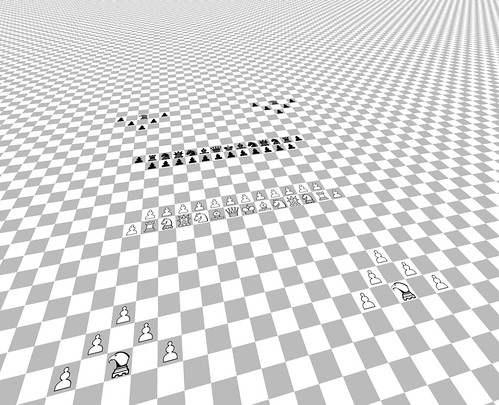
If you set two AIs playing chess on an infinite board… what would happen? CC-licensed photo by QyiQ23607 Pisano on Flickr.
You can sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam.
A selection of 10 links for you. Charity suggestions at end. I’m @charlesarthur on Twitter. Observations and links welcome.
Facebook bans seven ‘cyber mercenary’ companies from its platforms • The Guardian
Stephanie Kirchgaessner and Michael Safi:
»
The social media company said on Thursday that its investigation had revealed new details about the way the surveillance companies enable their clients to “indiscriminately” target people across the internet to collect intelligence about them, manipulate them – and ultimately compromise their devices.
Among the surveillance companies that Facebook named in its investigation and banned from its platforms are:
• Black Cube, an Israeli company that gained notoriety after it emerged that the disgraced media mogul and convicted sex offender Harvey Weinstein had hired them to target women who had accused him of abuse. Black Cube rejected Facebook’s claims about its activities
• Cobwebs, another Israeli company that Facebook said enabled its clients to use public websites and dark web sites to trick targets into revealing personal information. The company also reportedly works for US clients, including a local police department in Hartford, Connecticut
• Cytrox, a North Macedonian company that Facebook said enabled its clients to infect targets with malware following phishing campaigns.The investigation conducted by Facebook comes as the company is itself facing intense scrutiny in Washington and around the world following accusations by a whistleblower, Frances Haugen, that it enabled the spread of hate speech and disinformation.
The Facebook investigation is significant, however, because it reveals new details about the way parts of the surveillance industry use social media – from Facebook to Instagram – to create fake accounts to deceive their targets and conceal their own activities.
While many of the companies claim that they are hired to target criminals and terrorists, Facebook said the industry “regularly” enabled its clients to target journalists, dissidents, critics of authoritarian regimes and human rights activists and their families.
«
Sure that the US administration will be along in a minute to sanction Facebook like it did NSO. (There’s also the obvious joke – FB exec: “intrusive, constant surveillance? That’s our job!”)
unique link to this extract
There is no ‘Them’ • The Pull Request
Antonio García Martínez:
»
the real problem with the ‘Them’ [as he found a group of non-tech friends complaining about the Techopoly, thus viewed, to him a technologist who used to work at Facebook]: it ascribes a level of wilful agency to organisations (or entire industries) which are really baskets of disparate individuals and agendas grappling with happenstance and an intractable reality. It’s an illusion only readily maintained by outsiders, as insiders have seen how the sausage is really made. Nobody who’s opened a Facebook dashboard and seen figures in the billions blinking back at them would believe that any ‘Them’ could possibly manipulate this seething mass of humanity in a controlled, willful way.
The real Facebook struggle is to somehow manage all this complexity in scalable ways: an algorithm that sorts the billions of pieces of content created per day; machine learning that hopefully doesn’t filter out the noxious detritus of imperfect humanity in too, too wrong a way; some imperfect body of policies that placates often incomprehending regulators and is still implementable by overtaxed operations people. The thought that any set of people, no matter how motivated, could deploy grand designs of overt social control over that globe-spanning mess seems delusional when you realize the scale of it.
When our car gets stuck in the snow on the way to Tahoe, we don’t blame President Biden; well, some political partisans people might, and who knows, poor Federal infrastructure policy might be residually to blame for that poorly-marked turn we missed. But broadly we ‘get’ that national governance is a complicated, multi-tiered phenomenon, and assigning individual agency to this or that person or policy comes off as contrived. Somehow that worldliness disappears (or didn’t exist to begin with) when it comes to tech, which still confronts this unbridgeable chasm when it comes to explaining itself to the normies (and believe me, some have tried).
«
Martínez is smart, though I feel he’s a step away from realising that the fact he’s describing a system that’s impossible to control by its nature doesn’t absolve those who created the system from blame.
unique link to this extract
• Why do social networks drive us a little mad?
• Why does angry content seem to dominate what we see?
• How much of a role do algorithms play in affecting what we see and do online?
• What can we do about it?
