Is this when it all started to go wrong for Twitter? Photo by Rob Lawton on Flickr.
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
A selection of 10 links for you. Back to my Mac. I’m @charlesarthur on Twitter. Observations and links welcome.
The case against retweets • The Atlantic
»
The retweet began as a user convention. People would write “Retweet” (or “RT”) and paste in another person’s post. This was cumbersome, but it also meant those words would go out next to your name and photograph. People were selective about what they chose to retweet. When Twitter introduced a retweet button, in 2009, suddenly one click could send a post careening through the network. The automatic retweet took Twitter’s natural tendency for amplification and cranked it up.
Somewhere along the line, the whole system started to go haywire. Twitter began to feel frenetic, unhinged, and—all too often—angry. Some people quit. Others, like Schulz, cut way back. I felt the same urge, but I wanted to do something less extreme, something that would allow me to keep the baby, even as I drained the bathwater. So I began to take note each time I experienced a little hit of outrage or condescension or envy during a Twitter session. What I found was that nearly every time I felt one of these negative emotions, it was triggered by a retweet.
Twitter has a tool that lets you turn off retweets from one person at a time. But I follow thousands of people, so my office mate, who happens to be a skilled programmer, wrote a script for me that turned off retweets from everybody. Retweets make up more than a quarter of all tweets. When they disappeared, my feed had less punch-the-button outrage. Fewer mean screenshots of somebody saying precisely the wrong thing. Less repetition of big, big news. Fewer memes I’d already seen a hundred times. Less breathlessness. And more of what the people I follow were actually thinking about, reading, and doing. It’s still not perfect, but it’s much better…
…what if viral content isn’t the best content? Two Wharton professors have found that anger tops the list of shareable emotions in the social-media world, and a study of the Chinese internet service Weibo found that rage spreads faster than joy, sadness, and disgust. In general, emotional appeals work well, as everyone in media has come to discover. Fundamentally small stories that have no lasting import can dominate Twitter for days: a doctor being dragged off an airplane, the killing of Harambe the gorilla, something Lena Dunham said.
Twitter can destroy your perspective. “Every outrage was becoming the exact same size,” Mike Monteiro, a prominent web designer, wrote in a Medium post about quitting Twitter. “Whether it was a US president declaring war on a foreign nation, or an actor not wearing the proper shade of a designated color to an awards ceremony. On Twitter those problems become exactly the same size.”
«
Panic Blog » The Mystery of the Slow Downloads
