A symphony orchestra: the apotheosis of synchrony in technology? Photo by Grant Williamson on Flickr.
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
A selection of 10 links for you. Use them wisely. I’m @charlesarthur on Twitter. Observations and links welcome.
The web’s recommendation engines are broken. Can we fix them? • WIRED
»
Today, recommendation engines are perhaps the biggest threat to societal cohesion on the internet—and, as a result, one of the biggest threats to societal cohesion in the offline world, too. The recommendation engines we engage with are broken in ways that have grave consequences: amplified conspiracy theories, gamified news, nonsense infiltrating mainstream discourse, misinformed voters. Recommendation engines have become The Great Polarizer.
Ironically, the conversation about recommendation engines, and the curatorial power of social giants, is also highly polarized. A creator showed up at YouTube’s offices with a gun last week, outraged that the platform had demonetized and downranked some of the videos on her channel. This, she felt, was censorship. It isn’t, but the Twitter conversation around the shooting clearly illustrated the simmering tensions over how platforms navigate content : there are those who hold an absolutist view on free speech and believe any moderation is censorship, and there are those who believe that moderation is necessary to facilitate norms that respect the experience of the community.
As the consequences of curatorial decisions grow more dire, we need to ask: Can we make the internet’s recommendation engines more ethical? And if so, how?
Finding a solution begins with understanding how these systems work, since they are doing precisely what they’re designed to do. Recommendation engines generally function in two ways. The first is a content-based system. The engine asks, is this content similar to other content that this user has previously liked? If you binge-watched two seasons of, say, Law and Order, Netflix’s reco engine will probably decide that you’ll like the other seventeen, and that procedural crime dramas in general are a good fit. The second kind of filtering is what’s called a collaborative filtering system. That engine asks, what can I determine about this user, and what do similar people like? These systems can be effective even before you’ve given the engine any feedback through your actions.
«
DiResta is a terrific follow on Twitter. Anyhow, today we’ve got some more recommendation engine stories below. Think of it as accidental ironic commentary.
link to this extract
The symphony orchestra and the Industrial Revolution • Marginal REVOLUTION
»
I heard Mozart’s 39th symphony in concert last night, and it occurred to me (once again) that I also was witnessing one of mankind’s greatest technological achievements. Think about what went into the activity: each instrument, developed eventually to perfection and coordinated with the other instruments. The system of tuning and the underlying principles of the music. The acoustics of the music hall. The sheet music on paper and the musical notation. All of those features extremely well coordinated with the kind of compositional talent being produced in Central and Western Europe from say 1710 to 1920. And by the mid-18th century most of the key features of this system were in place and by the early 19th century they were more or less perfected.
Sometimes I think of the Industrial Revolution as fundamentally a Cultural Revolution. The first instantiation of this Cultural Revolution maybe was the rise of early Renaissance Art in Italy and in the Low Countries. That too was based on a series of technological developments, including improved quality tempera paint, the development of oil painting, the resumption of bronze and marble techniques for sculpture, and the reintroduction of paper into Europe, which enabled artists’ sketches and drawings.
«
So much of this is what Steven Johnson calls “adjacent technology” – that you can’t move wholesale to new tech. You can’t build a nuclear reactor without having special steelmaking techniques (radioactive water does odd things). You can’t build commercial aircraft without special aluminium-forging methods, which implies huge amounts of electricity to make the aluminium, which implies…
Once you start thinking about it, it’s astonishing how far we have come in just a few thousand years.
link to this extract
Suspicious event hijacks Amazon traffic for two hours, steals cryptocurrency • Ars Technica
»
Amazon lost control of a small portion of its cloud services for two hours on Tuesday morning when hackers exploited a known Internet-protocol weakness that allowed them to redirect traffic to rogue destinations. By subverting Amazon’s domain-resolution service, the attackers masqueraded as cryptocurrency website MyEtherWallet.com and stole about $150,000 in digital coins from unwitting end users. They may have targeted other Amazon customers as well.
