“Hey, Miss Lawrence! My name’s iCloud! What’s your password?” Photo by YourWay Magazine on Flickr.
You can now sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
A selection of 12 links for you. Use them wisely. I’m charlesarthur on Twitter. Observations and links welcome.
The disturbingly simple way dozens of celebrities had their nude photos stolen » Fusion
»According to court documents, Collins gained access to the intimate images of nude celebrities via a disturbingly simple technique: phishing.
Though many people assumed that the hacker took advantage of an iCloud vulnerability to brute-force his way into the celebrities’ accounts, the government makes no mention of that. Instead, it says that Collins hacked over 100 people by sending emails that looked like they came from Apple and Google, such as “e-mail.protection318@icloud.com,” “noreply_helpdesk0118@outlook.com,” and “secure.helpdesk0019@gmail.com.” According to the government, Collins asked for his victims’ iCloud or Gmail usernames and passwords and “because of the victims’ belief that the email had come from their [Internet Service Providers], numerous victims responded by giving [them].”
Celebrities really need better computer security advisers. If a dedicated enough attacker comes at you, it’s hard to avoid being compromised, but it helps immensely to turn on two-factor authentication for your online accounts. That way a person needs not just your password but a code sent to your phone to get into your account.
Once Collins had their credentials, says the government, he went through their email accounts looking for nude photos and videos. The government says that Collins got into approximately 50 iCloud accounts and 72 Gmail accounts this way, most of them belonging to celebrities. He “accessed full Apple iCloud backups belonging to numerous victims, including at least 18 celebrities” and “used a software program to download those full Apple iCloud backups.”
Ironically, that program was likely one that’s used by law enforcement to get evidence from phones.
«
The idea that someone had used a cutting-edge brute-force attack to break into the passwords always seemed like vapour trails to me. Social engineering is the Occam’s Razor explanation (and also the Hanlon’s Razor explanation) to stuff like this.
link to this extract
Exclusive: Chinese hackers behind U.S. ransomware attacks – security firms » Reuters
»executives of the security firms have seen a level of sophistication in at least a half dozen cases over the last three months akin to those used in state-sponsored attacks, including techniques to gain entry and move around the networks, as well as the software used to manage intrusions.
“It is obviously a group of skilled of operators that have some amount of experience conducting intrusions,” said Phil Burdette, who heads an incident response team at Dell SecureWorks.
Burdette said his team was called in on three cases in as many months where hackers spread ransomware after exploiting known vulnerabilities in application servers. From there, the hackers tricked more than 100 computers in each of the companies into installing the malicious programs.
The victims included a transportation company and a technology firm that had 30 percent of its machines captured.
Security firms Attack Research, InGuardians and G-C Partners, said they had separately investigated three other similar ransomware attacks since December.
Although they cannot be positive, the companies concluded that all were the work of a known advanced threat group from China, Attack Research Chief Executive Val Smith told Reuters.
«
Reformed LulzSec hacktivist joins payments firm » The Register
»A payments firm has hired reformed LulzSec hactivist Mustafa Al-Bassam (formerly known as tFlow) for a new blockchain research project.
London-based payments group Secure Trading has taken on Al-Bassam to help develop a platform that applies the verification benefits of blockchain technology in order to improve the visibility and security of online payments. Codenamed “Trustery”, the project aims to create a commercial platform.
Secure Trading approached Al-Bassam, who agreed to work for the firm part time while continuing his computer science degree at King’s College London.
«
Smart move: al-Bassam is a clever guy.
link to this extract
Crypto-ransomware spreads via poisoned ads on major websites » Tripwire
»Some of the world’s most popular news and entertainment websites have been spreading poisoned adverts to potentially hundreds of thousands of visitors, putting innocent readers at risk of having their computers hit by threats such as ransomware.
Famous sites which displayed the malicious ads and endangered visiting computers include MSN, bbc.com, the New York Times, AOL and Newsweek.
As a result, researchers at Malwarebytes say that they saw a “huge spike in malicious activity” over the weekend.
Security analysts at TrendLabs and Malwarebytes report that the attack is one of the largest ransomware campaigns seen in years, taking advantage of a recently-updated version of the notorious Angler Exploit Kit to spread malware.
