used a PC for anything at all.
So, 100m or so people are doing things on PCs now that can’t be done on tablets or smartphones. Some portion of those tasks will change and become possible on mobile, and some portion of them will remain restricted to PCs for a long time. But there are another 3bn people who were using PCs (but mostly sharing them) but who weren’t doing any of those things with them, and are now doing on mobile almost all of the stuff that they actually did do on PCs, plus a lot more. And, there’s another 2bn or so people whose first computer of any kind is or will be a smartphone. ‘Creation on PC, consumption on mobile’ seems like a singularly bad way to describe this: vastly more is being created on mobile now by vastly more people than was ever created on PCs.
«
Errata, corrigenda and ai no corrida: none notified



Unzipping “Anyway, that’s another obstacle to “real work” solved.”. I chuckled. , use a real OS ? The number of limitations of iOS tha never get mentioned) is weird. Stockholm syndrome ?
If iOS is so limited and Android so powerful, why is Photoshop coming first to the iPad, not Android? Why is the discussion about “giving up your laptop” focussed on the iPad, not Android? Why do Android tablet owners like yourself pine for ChromeOS on a tablet – which Google is now offering, since Android as a tablet OS isn’t breaking down any barriers?
In the end it comes down to the developer community and the user community. The Apple developer community seems excited about the possibility of creating new workflows and paradigms with the iPad; the user community seems increasingly interested in adopting those. (Dr Drang, who is a longstanding – and very skilful – Python/Applescript user, is adopting his workflows to Pythonista/Shortcuts. And he is not just some scribbler. Look more closely at his site to realise that.)
It’s not Stockholm Syndrome – people have options besides the iPad, but they like the freedom it gives them to move around, and work in new ways, and also not to worry about viruses and so on which is an everyday concern on Windows.
It’s a different way of working from the desktop. Trying to force it to be the desktop is antiquated thinking. Desktop doesn’t have GPS, mobile connectivity, back camera, protected kernel, full sandboxing and so much else.
The discussion is limited to iOS in your bubble. In my regular-joe bubble, the PC has been replaced by Android tablets for pretty much all Home users. There wasn’t much discussion about it, it just happened. I even replaced my mom’s Windows PC with an Android desktop about a year ago, and she’s been happy with the change. Very low-needs user though.
I’m curious indeed why Android tablets aren’t taken more seriously. You’re the tech journalist + blogger, you must know, and have good objective reasons for that. If you don’t, you should, beyond “that’s what me and my friends have always used !”
I understand for specific verticals (music creation, high-end photo+video editing), iPads have advantages. I’m just not sure they’re the only game in town outside of those, not any more than iOS tablets are dominating sales as you’ve falsely claimed several times.
My basic question when I’m asked for mo’money is “what can that magical machine do that I can’t do with the sensible gear”. For tablets (and phones) , the answer is far from obvious (and that’s across both iOS vs Android and luxury vs midrange), there’s even some stuff missing at the expensive end that’s possible at the low-end and mid-end (^^). Even “boost my ego” is arguable, it only works when your peers value style and money more than common sense and knowledge.
PS: there’s plenty of Adobe apps, and MS Office, on Android too.
https://play.google.com/store/apps/collection/cluster?clp=igM4ChkKEzQ3MzQ5MTY4NTEyNzA0MTYwMjAQCBgDEhkKEzQ3MzQ5MTY4NTEyNzA0MTYwMjAQCBgDGAA%3D:S:ANO1ljLrimQ
And to be very clear, I’m not saying that Android is the only ecosystem that makes sense or that matters or that should exist (you seem to be doing that for iOS ?). I’m saying it’s the ecosystem that makes the more sense for a large majority of cases. For a variety of reasons:
– cost (it’s OK to pay more, but that shoudl enable you to do more. If it doesn’t, or if you have limited hard-ceiling’d needs spend your money elsewhere
– choice of device you might want to have cheap stuff for the kids, premium stuff for the adults, small or large, rugged of snazzy-looking, …
– and even capabilities. We got the .zip gag this week, there was another one last week, then support for mice, homescreen widgets, USB peripherals (webcams, printers, gamepads, even hard disks ain’t that crazy !)…
Android tablet can do a lot of things, some of which iPads can’t (and reciprocally, but less so ^^). A lot more people are buying and using Android tablets. You seem utterly (or willfully ?) unaware…
re. Creation and consumption. “But then there are all of the things that a normal person (the other 90% or 95%) can’t do on a PC but can do on a smartphone, because the step change in user interface abstraction and simplicity means that they know how to do it on a phone and didn’t know how to do it on a PC” Source ? A smartphone UI’s is arguably less intuitive than a PC’s. Buttons are melding into the background, un-labeled, some of the UI is hidden 2 or 3 menus deep or is just plain hidden: to take screenshot: on PC, push the Print Screen key. On Android, it’s either swipe down w/ 3 fingers, go to Quick Settings and tap ScreenShot, press Vol- + Power button, or something else. How is that “more intuitive” than pushing the Print Screen key ?
