Uber launches in Cincinnati in 2014. Think it’s profitable there? Probably not. Photo by 5chw4r7z on Flickr.
Back early, by hardly any demand at all! But that’s life.
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
A selection of 13 links for you. Unlucky for some I’m @charlesarthur on Twitter. Observations and links welcome.
How Meltdown and Spectre were independently discovered by four research teams at once • WIRED
»
The Graz team’s discovery, an attack that would come to be known as Meltdown, proved a critical crack in one of computing’s most basic safeguards. And perhaps most troubling of all, the feature they had exploited was introduced into Intel chips in the mid-1990s. The attack had somehow remained possible, without any apparent public discovery, for decades.
Yet when Intel responded to the trio’s warning—after a long week of silence—the company gave them a surprising response. Though Intel was indeed working on a fix, the Graz team wasn’t the first to tell the chip giant about the vulnerability. In fact, two other research teams had beaten them to it. Counting another, related technique that would come to be known as Spectre, Intel told the researchers they were actually the fourth to report the new class of attack, all within a period of just months.
“As far as I can tell it’s a crazy coincidence,” says Paul Kocher, a well-known security researcher and one of the two people who independently reported the distinct but related Spectre attack to chipmakers. “The two threads have no commonality,” he adds. “There’s no reason someone couldn’t have found this years ago instead of today.”
«
I’d imagine there were people in security agencies who found this a while ago, and liked it. The coincidental discovery? There are tons of people everywhere who are trying to find security glitches and hacks.
link to this extract
The Spectre of an advertising meltdown: what you need to know • Lawfare
»
The information security world is focused on two new security vulnerabilities, “Spectre” and “Meltdown”, that represent vulnerabilities embedded in computer hardware. Lawfare readers should respond in two ways: keep their operating systems up to date and, critically, install an ad-blocker for your web browser. (Here are guides on how to do so in Chrome and Firefox.) In fact, a proper response to Spectre should involve ad-blocking on all government computers. Other than that, don’t worry.
Readers who just wanted to know what to do can stop reading. But for those curious about some of the technical background on these vulnerabilities and why ad-blocking is an essential security measure for a modern computer, read on.
«
No tracking, no revenue: Apple’s privacy feature costs ad companies millions • The Guardian
»
Advertising technology firm Criteo, one of the largest in the industry, says that the Intelligent Tracking Prevention (ITP) feature for Safari, which holds 15% of the global browser market, is likely to cut its 2018 revenue by more than a fifth compared to projections made before ITP was announced.
With annual revenue in 2016 topping $730m, the overall cost of the privacy feature on just one company is likely to be in the hundreds of millions of dollars.
Dennis Buchheim, general manager of the Interactive Advertising Bureau’s Tech Lab, said that the feature would impact the industry widely.
“We expect a range of companies are facing similar negative impacts from Apple’s Safari tracking changes. Moreover, we anticipate that Apple will retain ITP and evolve it over time as they see fit,” Buchheim told the Guardian.
“There will surely be some continued efforts to ‘outwit’ ITP, but we recommend more sustainable, responsible approaches in the short-term,” Buchheim added.
«
John Gruber called this article “pro-ad industry”. Can’t say I see that myself.
link to this extract
Uber is not price competitive with transit • Medium
»
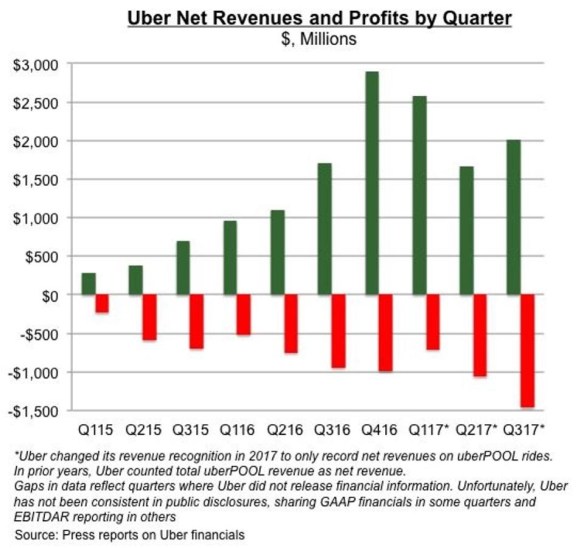
Uber’s strategy of reporting large losses to develop a customer base is not unique; many tech companies have taken a similar path before it. The tech press has compared Uber favorably with Amazon — now the fourth largest company in the world by market cap — because the latter reported growing losses every year from 1994 to 2000, during which time investors worried it would ever turn a profit. But there’s an important detail left out of those stories: how the scale of Uber’s losses compare to Amazon’s.
