
A Bulgarian playlist on Spotify (not this one) is reckoned to have made a huge profit – legally. Photo by Andrew Mager on Flickr
»You can sign up to receive each day’s Start Up post by email (arriving at about 0800GMT each weekday). You’ll need to click a confirmation link, so no spam.«
A selection of 10 links for you. Tell them you hear them. I’m @charlesarthur on Twitter. Observations and links welcome.
Bot-driven credential stuffing hits new heights • Infosecurity Magazine
»
More than 40% of global log-in attempts are malicious thanks to bot-driven credential stuffing attacks, according to the latest report from Akamai.
The cloud delivery provider’s latest State of the Internet/Security report for Q4 2017 comprised analysis from over 7.3 trillion bot requests per month.
It claimed that such requests account for over 30% of all web traffic across its platform per day, excluding video streaming. However, malicious activity has seen a sharp increase, as cyber-criminals look to switch botnets from DDoS attacks to using stolen credentials to try to access online accounts.
Of the 17 billion login requests Akamai tracked in November and December, over two-fifths (43%) were used for credential abuse. The figure rose to a staggering 82% for the hospitality industry.
The stats chime with similar data from fraud prevention specialist ThreatMetrix, which claimed in its latest Cybercrime report for Q4 2017 that there were 34 million bot attacks during the peak festive shopping period, rising to 800 million for the quarter.
It said that for some businesses bot activity can make up as much as 90% of their daily traffic.
Akamai claimed that credential stuffing can cost businesses up to $2.7m annually.
«
Just amazing. It’s as though the internet isn’t really for actual people most of the time.
link to this extract
The Goldilocks era for iPhone has begun • Above Avalon
»
The lack of iPhone unit sales growth is not surprising. In May 2016, I published “iPhone Warning Signs” and the conclusion that “the iPhone growth story is breaking apart and management does not seem to be in control of the situation.” Over the past two years, this is exactly what has happened as the four iPhone growth warnings signs highlighted in my article have fully materialized.
• Mobile carrier expansion is complete. Apple no longer has a sales tailwind from bringing iPhone to new carriers around the world.
• India isn’t the next China. Any expectation of India becoming an iPhone sales growth engine in the near term is misplaced.
• Smartphone saturation. The era of iPhone sales growth coming from people buying their first smartphone has come to an end.
• Running out of Android switchers. There are only so many premium Android users in a position to switch to iPhone.Two additional red flags have now appeared:
Slowing iPhone upgrade rate. iPhone users are holding on to their devices for longer before upgrading. This trend has been unfolding for years, but the impact on iPhone sales is only now being felt.
• Overserving users. One reason iPhone users are holding on to their devices for longer is that their needs are being met with older models and less capable features. While new iPhones are still intriguing and enticing to a majority of iPhone users, a growing percentage of the iPhone installed base is content with their current device.Instead of there being one particular reason or cause for the lack of iPhone unit sales growth, the six preceding factors have come together to create a much less friendly growth environment.
«
This applies across the smartphone market, of course. (Remember IDC says total sales shrank last year.) Expect more churn between OEMs at the lower price ranges, and a real challenge at the premium end – and not just for Apple. It’s probably safer than others.
link to this extract
#NotOKGoogle search suggestions: 2018 edition • Medium
»
I’m at a loss to understand how this could *still* be happening. The quality and reliability of Google’s search suggestions have actually devolved in the past year. It almost reads like these input signals are coming out of Reddit, Twitter and other online and social news forums.
Here’s February 20, 2018. Below are some examples of what kids are likely to see when they begin to type in or use Google to look up a controversial topic. Why does this matter? It matters because this is information pollution at the most critical interface: search. Google is the knowledge portal for most of the world.
When toxic information — suggestions like the ones seen below — get in the way of people actively fact checking and truth-seeking, it’s a major problem.
We’re at a critical juncture in social cohesion & the role of tech in society. The walls have been breached; platforms are now getting vandalized in broad daylight.
«
Note also that those are searches relating to American topics. But as Carole Cadwalladr has shown at the Guardian (a year ago, and again when Albright showed these) you get just as bad outside the US.
link to this extract
Internet of babies: when baby monitors fail to be smart • SEC Consult
»
Baby monitors serve an important purpose in securing and monitoring our loved ones. Unfortunately, the investigated device “Mi-Cam” from miSafes (and potentially further devices) is affected by a number of critical security vulnerabilities which raise serious security and privacy concerns. An attacker is able to access and interact with arbitrary video baby monitors and hijack other user accounts. Based on observed user identifier values extracted from the cloud API and Google Play store data, an estimated total number of more than 52,000 user accounts and video baby monitors are affected (implying a 1:1 distribution of user accounts to video baby monitors). Even worse, neither the vendor nor the CNCERT/CC could be reached for the coordination for our responsible disclosure process. Hence the issues are (up until the publication of this article) not patched and our recommendation is to keep the video baby monitors offline until further notice.