The incident, which started around 6 AM California time, hijacked roughly 1,300 IP addresses, Oracle-owned Internet Intelligence said on Twitter. The malicious redirection was caused by fraudulent routes that were announced by Columbus, Ohio-based eNet, a large Internet service provider that is referred to as autonomous system 10297. Once in place, the eNet announcement caused Hurricane Electric and possibly other peers of eNet to send traffic over the same unauthorized routes. Amazon and eNet officials didn’t immediately respond to a request to comment.
The highly suspicious event is the latest to involve Border Gateway Protocol, the technical specification that network operators use to exchange large chunks of Internet traffic. Despite its crucial function in directing wholesale amounts of data, BGP still largely relies on the Internet-equivalent of word of mouth from participants who are presumed to be trustworthy. Organizations such as Amazon whose traffic is hijacked currently have no effective technical means to prevent such attacks.
«
The internet’s fragility is well-hidden, but plenty of people know how to exploit it.
link to this extract
Watches, not phones, fuel Verizon’s subscriber growth • Bloomberg
»
Smartwatches, meanwhile, have helped bring another source of revenue to the industry — even if the devices aren’t as lucrative as phones. The latest wearable devices, such as the Apple Watch Series 3, have their own network connections. That means they don’t need to link up with smartphones to communicate and – good news for carriers – require a separate wireless subscription.
Verizon added about 359,000 subscribers last quarter who are using watches, wearables and other devices. That helped make up for the loss of 24,000 phone customers and 75,000 tablet customers in the period. But watch customers pay $10 a month, compared with the $40 or more that phone customers typically shell out.
That effect was evident in Verizon’s wireless service revenue, which fell 2.4% last quarter.
Verizon’s FiOS landline service, meanwhile, added 66,000 internet customers in the first quarter. But it lost 22,000 TV subscribers.
«
Wonder how many of those 359,000 subscriber adds were Apple Watch users, compared to Samsung or others. The lost tablet customers is a big number, too.
link to this extract
Facebook has hosted stolen identities and social security numbers for years • Motherboard
Lorenzo Franceschi-Bicchierai:
»
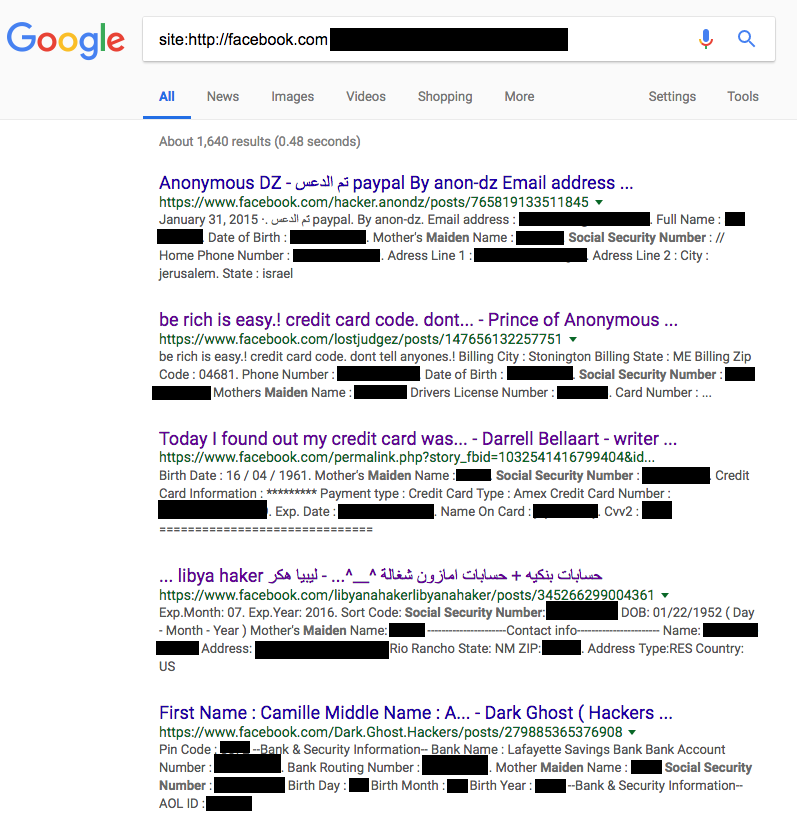
Cybercriminals have posted sensitive personal information, such as credit card and social security numbers, of dozens of people on Facebook and have advertised entire databases of private information on the social platform. Some of these posts have been left up on Facebook for years, and the internet giant only acted on these posts after we told it about them.