Mobile is more intuitive for some specific stuff: sharing, installing/removing apps, anything that’s in Quick Settings. But that’s it; it isn’t *generally* more intuitive, even for casual users.
And in some ways, it’s less intuitive, and getting even less so. Removing the Home and Back buttons from the bezel, then from the screen, has created issues for many of my low-techiness users. Text selection is still a pain, magnifying glass + selection handles or not; voice recog still makes more mistakes than I do if even when don’t proofread myself…
re. Apple and Amazon, Apple is also waging war against independent repairs and refurbs.
Apple has been working hard at grabbing all the revenue from their profligate customers, including repairs (which are set to rise if iDevice longevity rises). Apple has locked down their devices, parts, HW and SW/diagnostics tools, making non-Genius and non-Authorized repairs much harder, sometimes impossible.
This could be fine in theory, Apple service is a part of the Apple experience, but for 3 issues:
1- availability. If there are no Apple or Apple-Autorz’d shops near you, you’re left stranded.
2- cost. Apple-branded and Apple-Authorized repairs are significantly more expensive than sensible repairs
3- quality. Genius repairs aren’t always (usually ?) top-quality, and the criteria to be Apple-authorized are mostly financial, not qualitative (why am I not surprised).
The right-to-repair crowd -and users who want speed, self-sufficiency, and/or cost effectiveness- have been aghast and mad at Apple for a while. Those latest Amazon shenanigans are icing on the sour grapes.
Right-to repair activist and repairman extraordinaire Louis Rossmann has a rant about it, lost in a sea of “Fixing dead Macbook Pro with PP3V42_G3H missing & no magsafe light” and the like. https://www.youtube.com/watch?v=K669-vhKshU
re. Android screenshots: Anyone running a rooted Android with a custom bootloader and sideloaded apps has no right to complain about security, either ;-p
He seems competent enough to handle it. But that’s way outside the norm; Android does give regular users enough barbed wire to hang themselves with several times over. Nice of Android to let users run all those system-level audit tools though.
BTW, the Google Security Report with that 0.08% PHA figure is still available… It’s more relevant than this fun but ultimately no-meat sandwich.
PS: the whole issue might be a LineageOS-specific bug. On my Xiaomi phone, the multitasker shows a blank screenshot w/app logo for apps I’ve secured behind an individual password or touchID. No wild UI screenshots stored in the recesses of the OS.
re. The iPad as a pro tool. The conclusion nicely sums up why I think the iPad is overblown, and Android tablets unfairly dismissed. His words, my comments:
“For now, though, the iPad is still good for writing.” I’m sure. But Androids too, you even get the option of a mouse for text selection. There’s no need at all to pay $1k even $500 for text entry, even formatted-text entry.
“Amazing for sketching.” It’s probably better than Androids indeed. Some do use the Galaxy S4, many seem to prefer MS’s Surface.
“Reliable as a tank. Just don’t switch too quickly between apps.” I’m not aware of a difference of HW reliability between premium Android and iOS devices. I’m not aware of Android crashing when you switch between apps even “quickly”.
“Don’t expect your cursor to be where you think it should be.” That’s why Android’s mouse support is great: don’t expect, just set your pointer where you want it, no arm-flailing.I don’t know if Android’s cursor location is more predictable than iOS’; it certainly isn’t perfect either.