«
Baby monitors have never been the most secure things (in older times, they offered a couple of radio channels; people in adjacent flats or houses could sometimes eavesdrop accidentally). But this is taking it further.
link to this extract
Ex-engineer sues Google, saying he was fired for *condemning* diversity memo • The Guardian
»
Tim Chevalier, a site reliability engineer who worked for Google until November 2017, sued his former employer in California state court on Wednesday. Chevalier, who identifies as queer, disabled and transgender, alleges that Google terminated him over posts he made on internal forums advocating for diversity at Google and criticizing Damore.
Damore was fired for “advancing harmful gender stereotypes” in August 2017 after the memo, in which he posited that psychological differences between men and women explain the gaping gender imbalance at Google, was leaked and went viral…
…The Chevalier lawsuit offers a different spin on the debates that played out on Google’s internal email lists and message boards, which the attorney David Lowe described in a statement as “a cesspool of bullying and harassment”. Google failed to prevent employees from using the internal platforms to discriminate against marginalized groups, the suit alleges, allowing Google employees to call LGBT co-workers “immoral” and post statements such as:“If we have fewer Black and Latin@ people here, doesn’t that mean they’re not as good?”
Chevalier regularly participated in these internal discussions, the lawsuit states, “calling out discrimination and harassment for what it was and asking his peers to reflect on perspectives different from their own”.
“It is a cruel irony that Google attempted to justify firing me by claiming that my social networking posts showed bias against my harassers,” Chevalier said in a statement. “The anti-discrimination laws are meant to protect marginalized and underrepresented groups – not those who attack them.”
In an emailed statement, Google defended its termination of Chevalier.
“An important part of our culture is lively debate. But like any workplace, that doesn’t mean anything goes,” a spokeswoman, Gina Scigliano, said…
«
This now just seems like there’s war brewing internally.
link to this extract
The pro-Trump media has met its match in the Parkland students • Buzzfeed
»
factions of the mainstream media have proven time and again that they are unprepared for the pro-Trump media’s information war. Whether it’s Scott Pelley falling into a trap while interviewing pro-Trump personality Mike Cernovich, former New York Times public editor Liz Spayd taking the bait while being trolled on Twitter, or Megyn Kelly and NBC allowing Alex Jones to gin up outrage and scoop her on her own interview, the mainstream media has repeatedly failed to grasp the pro-Trump media’s new rules. It’s never quite understood that its online arm isn’t just an opposition force — it’s a parallel institution that insists on its own reality.
In the case of the Parkland students, however, the mold doesn’t fit. A look at the Twitter feeds of students like David Hogg shows that they are a remarkable foil for the pro-Trump media’s trolling tactics. Like the pro-Trump media, they, too, are an insurgent political force that’s native to the internet. And while they use legacy platforms like cable news to build awareness of their names and of their causes, much of the real work happens online.
They use platforms like Twitter to call out and put pressure on politicians. They address prominent critics like Bill O’Reilly not with bland, carefully written statements, but by dunking on them, and they respond to misinformation in real-time with their own viral, emoji-laden posts. Rather than take the bait on the crisis actor narrative, they opted to have fun with the conspiracy theories by mocking them. “I’m thankful that there are people out there finding my doppelgangers for me. I’ve always wanted to have a party with a room full of people who look like me,” Emma Gonzalez, a Parkland student, told BuzzFeed News. By dismissing the conspiracies for what they are — a tired, rather boring page in the Infowars playbook — Gonzalez and her classmates have stripped them of their power. Before the pro-Trump media can finish its line of attack, the students, unfazed, have moved on, staying one step ahead of their political enemies and owning the story.
«
It is fascinating to behold – and now that Twitter has verified a lot of those students, they are amassing huge followings. It is different this time. Wendy Grossman, an Overspill reader, suggests that US school shootings and gun control might be this new generation’s Vietnam: “their lives are threatened by decisions made by ‘the grown-ups’, who are out of touch with the incoming change in society.”
link to this extract
Apple plans upgrades to popular AirPods headphones • Bloomberg
»
The Cupertino, California-based technology giant is working on a new version for release as soon as this year with an upgraded wireless chip, the [unnamed] people said. A subsequent model for as early as next year is planned to be water resistant, they added, asking not to be identified discussing private product plans.
