
The bow of a Maersk container ship: the NotPetya ransomware brought the company to a dramatic halt. Photo by teralaser on Flickr.
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
A selection of 9 links for you. Honestly. I’m @charlesarthur on Twitter. Observations and links welcome.
What algorithmic art can teach us about artificial intelligence • The Verge
»
[Computational design lecturer and artist Tom] White says his motivation is primarily to deconstruct what we think of as machine perception. In other words: to explain the algorithmic gaze. Take the example of the cello print in White’s series “The Treachery of ImageNet.” If you know what you’re looking for, you can see shapes that represent the instrument (a cluster of straight parallel lines bracketed by curves). But there’s also a confusing shape looming behind it. White says these shapes are there because the algorithms were trained using pictures of cellos with cellists holding them. Because the algorithm has no prior knowledge of the world — no understanding of what an instrument is or any concept of music or performance — it naturally grouped the two together. After all, that’s what it’s been asked to do: learn what’s in the picture.
This sort of mistake is common in machine learning, and it demonstrates a number of important lessons. It shows how critical training data is: give an AI system the wrong data to learn from, and it’ll learn the wrong thing. It also demonstrates that no matter how “clever” these systems seem, they possess a brittle intelligence that only understands a slice of the world — and even that, imperfectly. White’s latest prints for the Nature Morte gallery, for example, are abstract smears of color designed to be flagged as “inappropriate content” by Google’s algorithms. The same algorithms used to filter what humans see around the world.
Still, White says that he doesn’t see his artwork as a warning. “I’m just trying to present the algorithms as they are,” he says. “But I admit it’s sometimes alarming that these machines we’re relying on have such a different take on how objects in the world are grounded.”
«
White’s original posting is on Medium.
link to this extract
Facebook finds disinformation networks tied to Iran, Russia • Ad Age
»
Facebook has closed down more than 600 accounts and pages due to malicious activity it has linked to the Russian military and Iran in yet more instances of foreign actors infiltrating the social network to spread propaganda.
On Tuesday night, Facebook convened a call with media headed by CEO Mark Zuckerberg to outline the new cases of “inauthentic” activity – accounts that conceal their true identity usually in order to influence the online discussion around politics and social causes.
Cyber security firm FireEye, which worked with the social network to investigate some of the fraudulent activity, said in a blog post that “it’s aimed at audiences in the US, UK, Latin America, and the Middle East. This operation is leveraging a network of inauthentic news sites and clusters of associated accounts across multiple social media platforms to promote political narratives in line with Iranian interests.”
«
Iran is a new one for social media.
link to this extract
Fortnite, Netflix take on Apple, Google over App Store ‘tax’ • Bloomberg
Mark Bergen and Christopher Palmeri:
»
In defense of the app store model, Apple and Google have highlighted their ability to filter out fake apps and malicious software, and to distribute apps widely. The companies handle identity and payment details, taking friction out of the sign-up process. Promotion inside their app stores can transform a company’s fortunes overnight.
Indeed, only the most-popular online services can risk not being in Apple and Google’s app stores. Skipping these powerful distribution channels is a “fool’s errand” for most publishers, according to Danielle Levitas, a senior vice president at App Annie. And few other game developers are joining Epic. Electronic Arts Inc. and Glu Mobile Inc. are sticking with their current distribution system, which includes app stores.
According to Branch co-founder Austin, this just shows how broken the system is. Most developers want to use the app stores, but some are reluctant to pay Apple and Google, so they have to take their chances on the web, he said. His firm offers software tools that let companies identify paying subscribers before directing them to their apps.
“If you’re a small up-and-coming company, you can’t really sell subscriptions on the mobile web,” he said. “By killing off the app store tax, it’d effectively reduce the last barrier for a large fraction of companies.”
«
That last quote does set it out clearly. The small companies need the app stores. The big players can ignore it, but big players were small players once. How do you set a “fair” figure for the “tax” on the subscription figure, though? And of course companies try to find ways around it – because for subscriptions they can. (Amazon on Kindle purchases, Netflix for its subs.)
link to this extract
The desperate quest for genomic compression algorithms • IEEE Spectrum
Dmitri Pavlichin and Tsachy Weissman:
»
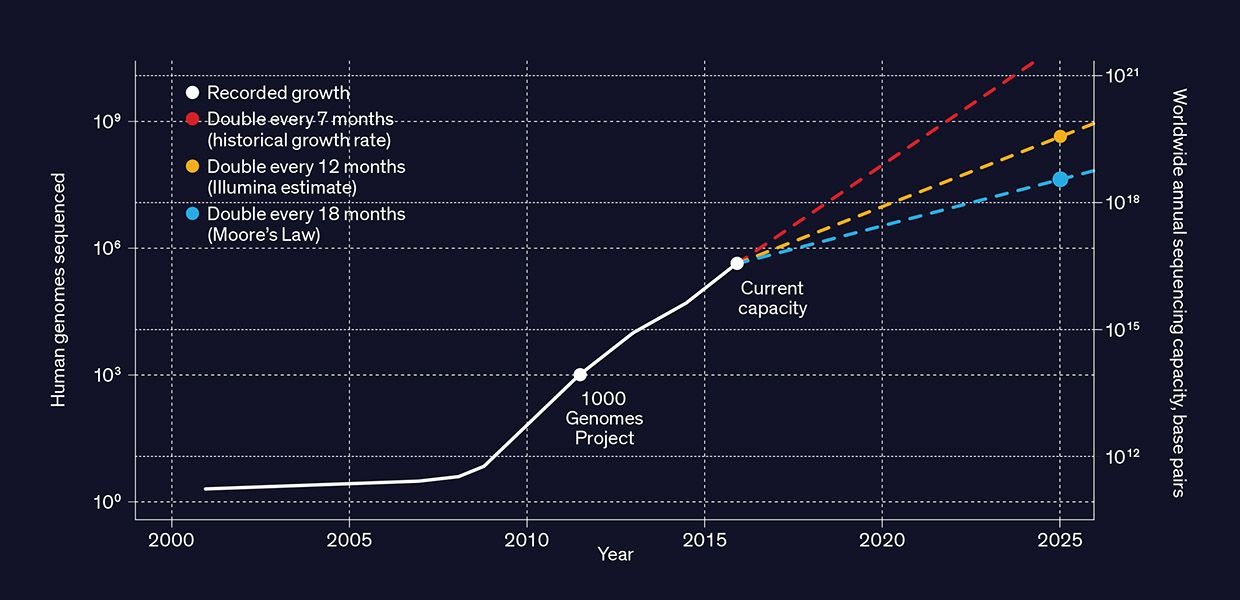
Scientists, physicians, and others who find genomic data useful aren’t going to stop at sequencing each individual just once [PDF]—in the same individual, they’ll want to sequence multiple cells in multiple tissues repeatedly over time. They’ll also want to sequence the DNA of other animals, plants, microorganisms, and entire ecosystems as the speed of sequencing increases and its cost falls—it’s just US $1,000 per human genome now and rapidly dropping. And the emergence of new applications—and even new industries—will compel even more sequencing.
While it’s hard to anticipate all the future benefits of genomic data, we can already see one unavoidable challenge: the nearly inconceivable amount of digital storage involved. At present the cost of storing genomic data is still just a small part of a lab’s overall budget. But that cost is growing dramatically, far outpacing the decline in the price of storage hardware. Within the next five years, the cost of storing the genomes of billions of humans, animals, plants, and microorganisms will easily hit billions of dollars per year. And this data will need to be retained for decades, if not longer.
Compressing the data obviously helps. Bioinformatics experts already use standard compression tools like gzip to shrink the size of a file by up to a factor of 20. Some researchers also use more specialized compression tools that are optimized for genomic data, but none of these tools have seen wide adoption. The two of us do research on data compression algorithms, and we think it’s time to come up with a new compression scheme—one that’s vastly more efficient, faster, and better tailored to work with the unique characteristics of genomic data. Just as special-purpose video and audio compression is essential to streaming services like YouTube and Netflix, so will targeted genomic data compression be necessary to reap the benefits of the genomic data explosion.
«
Can’t really “compress” it by listing it as proteins. (Or could you? I think not because long stretches are just nonsense.)
link to this extract
Synthestech offers “cold transmutation” alchemy on the blockchain. Plus UFOs • Attack of the 50 Foot Blockchain
David Gerard keeps watch on the various cryptocurrency goings-on:
»
The Bitcoin bubble is deflating, and there aren’t nearly enough suckers desperate to put their money into anything with the word “crypto” attached.
So for Synthestech’s ICO, they’ve decided to go big or go home:
»
DISRUPTIVE INNOVATION TECHNOLOGY FOR ARTIFICIAL SYNTHESIS OF PLATINUMWe are developing the most significant innovation of century. We use Cold Fusion phenomenon for transmutation of cheap elements into valuable elements and isotopes
«
Yep — it’s an ICO for alchemy.
«
Cold fusion plus crypto. Oh yes.
link to this extract
The untold story of NotPetya, the most devastating cyberattack in history • Wired
»
“Henrik Jensen” [not his real name] was busy preparing a software update for Maersk’s nearly 80,000 employees when his computer spontaneously restarted.
He quietly swore under his breath. Jensen assumed the unplanned reboot was a typically brusque move by Maersk’s central IT department, a little-loved entity in England that oversaw most of the corporate empire, whose eight business units ranged from ports to logistics to oil drilling, in 574 offices in 130 countries around the globe.
Jensen looked up to ask if anyone else in his open-plan office of IT staffers had been so rudely interrupted. And as he craned his head, he watched every other computer screen around the room blink out in rapid succession.
“I saw a wave of screens turning black. Black, black, black. Black black black black black,” he says. The PCs, Jensen and his neighbors quickly discovered, were irreversibly locked. Restarting only returned them to the same black screen.