“Don’t try to do anything fancy with files.” A clear Android advantage: full old-school filesystem and all the attendant tools.
“Don’t design a book on it.”. Probably not on Android either. Not sure what that entails though.
“And don’t hope to open two documents from the same app side-by-side.”. We discussed it earlier this week: Android can do that.
I know I’m fighting windmills. But this is so obvious it’s irresistible. And I’m not randomly picking features/capabilities, this is an iFan’s conclusion on iPads.
I wrote most of a book, and did most of the revision of said book (including Track Changes), on a first-generation iPad Pro, with Pages. I didn’t design the book – next year I guess that might become a possibility.
More to the point: if Android is so superior in so many ways, why do I not see any reports *anywhere* of developers adapting their workflows so they can be free of their clunky desktops and just work on their Samsung/Huawei/Lenovo Android OS tablet? I read a lot, including a lot of Android news sites, and cross-platform developer sites, and I don’t see a *whisper* of it. Is it just happening and nobody remarks on it? Can you point to examples where people are trying to do this?
Who would want to *develop* on a tablet ? It’s… slated to become possible on chromebooks and chromebooks are supposed to take over from Android for tablets, but that’s in the future.
For writing, which seems to be this guy’s business, a quick google for “best tablets for a wrtier ” brings up a mix of just about every premium tablet, Android/iOS and Windows.
Reciprocally, if iOS is *required* to write, I’m unaware of it. What’s *your* source ?
Plus, most of the money is from iOS. We have apps installed on 60:40 split between Android and iOS yet 95-98% of our revenue comes from iOS devices.
In addition, give a kid a choice of an Android tablet or an iPad, they will grab the iPad everytime.
Personally I’ve switched from taking my laptop with me and replaced it for a 2nd Generation iPad Pro (although I would really like the new pencil and its charging capability I’ll be sticking with my existing tablet for a while). Its lighter and does everything I need to do as a reporter.
I’m sure one anecdote can serve as any data. Generally speaking, the iOS:Android revenue split is about 50:50 worldwide. iOS has 30% share in tablets instead of phones’ 15%, so I’m sure tablet apps revenue skews more iOS. But if true, that split you cite might be due to your app, your marketing… more than to the overall market.
When on holidays here, my nephews prefer the “Marseilles’ iPads” (ie, Androids) because I’ve put SD on them with oodles of kids shows, which helps at my mom’s country house whose thick walls make for bad wifi. So anecdotes are 2:2.
And as a sales/marketing exec, I’ve sometimes taken my dual-boot Android+Windows tablet instead of lugging the whole laptop. Couldn’t use any tablet ‘coz I do need the full Office. 3:3
I’m not saying iPads can’t do anything, or never make sense. I’m saying for most people they’re wildly overkill and overspend, as are other luxury tablets; that the cases for which you *need* an iPa are very specific (music creation…), and that iPad also have objective drawbacks and limitations compared to Android tablets. I’m surprised this is eliciting such pushback, anecdote-based pushback at that. We understand you got an iPad. That doesn’t make it the only, nor even the bets, game in town. People typed a novel on it. Great ! That doesn’t mean you can’t type a novel on an Android, for less money and with a pointer and external backup.
The question is: how many people do this sort of work on an Android tablet? Why don’t we see reports of this? I’m genuinely puzzled. I see people talking about Chromebooks a fair amount (eg venture capitalist Fred Wilson among others). But Android tablets seem to principally be used as you describe – dumb glass.
Interesting though partial insight on Xiaomi’s sales mix: for Diwali (India), on-line only: 6m smartphones, 2.1m other “ecosystem” stuff, and 400k TVs. That’s in a country where smartphones are still not at saturation, so higher.
https://www.gsmarena.com/xiaomi_sold_6_million_smartphones_during_diwali-news-34177.php
I’m surprised non-smartphones are that high, especially since it means they’re higher in more mature markets. I’m not sure the “ecosystem” mayonnaise is that firm, but at least their product formulation and their branding seem to be working.
Now if we could have some info on ASP… It must be fairly low for smartphone with the $100 Redmi 6A as their best-seller, so I’m not even sure it’s worse for the “non-smartphone” catch-all, which includes air purifiers, bikes/scooters.. and they have no “5% margin” policy on those.