In WTF? What’s the Future and Why It’s Up to Us, Tim O’Reilly writes that Amazon lost $2.9bn over its first five years before turning a profit in 2001. That may seem like a lot, until Uber’s losses are placed beside it.
In 2016 alone, Uber lost $2.8bn, almost as much as Amazon lost over five years; but the losses didn’t stop there. Over the first three quarters of the 2017 fiscal year, Uber has already lost $3.2bn, with a loss of $1.5bn in the most recent quarter. A chart of Uber’s financials shows its losses have gotten worse in each quarter of 2017, suggesting annual losses for the year will likely hit $5bn, and the company has no realistic path to profitability.
«
Well, it does have a path to profitability – raise its prices. Except that (it’s later explained)
»
“Transportation industry expert Hubert Horan has detailed how “[d]rivers, vehicles and fuel account for 85% of urban car service costs” — costs which cannot be reduced with scale”.
«
And Marx (this one) does look at the question of driverless filling the gap.
link to this extract
Where did WikiLeaks’ $25m bitcoin fortune go? • The Daily Beast
»
Everyone from early investors to cybercriminals has benefited from the huge spike in the value of bitcoin in the past few weeks. It’s a boon for one other outfit that has likely racked up tens of millions of dollars’ worth of the cryptocurrency: WikiLeaks.
The transparency organization may be sitting on a stockpile of bitcoin valued at around $25 million, and has likely exchanged several other large cryptocurrency caches for fiat cash, according to two sources who independently analyzed WikiLeaks’ bitcoin transactions.
“Last wallet looks like his piggy bank,” John Bambenek, a security expert who has previously tracked Neo-Nazis’ use of bitcoin, told The Daily Beast, pointing to a specific bitcoin address believed to be linked to WikiLeaks.
An oft-repeated myth is that bitcoin is an anonymous currency. Although it can sometimes be harder for observers to determine which bitcoin address belongs to whom, the blockchain—the ledger listing all bitcoin transactions—is entirely public. Using this, it’s often possible to see which bitcoin wallets are associated with one another, perhaps link them to real identities, and infer what a bitcoin transaction was for…
…“Well, considering Julian [assange] is holed up in an embassy, it’s entirely possible someone else has physical possession. But would you trust that cash to someone else?” Bambenek said.
Julian Assange and the main WikiLeaks Twitter account did not respond to a request for comment.
Unsurprisingly, it appears WikiLeaks may have converted some of its bitcoin donations into much more practical fiat currency, too. Several other large chunks of bitcoin moved from the WikiLeaks donation address to BitPay, a bitcoin exchange platform, Bambenek said.“I am assuming he spent, because it went to BitPay,” Bambenek added, referring to WikiLeaks founder Assange. The second source said WikiLeaks has spent around 3,500 bitcoin since its move to the digital currency.
«
With rumours that Ecuador is looking to shift Assange out of its London embassy – and thus into the waiting arms of UK police – he might need that.
link to this extract
Google faces new discrimination charge: paying female teachers less than men • The Guardian
»
Google, which has been accused of systematically underpaying female engineers and other workers, is now facing allegations that it discriminated against women who taught employees’ children at the company’s childcare center.
A former employee, Heidi Lamar, is alleging in a complaint that female teachers were paid lower salaries than men with fewer qualifications doing the same job.
Lamar, who worked at Google for four years before quitting in 2017, alleged that the technology company employed roughly 147 women and three men as pre-school teachers, but that two of those men were granted higher starting salaries than nearly all of the women.
“I didn’t want to work for a company that I can’t trust, that makes me feel like my values of gender equality are being compromised,” Lamar, 31, told the Guardian.
«
Oh, but now read on.
link to this extract
Google memo author James Damore sues company for discrimination against white males • Buzzfeed
»
The author of a controversial memo that sparked debates about gender and diversity at Google sued his former employer on Monday, alleging that the company discriminates against politically conservative white men.