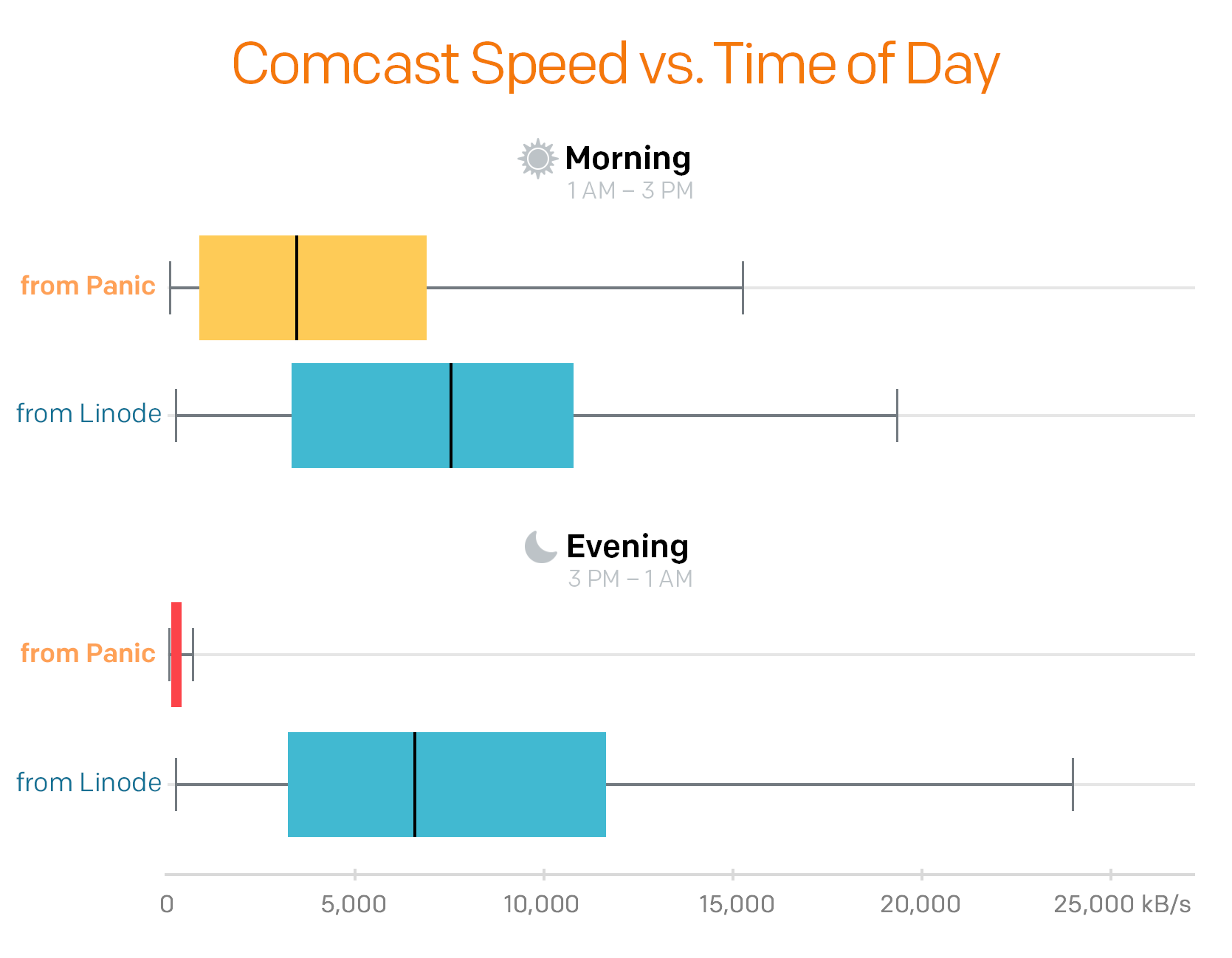
Cabel Sasser got reports from customers – and then discovered himself – that downloads from Panic were really slow. So they put out a script that would let people download a sample file, and recorded which ISP they were with, and at what time:
»
Nuts. The problem reports we’d been hearing were indeed a real thing.
Our downloads really were slow — but seemingly only to Comcast users, and only during peak internet usage times. Something was up.
At first we thought, maybe Comcast bandwidth is just naturally more congested in the evening as people come home from work and begin streaming Netflix, etc. But that didn’t explain why the connections to our Linode control server from Comcast, during the exact same time windows for each tester, were downloading with good speeds.
We wondered, is Comcast intentionally “throttling” Cogent customers? And if so, why?
«
This is a terrific story of internet plumbing.
link to this extract
Business can learn innovation lessons from Pentagon’s secret lab • FT
»
No one lasts long at the Defense Advanced Research Projects Agency, the secretive US government branch that gave birth to the internet, drones and stealth technology. On the day technical personnel arrive at Darpa, they are told when their term will end. To ensure they don’t forget, the date of their final day is printed on their security badge.
This fixed deadline is not a quirk, it is an essential part of the recipe for consistently delivering breakthrough innovations. In 1961, then president John F Kennedy didn’t just commit the US to sending a man to the moon and back — he committed to doing it “before this decade is out”. The Manhattan Project, which produced the first nuclear weapons before that, and the Darpa breakthroughs since all came from a process driven by the same urgency.
In a world hungry for technological advances, too many companies do not know how to manage innovation and are not learning from the breakthrough projects of the past. Innovation efforts too often wind up being worth no more than spare change, when they could be world-changing.
At one extreme, company leadership tries to produce innovation as they would widgets, by micro-managing research with rigid gates and metrics that lead to incremental innovation at best. At the other extreme, leadership treats innovation as art. In the belief that no constraints and no direction lead to the most creative innovations, technologists are left without the expectation or structure needed to identify and develop breakthroughs.
The latter is what happened at Bell Labs, where I started my career. Without some connection to the broader business goals, many of the innovations — from transistors to micro-electromechanical systems — that came out of Bell Labs were instead commercialised by competitors. Whether incrementally useful or useful to competitors, companies eventually tire of paying and shut down their innovation organisations.