The model coming as early as this year will let people summon Apple’s Siri digital assistant without physically tapping the headphones by saying “Hey Siri.” The function will work similarly to how a user activates Siri on an iPhone or a HomePod speaker hands-free. The headphones, internally known as B288, will include an upgraded Apple-designed wireless chip for managing Bluetooth connections. The first AirPods include a chip known as the W1, and Apple released the W2 with the Apple Watch last year.
The idea for the water-resistant model is for the headphones to survive splashes of water and rain, the people said. They likely won’t be designed to be submerged in water.
«
“Splashes of water”? Didn’t know they were subjected to that much. Note in passing all the fol-de-rol of formal American newswriting: the amazingly dull headline, the requirement to describe Apple as “the Cupertino-based technology giant”, in case you were trying to find them on a map; the inability to just say “my sources”; the strangulated “as soon as this year” instead of “perhaps this year”. It’s like a weird grammar of its own.
link to this extract
The great big Spotify scam: did a Bulgarian playlister swindle their way to a fortune on streaming service? • Music Business Worldwide
»
Our sources tell us that this data, within Spotify’s analytics, was pretty consistent: around 1,200 monthly listeners, with some variation, were hitting play on each ‘Soulful Music’ song.
So let’s bring all of this information together:
• A Bulgarian individual or collective managed to run at least one third-party playlist – ‘Soulful Music’ – which generated so much revenue in September 2017, it landed at No.35 on Spotify’s global 100 chart. (We actually have a testimonial from a further trusted source that ‘Soulful Music’ went on to break the US Top 10 in late September, but we haven’t seen the evidence.)
• However, ‘Soulful Music’ had less than 1,800 followers at the time.
• What’s more, each of its 467 tracks were only attracting around 1,200 monthly listeners apiece.Considering these numbers, how on earth could ‘Soulful Music’ beat down branded efforts from Sony, Universal and Warner to become one of the biggest playlists in the world?
There are only two possible answers to that question.
Soulful Music could – cough, splutter, sneeze – have been a completely legitimate niche playlist which was simply so addictive, 1,800 people just kept playing their way through it over and over and over.
Or – and this rather strikes us as the more likely scenario – an individual in Bulgaria set up circa 1,200 Spotify accounts, which continually played these 467 tracks on a loop, on random (thus why some songs had slightly different play counts to others).
In order to generate enough revenue to hit Spotify’s US Top 15 playlist rankings, all of these accounts must have been paid-for, premium subscriptions.
And it’s here that the genius of the (potential) ‘scam’ starts to become clear.
Let’s say that our friend the Bulgarian had laid out the money to purchase 1,200 premium accounts.
That would take a lot of work; they’d have to create individual email addresses and identities for each one.
It would also be expensive. A nice easy calculation shows why: 1,200 X $9.99-per-month would mean an outlay of $12,000 per month (although this could be reduced by family plans and other discounts).
That’s the monthly outgoings.
Now let’s work out the potential monthly revenue generation.
«
Spoiler: it’s a lot bigger. (It’s a LOT bigger.) And I bet family plans would be the way to go in setting up the paid accounts, cutting outgoings by 80%.
link to this extract
Jihadists see a funding boon in bitcoin • WSJ
Brett Forrest and Justin Scheck:
»
cryptocurrency has become an increasingly discussed topic among jihadist groups in the Middle East. This month, an issue of al-Haqiqa, a pro-al Qaeda online magazine, included a “Tech Talk” section that outlines bitcoin basics.
Al Sadaqah has realized what other violent groups have found: Raising funds in cryptocurrencies can evade the rules the global banking system has put in place to block terror financing and money laundering.
“It is fast, efficient, and does not pass through the same interest-loaded and traceable routes that any usual payment methods would go through,” Hassan Abdo, an al Sadaqah spokesman, wrote to The Wall Street Journal in a text message. “This way we and our donors can keep our full anonymity.”
Yaya Fanusie, an ex-CIA analyst who is a director of the Washington-based counterterrorism think tank Foundation for Defense of Democracies, has been tracking al Sadaqah’s bitcoin accounts for months. He said it is difficult to confirm the identities of such groups online because they hide behind fake personas and use technology to protect their identities.
“What they’re more than likely attempting to do isn’t just to pick up a few peanuts in donations here,” said Michael Smith, a fellow at the New America think tank who studies terrorists’ use of technology. “It’s to build a network of sympathizers.”
«
Maybe that’s the new use for the blockchain. Not quite what Satoshi intended.
link to this extract
The #1 reason facebook won’t ever change • Om Malik
Om Malik on how “growth” and “engagement” are the constant refrains for Facebook:
»
now you know why Facebook does what it has been doing recently — sending various messages constantly to get you back on the service. I know first hand. I left Facebook on September 23, 2017, and not a single day has gone by when I don’t get at least a couple of emails or some SMS messages trying to get me back with notes about what friends have posted recently, or birthdays or other milestones. I keep unsubscribing and they still keep coming. Now I’ve set up a spam rule: all emails from Facebook.com go straight into the spam folder.
Facebook’s DNA also explains why it is pushing Protect (the FB-owned VPN) and what it brings to the table. First of all, it allows the company to keep tabs on what apps people are using in different parts of the world, which in turn gives it a leg up on who or what to copy or, potentially, acquire.
The VPN data also allows Facebook to better target its ads — much like how Google Mail and Google Chrome allows Google to better target what ads you see. By the way, Facebook isn’t the only one who is taking data from VPN mobile streams. Other data brokers buy data from other VPN apps. To be clear, just because others are doing it doesn’t make it right for Facebook to follow suit. I would love to see a US version of GDPR — a citizen data rights manifesto — to be put on the table.
How does Protect help Facebook?
Protect can tell that you browsed H&M’s North American site, visited NYTimes.com, and bought groceries on Farmstead. It can figure out how much time you spend on various sites and services and start to build a better profile of your online usage for smarter ad targeting and to place you in more and more buckets.
In other words, Protect brings more granular and refined data into Facebook’s system, which in turn allows Facebook to refine its algorithms and become more efficient at targeting of ads. It is especially more useful in the Asia Pacific region and other emerging markets where it is pretty tricky to create buckets and hyper-targeting. Overseas users of Facebook are using the social platform on phones that are usually pre-paid phones and don’t have as much personalized information available from third party sources to create profiles. Facebook needs to find more high-value customers in the hordes of users in Asia, Africa, and Latin America.
«
I hadn’t thought about the point that PAYG phones mean less data for networks, but in retrospect it’s obvious, and relevant.
link to this extract
Errata, corrigenda and ai no corrida: none notified.


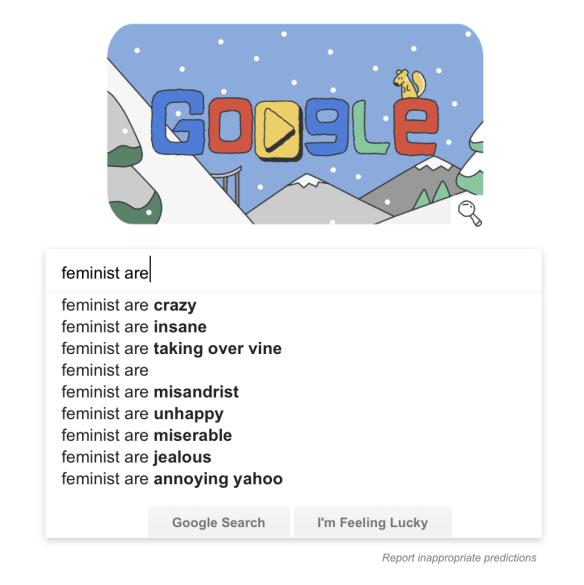
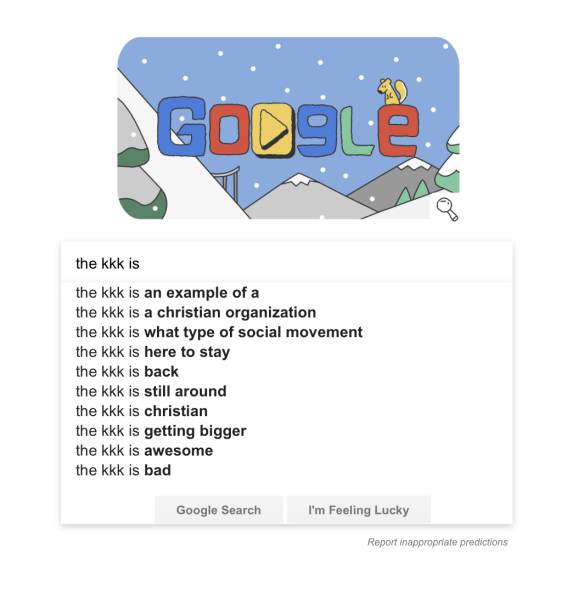
As I’ve been saying for a long time, Google’s results reflect what is *popular*, not what is *right*. What we are seeing is roughly the effect of the average web or social media item being more and more outrage/clickbait. There’s no magic which is going to sort out sense from nonsense. If there were such an all-knowing algorithm, we could just apply it to “news”, and not have a problem with tabloid sensationalism or outright propaganda.
Google was God a few year ago, now it’s the Devil (or at least a servant). Sadly, neither view is actually addressing the structural problem.
Google’s auto-suggest results are influenced by your own search history. I get very different results for those searches compared to the screenshots.
I think it also depends on your location: I’m guessing you’re in the UK, so that might also explain it.