James Damore, who was fired in August for internally circulating a manifesto that argued Google’s gender pay gap was the result of genetic differences that tend to favor men, said in a lawsuit filed in Santa Clara Superior Court that the search giant “singled out, mistreated, and systematically punished and terminated” employees who deviated from the company’s view on diversity. Damore and a second plaintiff, David Gudeman, another former Google engineer, are seeking class-action status for anyone who identifies as conservative, Caucasian, or male.
The men are being represented by Harmeet K. Dhillon, the Republican National Committee’s committeewoman for California.
“Google’s management goes to extreme — and illegal — lengths to encourage hiring managers to take protected categories such as race and/or gender into consideration as determinative hiring factors, to the detriment of Caucasian and male employees and potential employees at Google,” the suit reads.
«
Another quote from the suit: “…The presence of Caucasians and males was mocked with ‘boos’ during company- wide weekly meetings”. I bet Google wishes it had dumped Damore’s CV and never gave him an interview.
link to this extract
CoffeeMiner hijacks public Wi-Fi users’ browsing sessions to mine cryptocurrency • ZDNet
»
According to the developer, public Wi-Fi may also now be a source of income for hackers that successfully pull off man-in-the-middle (MiTM) attacks to launch cryptocurrency miners.
The project, released to the public for academic study, leans upon the recent discovery of a cryptocurrency miner discovered on a Starbucks Wi-Fi network.
CoffeeMiner works in a similar way. The attacking code aims to force all devices connected to a public Wi-Fi network to covertly mine cryptocurrency.
The attack works through the spoofing of Address Resolution Protocol (ARP) messages by way of the dsniff library which intercepts all traffic on the public network.
Mitmproxy is then used to inject JavaScript into pages the Wi-Fi users visit. To keep the process clean, the developer injected only one line of code which calls a cryptocurrency miner.
«
Can’t wait for the cryptocurrency madness to expire.
link to this extract
No boundaries for user identities: web trackers exploit browser login managers • Freedom To Tinker
»
We show how third-party scripts exploit browsers’ built-in login managers (also called password managers) to retrieve and exfiltrate user identifiers without user awareness. To the best of our knowledge, our research is the first to show that login managers are being abused by third-party scripts for the purposes of web tracking.
The underlying vulnerability of login managers to credential theft has been known for years. Much of the past discussion has focused on password exfiltration by malicious scripts through cross-site scripting (XSS) attacks. Fortunately, we haven’t found password theft on the 50,000 sites that we analyzed. Instead, we found tracking scripts embedded by the first party abusing the same technique to extract emails addresses for building tracking identifiers.
The image above shows the process. First, a user fills out a login form on the page and asks the browser to save the login. The tracking script is not present on the login page [1]. Then, the user visits another page on the same website which includes the third-party tracking script. The tracking script inserts an invisible login form, which is automatically filled in by the browser’s login manager. The third-party script retrieves the user’s email address by reading the populated form and sends the email hashes to third-party servers.
«
The link above (“has been known”) is actually only one of the five offered in that phrase – OK, so I’m lazy about copying all the HTML sometimes. It’s a problem though that the most secure way to handle passwords is also so exploitable. So it’s back to remembering them all?
link to this extract
My internet mea culpa • Shift Newco
»
Being generous to the prophets [Stewart] Brand and [Kevin] Kelly et al, it’s entirely reasonable to argue that this version of a global village is not what they proposed or envisioned. Minorities are still denied equal voices on the internet — harassed off of it, or still unable to even get online. Massive amounts of data is still hidden behind firewalls or not online at all. Projects to bring more information online (such as Google Books) have foundered due to institutional obstruction or a change of priorities in those undertaking them. Governments still have secrets. Organizations such as Wikileaks that showed early promise in this regard have been re-cast as political tools through some mix of their own hubris and the adversarial efforts of the governments they seek to expose.
It’s quite easy to see the differences between the internet world we live in and the utopia we were promised. And a fair measure of that is because we didn’t actually make it to the utopia. The solution, then, the argument goes, is to keep at it. To keep taking our medicine even as the patient gets more sick, on the faith that we will one day reach that future state of total-information-freedom and equality of voices.