• Did Facebook have any inkling of what was coming in Myanmar in 2016?
Social Warming, my latest book, and find answers – and more.
Toyota made its key fob Remote Start into a subscription service • The Drive
Rob Stumpf:
»
Remember when BMW wanted to charge drivers to use Apple CarPlay? How about the subscription required for the Mercedes EQS’s rear-wheel steering functionality in Europe? It turns out that luxury marques aren’t the only ones looking to cash in on that sweet, sweet software as a service cash: Toyota has been testing the waters by making the remote start functionality on your proximity key fob part of a larger connected services subscription.
Yes, it appears the pay-to-play ethos that’s spreading around the industry has reached the world’s largest automaker. A Toyota spokesperson confirmed to The Drive that if a 2018 or later Toyota is equipped with Toyota’s Remote Connect functions, the vehicle must be enrolled in a valid subscription in order for the key fob to start the car remotely. To be clear, what we’re talking about is the proximity-based RF remote start system, where you press a button on the fob to start the car while outside of it within a certain distance—say, from your front door to warm up your vehicle in the driveway on a cold morning before you get in. Your fob uses radio waves to communicate with the car, and no connection back to Toyota’s servers is needed. But the function will not work without a larger Remote Connect subscription.
«
That’s a tasty $8 per month or – discount! – $80 per year. How would you like to pay? Now, the story clarifies that the free period might be up to 10 years. But that’s only might. Who knows if Toyota might find itself a bit squeezed on cashflow some day? The mission creep of subscriptions into all sorts of places they’re not wanted continues.
unique link to this extract
Omicron variant may multiply 70 times faster than delta • USA Today
John Bacon and Celina Tebor:
»
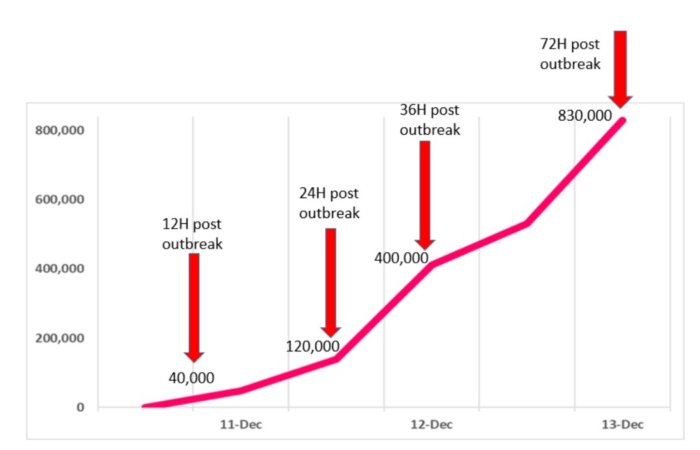
The omicron variant multiplies 70 times faster in the human bronchial tubes than the initial COVID-19 infection or the delta variant, according to a new study from the University of Hong Kong.
The lightning-fast spread within people may explain why the variant may transmit faster among humans than previous versions, the researchers say. Their study also showed the omicron infection in the lung is significantly lower than the original SARS-CoV-2, which may be an indicator of lower disease severity. The research is currently under peer review for publication.
By infecting many more people, a very infectious virus may cause more severe disease and death even though the virus itself may be less dangerous, said Dr Michael Chan Chi-wai, the study’s principal investigator.
“Taken together with our recent studies showing that the omicron variant can partially escape immunity from vaccines and past infection, the overall threat from omicron variant is likely to be very significant,” he said.
The US Centers for Disease Control and Prevention says the omicron variant has now been reported in at least 36 states and 75 countries. Schools and businesses are grappling with how to manage the latest threat.
«
I hadn’t seen (or heard) that 70x figure before, but it fits in with other stuff that’s been floating around, about the RBD (receptor binding domain – the bit that latches on to the cell surface) having much stronger affinity for ACE2, the cell protein that it binds to. If it can attach better then it would be more likely to penetrate the cell and reproduce. Omicron is very much out of control now in the UK.
unique link to this extract
Fact check: did Jimmy Carter stop a nuclear reactor from destroying Ottawa? • Newsweek
Ewan Palmer:
»
On December 12, 1952, the Chalk River NRX nuclear reactor suffered a partial meltdown. The incident resulted in hundreds of thousands of gallons of radioactive water flooding the core and causing major damage to the reactor.
As reported by nuclearenergy.net, the major failure, along with “several poor decisions by facility operators,” resulted in a nuclear fission chain reaction that caused the power level to rise exponentially.
At the time, the NRX reactor operated at around 30 megawatts (MW). On December 12, workers at the plant were preparing for a reactor-physics experiment at low power. However, a defect in the NRX shut-off rod mechanism, combined with the human errors, caused a temporary loss of control over reactor power, ultimately causing it to surge to between 60 and 90 MW.
“This energy load would normally not have been a problem, but several experimental fuel rods that were at that moment receiving inadequate cooling for high power operation ruptured and melted,” the FAQ section of the Canada Deuterium Uranium (CANDU) reactor website states.
Thousands of nuclear fission particles were released into the atmosphere. The radioactive water also ended up in the reactor building’s basement, before being pumped out into shallow ditches near the Ottawa River.
The US was then called in to help with the clean up the site. [Jimmy] Carter, a trained nuclear engineer who had worked under famed Admiral Hyman Rickover, the father of the Navy’s nuclear program on the atomic submarine “Sea Wolf,” was asked to lead a team for the cleanup operation.
The Historical Society of Ottawa said that as part of the cleanup plan, the reactor had to be shut down, disassembled and replaced, with the team also needing to clean any spilled radioactive material. The intensity of the radiation meant that Carter and each member of his team could only spend about ninety seconds at the core location. Before the operation, which involved being lowered into the core, an exact replica of the reactor was built on a nearby tennis court, where Carter and his men practiced cleaning and repairing it.
Carter described the operation in his book, Why Not the Best?, which he released while running for president in 1976. “We all went out on the tennis court, and they had an exact duplicate of the reactor on the tennis court. We would run out there with our wrenches and we’d check off so many bolts and nuts and they’d put them back on,” Carter told Canadian journalist and author Arthur Milnes.
«
The accident is now rated 5 out of 7 on the severity scale. (Chernobyl, of course, was a 7.)
Jimmy Carter is 97 years old.
unique link to this extract
Apple may be making standalone 4K monitors to match the iMac • Macworld
Michael Simon:
»
If there’s one gaping hole in Apple’s lineup, it’s a standalone display that doesn’t cost $4,999 (without a stand). But according to a new rumor, that might change in 2022.
We’ve heard previous rumors that Apple is working on a display to go with its M1 Macs, but a new report sheds a little more light on what Apple has in mind. According to Twitter user Dylan, who has previously leaked accurate information about the 24-inch iMac and iPhone 13, LG is manufacturing two displays “encased in unbranded enclosures for usage as external monitors that are in early development” that “have the same specifications as the upcoming 27in and current 24in iMac displays.”
LG makes many of Apple’s current displays, including the ProDisplay XDR, so based on the specs and the secrecy, it’s likely that these are bound for use in an Apple product.
«
Apple used to do displays, then it didn’t for a long time (or let them become hopelessly out of date), then it did but they were wildly expensive. For years people have been asking for a 5K display like that used for the iMac 5K, but without the “iMac” bit. Most would probably settle for the 4K format.
unique link to this extract
Meta opens up access to VR social platform Horizon Worlds • The Verge
Alex Heath:
»
During a demo of Horizon Worlds, I was greeted by a few Meta employees at the Plaza, a central gathering place used to enter custom worlds and games built by users. We first visited a creator lounge area where you try custom items being built, like a bow and arrow or paper plane launcher, and enter building competitions to win cash prizes. Then we hopped to another world and divided up into teams to play a battle royale shooting game. After that, I was given a demo of Horizon’s building tools that let you create a world and items from scratch.
A key part of Horizon Worlds is the ability to write basic code that sets rules for how objects work, such as a gun shooting when you press the trigger or a ball bouncing when it touches a surface. The code, which Meta calls script blocks, acts similarly to layers in Photoshop by letting you chain together rules to create complex interactions, such as a leaderboard that automatically updates after a game is finished. “Attaching behaviors to objects is actually one of the biggest innovations that I’m proud of for the team,” says Sharma.
He says that, so far, Meta employees have been making the script blocks at the request of beta testers and that the company eventually plans to release a free library of them. An asset library of objects is also coming. Right now, the coding for script blocks is done entirely in VR, but eventually, Meta plans to let them be built from a desktop computer.
Safety is a big concern for a VR environment like Horizon Worlds, where you can easily interact with someone you don’t know. Earlier this month, a beta tester posted in the official Horizon group on Facebook about how her avatar was groped by a stranger. “Sexual harassment is no joke on the regular internet, but being in VR adds another layer that makes the event more intense,” she wrote. “Not only was I groped last night, but there were other people there who supported this behavior which made me feel isolated in the Plaza.”
Sharma calls the incident “absolutely unfortunate” and says that after Meta reviewed the incident, the company determined that the beta tester didn’t utilize the safety features built into Horizon Worlds, including the ability to block someone from interacting with you. (When you’re in Horizon, a rolling buffer of what you see is saved locally on your Oculus headset and then sent to Meta for human review if an incident is reported.) “That’s good feedback still for us because I want to make [the blocking feature] trivially easy and findable,” he says.
«
Between this and Parmy Olson’s experience recounted in yesterday’s roundup, something tells me that the metaverse already has a harassment problem, and solving it isn’t about having controls be “trivially easy and findable”. It’s about defaults.
unique link to this extract
The hidden world of Ethereum snipers • Sam Chepal
Samneet Chepal:
»
Despite its massive success as a protocol, many users are not aware of the fact that anytime a transaction is made it might be in the crosshairs of a hyper-optimized sniper bot. These sophisticated bots are fine-tuned around the core technological architecture of Ethereum to hunt for profitable opportunities. Earlier this year it was not uncommon to see these bots make more than $250k in a single trade. Many stories have already been documented on the dangers of these bots such as Dan Robinson’s journey into the Dark Forest and samczun’s escape from the Dark Forest. Fortunately, recent innovations within the Ethereum eco-system have been developed to help reduce the negative externalities of these snipers.
…Suppose XYZ token is trading for $100 on Uniswap but $120 on Sushiswap. A simple arbitrage strategy would be to buy XYZ token for $100 on Uniswap and sell the same token on Sushiswap at $120, resulting in an arbitrage of $20. An arbitrageur would submit both trades at the same time to ensure the position is opened and closed in the same transaction which ensures a relatively risk-free profit. In this case let’s suppose the arbitrageur sends over this transaction with a gas transaction fee worth $5, leaving him with a net profit of $15.
When the arbitrageur submits this transaction to the network, he’s unaware that sniper bots are sniffing through the mempool looking for any exploitable opportunities. Given this user’s trade is publicly available for anyone to see before it becomes finalized in the blockchain, a sophisticated sniper bot could front-run this user by simply bribing the miner with higher gas fees. In this case the sniper bot would simply copy the exact same trade as the arbitrageur but offer a slightly higher gas fee of $10, leaving the sniper bot with a net profit of $10. Ironically, this bot may get sniped by another bot willing to pay a higher gas fee bribe to the miner. This new sniper bot may be willing to pay $15 worth of transaction fees to collect a net arbitrage profit of $5.
«
But – and it’s an important but – only one can succeed, because the transaction can only happen once.
unique link to this extract
Melania Trump launches NFT venture, promising ‘an amulet to inspire’ • The Guardian
David Smith:
»
In Melania’s first public venture since leaving the White House almost a year ago, an NFT named Melania’s Vision can be bought between 16 and 31 December with the SOL cryptocurrency or an old-fashioned credit card.
An irony-free statement from her office says it is “a breathtaking watercolor art by Marc-Antoine Coulon, and embodies Mrs Trump’s cobalt blue eyes, providing the collector with an amulet to inspire.”
“The limited-edition piece of digital artwork will be 1 SOL (approximately $150) and includes an audio recording from Mrs Trump with a message of hope.”
Melania, 51, joins a growing list of celebrities offering lucrative digital memorabilia. Earlier this year Argentinian footballer Lionel Messi, Jamaican athlete Usain Bolt and American football player Tom Brady launched their own collections of NFTs. Singer Justin Bieber and K-pop group BTS have also dived in.
«
The absolutely perfect intersection of grifts.
unique link to this extract
The biggest chess game ever • YouTube
Lex Fridman:
»
It’s two Stockfish 14 chess AI engines playing each other on a chess board that is infinitely expanding outwards, initializing the squares at the edges with middlegames from 30,000 grandmaster games including from Carlsen, Fischer, Kasparov, Spassky, Tal, Karpov, and so on.
I love chess, always have, but chose to stop playing it myself early on when I became passionate about building AI systems, and instead became a fan of watching the game and the humans who play it.
«
The commentary explains plenty more. (It’s a terrific choice of music too.) Whenever people start suggesting that maybe, just maybe a super-capable chess AI might in some way be showing us what a generalised intelligence might be like, I’m reminded of the satirical SF writer John Sladek’s book “The Reproductive System”, in which a huge machine takes over the world. Someone asks it to identify itself, and it produces a long response; “then, as if to be on the safe side, added ‘P-Q4’.”
unique link to this extract
Errata, corrigenda and ai no corrida: I’ve been lax in suggesting charities to give to at Christmas. (There’s another week coming, so stay with it.) But if you want to get your donations on early, I’d suggest all or any of:
• Shelter (or equivalent in your country)
• Wikipedia (it’s an invaluable, unique resource)
• the Internet Archive (ditto)
• any dog rescue centre (dogs are a source of joy and inspiration: watch Lollipop and then try to deny that). Here’s Lollipop’s home.