Just last month the Angler Exploit Kit was found to be targeting PCs and Macs after it was updated to take advantage of a known vulnerability in Microsoft Silverlight…
…It seems glaringly apparent to me that there is so much malicious advertising on the internet that anytime you surf even legitimate sites without an ad blocker in place, you are putting your computer’s data at risk.
«
Why is the Nokia 105 cellphone a favourite among ISIS fighters? » NBC News
»The must-have cellphone for ISIS fighters in Iraq doesn’t have apps or a camera, and ships for less than $30.
The small and simple Nokia model is frequently used as a trigger device to set off ISIS’ improvised explosive devices, known as IEDs, according to a Conflict Armament Research report released last month.
As part of a study looking at civilian components in ISIS bombs, CAR documented 10 of the phones captured from members of the terror group in Iraq in December 2014.
The research showed the terror group “consistently” used the Nokia 105 above all others “in the manufacture of a specific type of remote controlled IED.”
Two phones are used in the bomb-making process: one to call the other, which then sends a signal to a circuit board and sparks the explosion.
There are plenty of other cheap, durable phones with long battery life that ISIS fighters could use — and yet this particular model, also branded as the Microsoft Mobile 105 after the tech giant bought Nokia in 2014, shows up again and again.
«
I’m sure there’ll be widespread condemnation of Microsoft for aiding terrorists any moment now.
link to this extract
Why Sony will win first in VR » Jon Peddie Research
»Now that Oculus has revealed its consumer version of the Rift HMD, consumers can start planning how they might engage with VR, and they have a choice—a DIY rig with a PC and Rift, or a turn-key system with Sony.
Sony’s HMD will be about 30% less expensive than the Oculus HDM. And Sony buyers probably already have a PS4, and possibly PS4 accessory controllers. Most importantly, Sony also has content.
«
So, first couple of rounds to Sony.
link to this extract
The best things in Android are free — with in-app purchases » Medium
»A year ago, iA Writer for Android entered the Play Store. So far, we have sold a little more than 6’000 apps. At a price of 1 to 5 Dollars, this doesn’t cover much more than one month of app development. So we decided to go free and add in app purchases later.
We are not sure why apps sell in the Apple universe but not in the Android world. It just seems to be a hard cold fact:
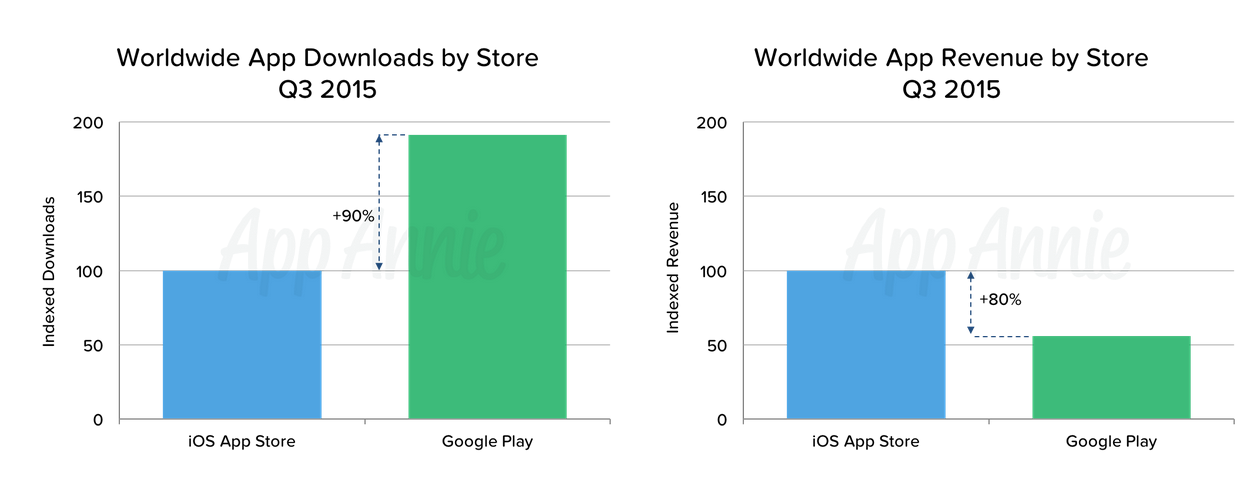
Worldwide App Downloads by Store vs Worldwide App Revenue by StoreLooking at the sales numbers of paid Android apps it becomes apparent that plain paid offerings just do not get traction on Android. Why? We are not sure. Here is what we have learned.