All across Maersk headquarters, the full scale of the crisis was starting to become clear. Within half an hour, Maersk employees were running down hallways, yelling to their colleagues to turn off computers or disconnect them from Maersk’s network before the malicious software could infect them, as it dawned on them that every minute could mean dozens or hundreds more corrupted PCs. Tech workers ran into conference rooms and unplugged machines in the middle of meetings. Soon staffers were hurdling over locked key-card gates, which had been paralyzed by the still-mysterious malware, to spread the warning to other sections of the building.
Disconnecting Maersk’s entire global network took the company’s IT staff more than two panicky hours. By the end of that process, every employee had been ordered to turn off their computer and leave it at their desk. The digital phones at every cubicle, too, had been rendered useless in the emergency network shutdown.
Around 3 pm, a Maersk executive walked into the room where Jensen and a dozen or so of his colleagues were anxiously awaiting news and told them to go home. Maersk’s network was so deeply corrupted that even IT staffers were helpless.
«
From a forthcoming book by Greenberg about NotPetya, called “Sandworm”.
link to this extract
Flipkart acquires speech recognition start-up Liv.ai • Financial Times
»
The buyout reflects a growing consensus among ecommerce executives that strong growth will require a broadening of the market beyond English-speaking, relatively prosperous Indians who already do some shopping online.
Kalyan Krishnamurthy, Flipkart chief executive, said that “the next wave of growth of internet users” was coming from beyond India’s major cities. He added that most of these new users would want to access online services in vernacular languages — which most would never before have written using a keyboard.
“Given the complexities in typing on vernacular keyboards, voice will become a preferred interface for new shoppers,” he said.
A joint report this month by Bain & Company, Google and Omidyar Network found that only 40% of India’s 390m internet users made any transactions online, with this group skewed overwhelmingly towards higher-income people.
Analysts say this is partly a reflection of the fact that Indian ecommerce offerings have failed to keep up with a shift in the country’s online demographics beyond the fluent English speakers who were first to get online.
KPMG estimates that in 2011, there were 68m Indian web users who were comfortable using English, against 42m who preferred using a local language. By 2016, the latter group outnumbered English speakers 234m to 175m. And in 2021, KPMG forecast, there would be 536m local language speakers online, against 199m English speakers.
«
Significant point: in developing countries, voice is already the prime method for search, and can be for shopping too.
link to this extract
How misinformation spreads on Line — one of the most popular messaging apps in Southeast Asia • Poynter
»
Line has about 170 million monthly active users in its four main markets and is among the most popular messaging apps in countries like Thailand, Indonesia and Taiwan. While it’s similar to other messaging platforms, Line has a more exhaustive array of features, such as separate sections for news, ordering taxis, mobile payments and music streaming. The app makes money by selling stickers and advertising.
And, like both WhatsApp and WeChat, the peer-to-peer messaging environment can be taken advantage of by fake news writers, hoaxers and scammers.
“It’s a kind of complex thing as a mixture of misinformation, phishing, scamming, bad advertising and monetization,” Anutarasoat said of accounts that dabble in misinformation. “What people are sharing the most is about health.”
Those types of stories directly target an older demographic that might be less likely to discern between credible and bunk health information on Line, Anutarasoat said.
“Old people are solely on Line because they do not use Facebook much,” he said. “And those people, they are in the stage where their friends are deceased (and they’re) facing health problems, so I think it also drives the content network to target them and sell something like health products.”
Accounts similar to Knowledge Treasury, such as “GINZEN take care of health” and “GINZEN omni-knowledge about health” (roughly translated), get so big that they advertise bogus health brands. Both have more than 850,000 subscribers and “Ginzen” — an herbal supplement that promises to solve “chi and yin deficiency” — in their account names. Poynter reached out to both on Line but had not heard back as of publication.
«
Apple to gain unconditional EU approval for Shazam buy: sources • Reuters
»
Apple is set to win unconditional EU antitrust approval for its planned acquisition of British music discovery app Shazam, two people familiar with the matter said on Wednesday.
The deal, announced in December last year, would help the iPhone maker better compete with Spotify, the industry leader in music streaming services. Shazam identifies songs when a smartphone is pointed at an audio source.
The European Commission opened a full-scale investigation into the deal in April, emblematic of its recent worries that companies may buy a data-rich rival to mine it for information or drive others out of the market.
The EU antitrust authority said it was concerned that the Shazam deal might give Apple an unfair advantage in poaching users from its rivals.
It also cited worries about Apple possibly halting referrals from Shazam to rivals of Apple Music, the second-largest music streaming service in Europe.
«
So does that mean it thinks Apple won’t be able to poach users from Spotify, or what?
link to this extract
Errata, corrigenda and ai no corrida: none notified


re: Shazam: It means the EU doesn’t think Apple buying Shazam threatens the free market (in music subs/distribution I assume, not in music identification), either because Apple is far from a monopoly in that space, or because Shazam won’t make much of a difference. Or both.
It doesn’t mean “Apple won’t be able to poach users from Spotify”. That’s none of the EU’s business/concern.