As of Monday, there were several public posts on Facebook that advertised dozens of people’s Social Security Numbers and other personal data. These weren’t very hard to find. It was as easy as a simple Google search.
A screenshot of the redacted Google search results for social security numbers on Facebook.
Most of the posts appeared to be ads made by criminals who were trying to sell personal information. Some of the ads are several years old, and were posted as “public” on Facebook, meaning anyone can see them, not just the author’s friends.Independent security researcher Justin Shafer alerted Motherboard to these posts Monday.
“I am surprised how old some of the posts are and that it seems Facebook doesn’t have a system in place for removing these posts on their own,” Shafer told Motherboard in an online chat. “Posts that would have words flagged automatically by their system.”
«
Comment from editor-in-chief Jason Koebler:
»
“Sick of a) having journalists have to moderate social media platforms for the giant companies that run them b) getting no response to request for comment on things that are illegal/break TOS but having the companies delete them before we run an article.”
«
Facebook and Google: skip the F8 and I/O infomercials; fix your problems • Buzzfeed
»
If the platforms are serious about healing themselves, you should be able to see it in a show that’s more about fixing what’s broken rather than building something new. And if they aren’t serious? Expect the same shiny, happy-fun wow-fests. If the onstage apology is shorter than the post-show afterparty, it will make clear that the contrition tours of 2017 and 2018 have been little more than lip service, and we can expect more of the same old fuckups and same old promises to do better.
In 2018 spending millions on rah-rah promotional spectacles for platforms like Facebook’s and Google’s is particularly unseemly when set against the conga line of travesties they’ve enabled.
What might 2019 look like if instead of dumping a manure spreader of money to rent out Mountain View, California’s cavernous Shoreline Amphitheatre and trick it out with 1,000-foot earth harps and other Burningmanalia, Google directed those resources towards developing moderation solutions that might have prevented the propagation of exploitative videos aimed at and starring children on YouTube — or prohibited mass shooting conspiracy theories from showing up in Google’s “top stories” search results? Or if instead of hiring Chvrches or Chance the Rapper to serenade developers, Facebook redirected those resources to repairing a massive, global platform that clearly incentivizes users to spread fake news faster than credible, verified reports?
This year instead of promising to “continue to look at ways to improve,” as Google did when it and YouTube spread fake news and propaganda about a Texas mass shooting suspect (just one month after the latter announced reforms intended to prevent such things from happening), just improve.
«
YouTube hosted graphic images of bestiality for months • Buzzfeed
»
The “Fantastic Girl and Her Horse in My Village” video itself does not feature any bestiality. It’s largely footage of a woman bathing and brushing a horse. But clicking on it triggers YouTube’s recommendation engine which promptly serves up dozens more animal videos — many with thumbnails featuring graphic bestiality. One such thumbnailed video, published by a channel called “ALL ANIMAL,” had amassed 2.3 million views at the time of this writing.
Most of these bestiality-thumbed videos — which appear to originate in South Asian countries like Cambodia — feature women in sundresses playing with or caring for animals like horses and dogs; Some feature up skirt angles and groin shots of women as they bathe or brush horses and dogs. And there are many. Without needing to search, YouTube’s recommendation algorithm pointed BuzzFeed News to dozens of accounts, each with multiple videos featuring explicit bestiality thumbnails.
«
OK, YouTube, you broke it with your algorithm. Now fix it.
link to this extract
Addressing recent claims of “manipulated” blog posts in the Wayback Machine • Internet Archive Blogs
»
This past December, [Joy Ann] Reid’s lawyers contacted us, asking to have archives of the blog (blog.reidreport.com) taken down, stating that “fraudulent” posts were “inserted into legitimate content” in our archives of the blog. Her attorneys stated that they didn’t know if the alleged insertion happened on the original site or with our archives (the point at which the manipulation is to have occurred, according to Reid, is still unclear to us).
When we reviewed the archives, we found nothing to indicate tampering or hacking of the Wayback Machine versions. At least some of the examples of allegedly fraudulent posts provided to us had been archived at different dates and by different entities.