«
Neat idea to have a set lifespan, though I wonder if you’d get discouraged if there was a month remaining and you knew you needed two or three months to get your breakthrough.
link to this extract
Tiangong-1 frequently asked questions • Rocket Science
There’s an 8.5-tonne Chinese space station that’s out of control and is going to crash to Earth in a few weeks:
»
Due to the orbital inclination of the Tiangong-1, approximately 42.8 degrees, and the likely uncontrolled nature of the reentry, the final impact point can be anywhere on Earth between 42.8 degrees North and 42.8 degrees South in latitude.
Map showing the area between 42.8 degrees North and 42.8 degrees South latitude (in green), over which Tiangong-1 could reenter. Graph at left shows population density. Credit: ESA CC BY-SA IGO 3.0As you can see in the chart at right in the map above, the re-entry location itself is not uniformly distributed. Due to the geometry of the craft’s circular orbit, the probability of reentry happening at the maximum (42.8 degrees N) and minimum (42.8 degrees S) latitude are higher than at the equator.
Why is this?
Because of the low eccentricity and non-polar inclination of the orbit (in other words, because the orbit of the space station around the Earth is circular and at an angle with respect to the equator), the space station spends more time near the edges of the band then it spends crossing the equatorial region of Earth. This leads to a higher likelihood of reentry occurring near the edges of the latitude band, i.e., the top and bottom of the band in the map above.
«
More updates here. Have you booked that quick break holiday to northern Europe/Canada/Antarctica yet?
link to this extract
Galaxy S9+ fingerprint sensor placement may be too low for some • SamMobile
»
Alongside the aggravation behind the Bixby button for most users, the placement of the fingerprint sensor was most definitely quite high on the list of complaints. With Samsung a company that keeps its ear to the streets and makes changes accordingly, we have a differently placed sensor on the new flagships. But, for those with larger hands, like myself, it is now a hassle as the sensor is a tad too low. This is especially an issue on the S9+. The dual rear camera means the fingerprint sensor is placed lower on the body on the S9+ compared to the S9. Yes, the Galaxy S9 is shorter and should technically have the same problem, but since the S9+ is heavier, one tends to grip it higher up, which compounds the issue.
I had no issues at all with the placement of the sensor on the 2017 flagships; my finger rested right on the scanner. Others got used to it after a while. The previous placement appeased larger-handed folks, though, whereas this year it is kind of a middle ground for everyone.
«
So Samsung fired all its large-handed testers? Also, this really does count as one of the cream of first-world problems: the fingerprint sensor on a not-yet-on-sale phone is in slightly the wrong place for you.
link to this extract
Google is helping the Pentagon build AI for drones • Gizmodo
»
Google has partnered with the United States Department of Defense to help the agency develop artificial intelligence for analyzing drone footage, a move that set off a firestorm among employees of the technology giant when they learned of Google’s involvement.
Google’s pilot project with the Defense Department’s Project Maven, an effort to identify objects in drone footage, has not been previously reported, but it was discussed widely within the company last week when information about the project was shared on an internal mailing list, according to sources who asked not to be named because they were not authorized to speak publicly about the project.
Some Google employees were outraged that the company would offer resources to the military for surveillance technology involved in drone operations, sources said, while others argued that the project raised important ethical questions about the development and use of machine learning.
Google’s Eric Schmidt summed up the tech industry’s concerns about collaborating with the Pentagon at a talk last fall. “There’s a general concern in the tech community of somehow the military-industrial complex using their stuff to kill people incorrectly,” he said. While Google says its involvement in Project Maven is not related to combat uses, the issue has still sparked concern among employees, sources said…
…The project’s first assignment was to help the Pentagon efficiently process the deluge of video footage collected daily by its aerial drones—an amount of footage so vast that human analysts can’t keep up, according to Greg Allen, an adjunct fellow at the Center for a New American Security, who co-authored a lengthy July 2017 report on the military’s use of artificial intelligence. Although the Defense Department has poured resources into the development of advanced sensor technology to gather information during drone flights, it has lagged in creating analysis tools to comb through the data.
«
Geek Squad’s relationship with FBI is cozier than we thought • Electronic Frontier Foundation
»
Another document records a $500 payment from the FBI to a confidential Geek Squad informant. This appears to be one of the same payments at issue in the prosecution of Mark Rettenmaier, the California doctor who was charged with possession of child pornography after Best Buy sent his computer to the Kentucky Geek Squad repair facility.
Other documents show that over the years of working with Geek Squad employees, FBI agents developed a process for investigating and prosecuting people who sent their devices to the Geek Squad for repairs. The documents detail a series of FBI investigations in which a Geek Squad employee would call the FBI’s Louisville field office after finding what they believed was child pornography.