This isn’t an unreasonable position, but I think it would have been worth thinking about beforehand. There is a difference between Advil and chemotherapy. If you’re not dying of cancer, the benefits of something like chemotherapy are dubious. A better metaphor might be back pain. I have back pain. I could get surgery for my back pain. But the surgery is hugely debilitating, with only moderate chances of success. It is not unreasonable for me to say “nah, not worth it.”
«
I think Wikileaks on its own sums up the degradation of the dream. It began trying, and succeeding, in exposing African dictators; it has ended up helping Russian ones, and quite where it morphed from idealism to cynicism is difficult to pinpoint.
link to this extract
What happened when the infosec community outed its own sexual predators • The Verge
»
Since autumn, I’ve noticed SHA hashes popping up again across my social media feeds — hashes of men’s initials or sometimes full names. These strings cannot be decrypted but if you know or suspect what the solution is, you can try running the same algorithm over it and see if the hash matches. Women describe how they or a friend were harassed or assaulted, they describe in vague terms the man in question. And then they post the hash, so their friends can check to see if they’ve been attacked by the same man.
It’s a step up from the “Shitty Media Men” spreadsheet that went viral a couple of months ago, a means of sharing information that is easy enough among the women who are capable of opening a command line window and running SHA-256 on a man’s name — women who deal professionally with secrets, privacy, truth, and verification. These are women whose technical abilities, whose place in their world, have long been questioned. They have been treated like fakes and posers and interlopers and arm candy. But they are here and have always been here. And when all the bad men who “do good work” have fallen from their pedestals, those women are waiting, ready to inherit the tech industry.
«
Such a clever idea. Hide it from everyone except those who also know it, so that you can be sure that you all agree before going public. (Could such a system be used for the accused in rape trials?)
link to this extract
Phone screen, heal thyself • CCS Insigh
»
Researchers at the University of Tokyo have discovered a new polymer that can actually heal itself, pointing the way to a future of self-healing phone screens.
There’s been ongoing efforts to improve the strength of displays on smartphones and tablets, and there’s no denying that they’ve become tougher. Nonetheless, round-the-clock smartphone use has increased the potential for drops and smashes. Screens are getting damaged all the time.
The polymer was discovered by accident by a Japanese graduate student, Yu Yanagisawa, who thought the material would become a type of glue. He found that cut edges of the polymer would stick to each other, and formed a strong sheet after being compressed by hand at 21 degrees Celsius.
The findings of a team of researchers led by Professor Takuzo Aida have been published in Science magazine. Titled Mechanically robust, readily repairable polymers via tailored noncovalent cross-linking, the research promises a hard glass-like polymer called polyether-thioureas that can heal itself with only hand pressure. This makes it different from other materials that need high heat to recover from a break.
«
CCS Insight reckons between 10% and 15% of smartphone owners crack or smash a display every year. It’s a big business.
link to this extract
What do you call a world that can’t learn from itself? • Eudaimonia
»
There is a myth of exceptionalism in America that prevents it from looking outward, and learning from the world. It is made up of littler myths about greed being good, the weak deserving nothing, society being an arena, not a lever, for the survival of the fittest — and America is busy recounting those myths, not learning from the world, in slightly weaker (Democrats) or stronger (Republicans) forms. Still, the myths stay the same — and the debate is only really about whether a lightning bolt or a thunderstorm is the just punishment from the gods for the fallen, and a palace or a kingdom is the just reward for the cunning.
Hence, I have never once sees in America a leader saying, “hey! See that British healthcare system? That German union and pension system? Why don’t we propose that? They work!!” Instead, the whole American debate is self-referential — pundits debating Andrew Jackson (LOL) instead of, say, what the rest of the world does today in 2017. How can a broken society grow only by looking inwards? If you are a desperate, heart-broken addict, what can you learn from yourself? Won’t you only, recounting your pain, reach for the needle quicker?
«
This is a fabulous essay. As he points out, American life expectancy is also lower than you’ll find in comparable European countries, and as he also notes:
»
The same is true for things like maternal mortality, stress, work and leisure, press freedom, quality of democracy — every single thing you can think of that impacts how well, happily, meaningfully, and sanely you live is worse in America, by a very long way.
«
But as he also points out, neither is learning the lessons of the other.
link to this extract
Errata, corrigenda and ai no corrida: none notified