We let Reid’s lawyers know that the information provided was not sufficient for us to verify claims of manipulation. Consequently, and due to Reid’s being a journalist (a very high-profile one, at that) and the journalistic nature of the blog archives, we declined to take down the archives. We were clear that we would welcome and consider any further information that they could provide us to support their claims.
At some point after our correspondence, a robots.txt exclusion request specific to the Wayback Machine was placed on the live blog.
«
The idea that you could have the Internet Archive itself is a bit fanciful. I could just about believe that someone malicious could have hacked an old blog and inserted content (some old blogs were Swiss cheese, security-wise); but then it should be feasible to follow when pages were added and deduce if they were contemporary or post-facto. (Disclaimer: I follow Reid on Twitter, and don’t really care what her views on homosexuality used to be.)
link to this extract
Alphabet boosts spending as revenues soar • FT
»
Even after deducting so-called TAC — traffic acquisition costs, the fees paid to other companies to carry its search service and adverts — Wall Street expects the company to add $17bn in net revenue this year. That is roughly as much as the entire US newspaper industry earned last year from print advertising.
The company’s net revenues jumped 24% in the first quarter, to $24.9bn, with growth driven by advertising from mobile search and YouTube. That was higher than the 21% most analysts expected.
Revenue from the company’s non-advertising businesses, driven by its cloud computing division, climbed 36%, and now account for 17% of the total.
The latest burst of spending included $7.3bn in capital spending in the first quarter, more than half the $13.2bn the company spent in the whole of last year. Even without the $2.4bn to buy a new office building in New York, that would still have been nearly double what it spent in the first quarter of last year.
Ruth Porat, chief financial officer, said half the capital spending was needed to expand the company’s data centres and network to handle heavier use of its services in future. “The investments we’re making there really support the compute capacity we see in our growth outlook,” she said.
«
Google seems to have discovered the ability to just keep growing its revenues. Hard not to think that it’s YouTube which is really driving the growth.
link to this extract
The Presidency: the hardest job in the world • The Atlantic
John Dickerson interviewed multiple people who have worked in the White House to wonder about how the job has arguably become too big:
»
Eisenhower sorted priorities through a four-quadrant decision matrix that is still a staple of time-management books. It was based on his maxim “What is important is seldom urgent, and what is urgent is seldom important.”
Sage advice, but antique for any president trying to manage the office after the attacks of September 11, 2001. The Cold War presidents monitored slow-moving events that had flashes of urgency. Now the stakes are just as high, but the threats are more numerous and fast-moving…
…Presidents now start their day with the President’s Daily Brief, an intelligence assessment of the threats facing America. How the PDB is delivered changes with each president. Early in his term, Trump reportedly requested a verbal digest of the brief. During the Obama years, the PDB was wrapped in a stiff leather binder and looked like the guest book at a country club. Inside was a grim iPad containing all the possible ways the president could fail at his most essential role. Satellite photos tracked terrorists’ movements, and pictures of failed laptop bombs demonstrated the pace of awful innovation. At the end of the briefing with intelligence officials, a president might be asked whether a specific person should be killed, or whether some mother’s son should be sent on a secret raid from which he might not return.
John F. Kennedy requested that his intelligence briefing be small enough to fit in his pocket. Since 2005, the PDB has been produced by an entirely new entity in the executive branch, the Office of the Director of National Intelligence, which itself includes several intelligence agencies founded since Kennedy’s era, among them the vast Department of Homeland Security.
Monitoring even small threats can take up an entire day. “My definition of a good day was when more than half of the things on my schedule were things I planned versus things that were forced on me,” says Jeh Johnson, who served Obama as homeland-security secretary. An acute example: In June 2016, Johnson planned to travel to China to discuss the long-term threat from cyberattacks. Hours before takeoff, he was forced to cancel the trip so he could monitor developments after the shooting at the Pulse nightclub in Orlando.
“The urgent should not crowd out the important,” says Lisa Monaco, Obama’s chief counterterrorism adviser. “But sometimes you don’t get to the important. Your day is spent just trying to prioritize the urgent. Which urgent first?”
«
Errata, corrigenda and ai no corrida: none notified