The FBI agent would show up, review the images or video and determine whether they believe they are illegal content. After that, they would seize the hard drive or computer and send it to another FBI field office near where the owner of the device lived. Agents at that local FBI office would then investigate further, and in some cases try to obtain a warrant to search the device.
Some of these reports indicate that the FBI treated Geek Squad employees as informants, identifying them as “CHS,” which is shorthand for confidential human sources. In other cases, the FBI identifies the initial calls as coming from Best Buy employees, raising questions as to whether certain employees had different relationships with the FBI.
«
Now, is this really, actually bad? I’d suggest that the Geek Squad staff are doing precisely what you’d want concerned citizens to do: alerting the authorities when they think they have evidence of malfeasance. Then the authorities check it. The accused person might never know they were accused; it could all blow over. The evidence still has to be heard in public.
Related: it was staff at a PC World (akin to Geek Squad) in the UK who found child abuse imagery on the computer of a British man. And so began the downfall of Paul Gadd – aka the multiply-chart-topping music star Gary Glitter.
link to this extract
‘Stalkerware’ seller shuts down apps ‘indefinitely’ after getting hacked again • Motherboard
Lorenzo Franceschi-Bicchierai:
»
A company that sells spyware to regular consumers is “immediately and indefinitely halting” all of its services, just a couple of weeks after a new damaging hack.
Retina-X Studios, which sells several products marketed to parents and employers to keep tabs on their children and employees—but also used by jealous partners to spy on their significant others—announced that its shutting down all its spyware apps on Tuesday with a message at the top of its website.
“Regrettably Retina-X Studios, which offers cutting edge technology that helps parents and employers gather important information on devices they own, has been the victim of sophisticated and repeated illegal hackings,” read the message, which was titled “important note” in all caps.
The company sells subscriptions to apps that allow the operator to access practically anything on a target’s phone or computer, such as text messages, emails, photos , and location information. Retina-X is just one of a slew of companies that sell such services, marketing them to everyday users—as opposed to law enforcement or intelligence agencies. Some critics call these apps “Stalkerware.”
«
BlackBerry sues Facebook, WhatsApp, Instagram over patent infringement • Reuters
»
BlackBerry Ltd on Tuesday filed a patent infringement lawsuit against Facebook Inc and its WhatsApp and Instagram apps, arguing that they copied technology and features from BlackBerry Messenger.
Litigation over patent infringement is part of BlackBerry Chief Executive John Chen’s strategy for making money for the company, which has lost market share in the smartphone market it once dominated.
“Defendants created mobile messaging applications that co-opt BlackBerry’s innovations, using a number of the innovative security, user interface, and functionality enhancing features,” Canada-based BlackBerry said in a filing with a Los Angeles federal court.
“Protecting shareholder assets and intellectual property is the job of every CEO,” BlackBerry spokeswoman Sarah McKinney said in an email. However, she noted that litigation was “not central to BlackBerry’s strategy.”
The lawsuit followed years of negotiation and BlackBerry has an obligation to shareholders to pursue appropriate legal remedies, she added.
«
Facebook isn’t impressed. But last year BlackBerry squeezed $940m out of Qualcomm in arbitration over royalties. Chen is nobody’s fool. This doesn’t have to make a lot to be almost pure profit.
link to this extract
One single malicious vehicle can block “smart” street intersections in the US • Bleeping Computer
»
In the US, the Department of Transportation (DOT) has started implementing a V2I system called Intelligent Traffic Signal System (I-SIG), already found on the streets of New York, Tampa (Florida), Cheyenne (Wyoming), Temple (Arizona), and Palo Alto (California).
But the Michigan research team says the I-SIG system in its current default configuration is vulnerable to basic data spoofing attacks.
Researchers say this is “due to a vulnerability at the signal control algorithm level,” which they call “the last vehicle advantage.” This means that the latest arriving vehicle can determine the traffic system’s algorithm output.
The research team says I-SIG doesn’t come with protection from spoofing attacks, allowing one vehicle to send repeated messages to a traffic intersection, posing as the latest vehicle that arrived at the intersection.
Rresearchers say an attacker can use this bug and trick a traffic control system into believing cars keep arriving from all sides on the left lane. The system reacted by altering traffic lights and prolonging red light times to accommodate the non-existent vehicles, causing a delay in the entire intersection. (Here’s the simulation.)
«
Errata, corrigenda and ai no corrida: none notified