«
There’s a point in there about price elasticity which is remarkable. But also that stuff with an upfront price tag does not sell.
link to this extract
Windows 10 Store will continue to support bitcoin » Softpedia
»while there was a lot of speculation online regarding the removal of Bitcoin support for new deposits in the Windows Store – some people said it’s because of the limited adoption of Bitcoin – it appears that the change made to the FAQ page was just “a mistake.”
In other words, Microsoft will continue to support Bitcoin in the Windows Store, so you can keep on using the digital currency for new deposits. A statement we received from a Microsoft spokesperson a few minutes ago provides us with some details on this:
“We continue to support Bitcoin for adding money to your Microsoft Account which can be used for purchasing content in the Windows and Xbox stores. We apologize for inaccurate information that was inadvertently posted to a Microsoft site, which is currently being corrected.”
«
Would love to know what volume of transactions they see.
link to this extract
Top NFL official acknowledges link between football-related head trauma and CTE for first time » ESPN
»The NFL’s top health and safety officer acknowledged Monday there is a link between football-related head trauma and chronic traumatic encephalopathy, or CTE, the first time a senior league official has conceded football’s connection to the devastating brain disease.
The admission came during a roundtable discussion on concussions convened by the U.S. House of Representatives’ Committee on Energy and Commerce. Jeff Miller, the NFL’s senior vice president for health and safety, was asked by Rep. Jan Schakowsky, D-Ill., if the link between football and neurodegenerative diseases such as CTE has been established.
“The answer to that question is certainly yes,” Miller said.
«
A bit like boxing: does it mean people will be put off the potentially fabulous riches? But equally: will parents be less likely to put their children into it? The public admission is important.
link to this extract
Teenager wins $250,000 in biggest drone race yet » The Verge
»The sport has already attracted investment from the likes of NFL team owners, but it still has some way to go before it breaks into the mainstream. Particularly difficult is the question of how to actually observe the races. Drone pilots fly their racing craft in first-person, using special headsets to see as the drone sees, but for observers the footage can feel — and sound — like being strapped to the front of a particularly excitable wasp. A second camera following the action might help human brains contextualize the movements in space, but some of the nascent racing leagues set their courses inside buildings, making a chase camera’s operation difficult. Still, though, the speed of the craft and the deftness of his control make watching [15-year-old winner] Luke [Bannister]’s victory from Dubai an exhilarating — if slightly nauseating — experience.
«
Dubai, of course.
link to this extract
Music streaming has a nearly undetectable fraud problem » Quartz
»For an in-depth look into how click fraud works, there’s Sharky Laguana’s thorough explanation here. Laguana—a music industry veteran who now owns a rental company—tells Quartz it certainly wouldn’t be hard to run the “perfect” scheme to con Spotify. First, set up a couple hundred fake artists. Next, upload some auto-generated tunes—mediocre dance music is particularly easy to “produce” online—and just make sure your bots click on an array of songs both real and fake, so no one gets suspicious. (He uses Spotify as an example because of its size, but the scheme could theoretically work for any music subscription service.)
“If it’s done properly, it’s nearly impossible to detect,” says Laguana. “There’s no way to know why somebody chose to click on something.”
«
Should we just turn off the internet?
link to this extract
Donald Trump, America’s own Silvio Berlusconi » The Intercept
»Neither Trump nor Berlusconi has a real political program; what they are selling is themselves. Berlusconi used to say that what Italy needs is more Berlusconi. I recall a very telling moment in his first election campaign: During a TV debate, his opponent, the economist Luigi Spaventa, was pointing out the holes and inconsistencies in Berlusconi’s economic program, and Berlusconi stopped him mid-sentence and pointed to the victories of his soccer club, AC Milan: “Before trying to compete with me, try, at least, winning a couple of national championships!” The remark had the air of unassailable truth — however irrelevant it might be to Berlusconi’s fitness to govern. Similarly, when asked how he is going to get Mexico to pay for a giant wall between its country and ours, Trump simply responds, “Don’t worry, they’ll pay!”
Yet there is another element — a systemic one — that helps explain why Italy and the U.S. are the only major democracies in which a billionaire circus has raised its tent: the almost total deregulation of broadcast media.
«
The latter matters, as Stille explains. (Via @papanic.)
link to this extract
Errata, corrigenda and ai no corrida: