Donald Trump could be good for them, or their offspring. Joi Ito can explain. Photo by StreetFly JZ on Flickr.
You can now sign up to receive each day’s Start Up post by email. You’ll need to click a confirmation link, so no spam. Offer it to a friend as a present – it’s free!
A selection of 11 links for you. Boom. I’m @charlesarthur on Twitter. Observations and links welcome.
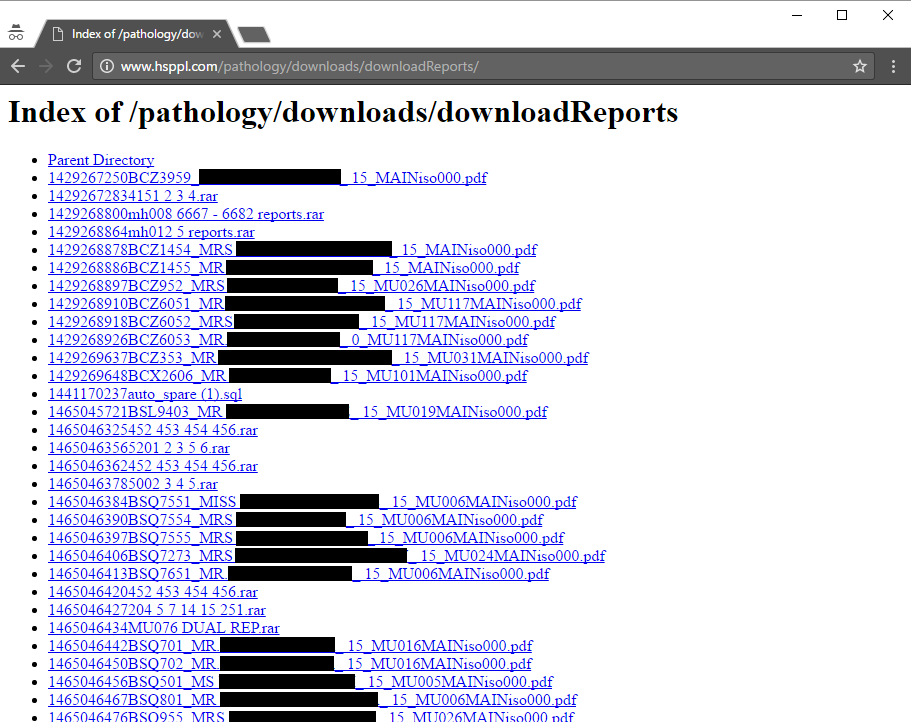
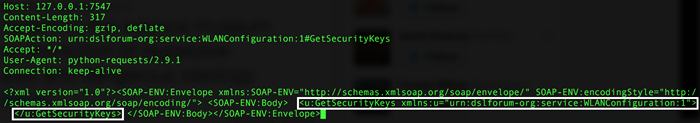
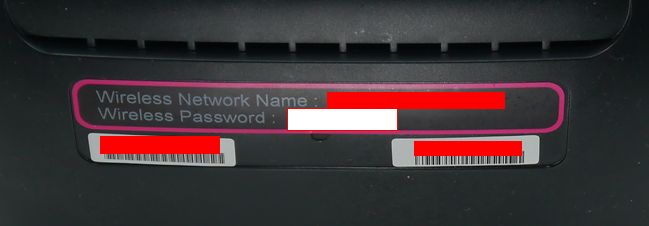
TalkTalk’s wi-fi hack advice is ‘astonishing’ • BBC News
»
TalkTalk’s handling of a wi-fi password breach is being criticised by several cyber-security experts.
The BBC has presented the company with evidence that many of its customers’ router credentials have been hacked, putting them at risk of data theft.
The UK broadband provider confirmed that the sample of stolen router IDs it had been shown was real.
But it is still advising users that there is “no need” to change their routers’ settings.
A cyber-security advisor to Europol said he was astounded by the decision. “If TalkTalk has evidence that significant numbers of passwords are out in the wild, then at the very least they should be advising their customers to change their passwords,” said the University of Surrey’s Prof Alan Woodward. “To say they see no need to do so is, frankly, astonishing.”
A spokeswoman for TalkTalk said that customers could change their settings “if they wish” but added that she believed there was “no risk to their personal information”.
She referred the BBC to another security expert. But when questioned, he also said the company should change its advice.
«
Read on for the amazing denial about the trouble it’s in: there’s a huge list of routers and passwords out there. TalkTalk’s response: “We see no huge list.”
TalkTalk really doesn’t have a grip on security topics.
link to this extract
Samsung S8: new Galaxy phone to lose headphone jack and home button and be one big screen, just like iPhone 8 • The Independent
»
Samsung is about to launch a new phone that will include all of the iPhone 8’s biggest features.
The upcoming Galaxy S7 will drop the physical home button so that the entirety of the front of the phone can be one big screen, according to reports. That will allow it to have much the same design as the one rumoured for the upcoming iPhone 8 – which is also expected to be made entirely of glass and not have any bezel.
The new phone will also lose the headphone jack, according to reports. Apple dropped the headphone jack in its last iPhone, telling people to use wireless headphones instead, a decision that caused huge controversy.
«
Urr, but the iPhone 7 doesn’t have a physical home button. That is, not a moving one. It’s a Force Touch, or 3D Touch, or whatever we call it, “button”. So the big wraparound screen might be new, but the other two things aren’t.
Not sure Samsung will do well with the S8 without a headphone jack, though. Feel like that could see a lot of returns unless it includes a USB-C-to-3.5mm jack. Not even sure those exist.
link to this extract
Trump invites tech leaders to roundtable next week • USA Today
»
President-elect Donald Trump has invited technology industry leaders to a roundtable next week in New York.
The invitation for the Dec. 14 summit was sent by Trump’s chief of staff Reince Priebus, Jared Kushner, Trump’s son-in-law, and transition team adviser Peter Thiel. Among the CEOs who plan to attend the meeting are Cisco CEO Chuck Robbins and Oracle Co-CEO Safra Catz.
The tech industry, which bet heavily on Hillary Clinton in the months leading up to the presidential election, is looking to build bridges to the incoming administration…
…Facebook declined to comment whether it would attend next week’s tech roundtable. [Peter] Thiel [who is advising the Trump transition team] sits on the board of the giant social network.
Leading Silicon Valley companies such as Alphabet’s Google declined to comment.
Meg Whitman, the CEO of Hewlett Packard Enterprise and self-described “proud Republican” who had supported Trump rival Hillary Clinton in the campaign, won’t attend, the company said.
«
Do we think Twitter will attend, and will upbraid Minority Donald for offensive tweeting aimed at individuals?
link to this extract
Windows 10 on ARM: Microsoft’s key to the Chromebook market • Windows Central
»
Microsoft has announced that the full version of Windows 10 is coming to ARM, with x86 support meaning your Win32 desktop applications won’t be missing like they were on Windows RT. This opens up a whole world of new opportunities for OEMs, and indeed Microsoft, to build low-cost and low-powered Windows 10 devices that can directly take on Chromebooks.
If you were to tell me a few years ago that Chromebooks would actually be a big deal and a possible threat to Windows, I’d have probably laughed in your face. I remember thinking “A laptop that’s just a browser? There’s no way that’ll catch on”. I know many don’t consider the rise of Chromebooks to be a threat to Microsoft or Windows 10, but they very much are. More and more schools and businesses are opting for Chromebooks over Windows 10 laptops, mainly because of price, but also because Chromebooks do what they need them to do, durably, and at a low cost.
«
There’s a lot of hope in the Windows enthusiast market that this latest version of Windows on ARM (WoA) will, unlike 2011’s version, be a really amazing implementation, rather than a milquetoast version which can’t run x86 apps.
The good news: they will be able to run x86 apps, through virtualisation. The bad news: they’ll be doing it on really underpowered CPUs. True, you don’t need a lot of power to compete with Chromebooks; but Chromebooks are already getting their market. It feels like another proof-of-concept.
For more, read Wes Miller’s 2012 thoughts on “architectural escape velocity“, which deals with the first attempt at WoA; then read his latest thoughts on this new announcement.
link to this extract
Bluetooth 5: What you need to know about the new wireless technology • Daily Telegraph
»
Bluetooth 5 is twice as fast as its predecessor and can connect devices at quadruple the range, making it more reliable for use outside and around the whole of a house.
The bandwidth on Bluetooth 5 is 2 Mbps up from 1 Mbps, which means devices with the new standard will be able to transfer twice as much data, as well as making it quicker to send and receive information.
This means devices will be able to download updates in less time, and export collected information, for example from a sensor, at fast speeds.
A longer range, of up to four times that of Bluetooth 4.2LE (low energy), means smart home devices such as security cameras will be able to cover the entirety of a house. Improved ability to detect and prevent interference from other devices helps improve signal too.
«
Basically it’s approaching the point where it will be Wi-Fi.
link to this extract
Who killed Pebble? Easy: The vulture capitalists • The Register
Andrew Orlowski wraps up Pebble’s history, with this coda:
»
In 2013 Charles River Ventures had handed Pebble $15m in funding. A venture capitalist at CRV, George Zachary, who owed his reputation to funding Twitter early, took a seat on the Pebble board.
Few smartstraps ever appeared. The colour Pebbles didn’t have such a great display after all, as we found. The non-Gorilla Glass model scratched easily. The software took the user experience backwards in a few ways: slower, and more cumbersome. After that, successive firmware updates were slow and often buggy. A “Round” model announced later that year was an attempt to make a more stylish and better looking timepiece, but the cost was a big fall in battery life, to about a day.
“Pebble has strayed further away from its hobbyist DIY roots,” we noted.
Pebble had benefited from the smartwatch hype but it was catching a cold from the backlash. Pressure from investors caused it to move further from its DIY roots and go for “health”. Why? Well, now we know. That’s where the VC community had decided a buyer would come from, allowing the funds to cash in their chips.
Pebble was being touted for a sale. Fitbit had made a successful flotation on the stock exchange, so had cash to spare, and won.
«
Joi Ito explains why Donald Trump is like the Sex Pistols • Medium
Steven Levy interviewed Joi Ito, who is has written a book about his ideas as head of the MIT Media Lab:
»
Ito: We write about what’s going on in the world today in a upbeat way because we want people to lean into it, but it’s not like only the good guys can use it. It just is. It’s the way everything is changing. Unless you figure it out, you’re not going to be able to keep up. Having said that, I don’t think that a lot of the people who voted for Trump are necessarily going to be up to speed on synthetic biology and AI.
Steven Levy: You don’t think?
Ito: No. But I think AI can be just as destructive for investment bankers and lawyers as it is for doctors. It could be that it will be empowering pharmacists who go to one year of community college and become a doctor — screw the whole medical school. Disruption doesn’t necessarily advantage those with power.
Levy: One theme of your book is disobedience over compliance. That seems to define the transition so far.
Ito: Absolutely. People want a culture change, and this moment reminds me of the beginning of punk rock, or the beginning of the hippie movement. But I’d hate for Trump to be our millennial Sex Pistols or Timothy Leary or the Beatles. We need something like the Beatles that captures the hearts and minds of people. We’re ripe for a new cultural movement. Culture movements and art and punk rock thrive under bad presidents. The music was better under Reagan and Nixon than it was under Obama. I think that the doomsday scenarios tend to promote the arts. A lot of my energy now is in trying to provide tools to the young people to try to organize.
«
Holy crap did I get the most annoying trojan attempt ever! • SuperGlobalMegaCorp
»
Sit down kids, it’s time for an old man rant.
So yeah, I have one of those clients who wants to use ‘one of those’ file sharing sites. UGH. I swear I’m to the point of just paying for an Office 365 subscription for them so I don’t have to deal with this kind of shit. So I hit the site on my phone, then it jumps to this genchatu.top site. Fantastic.
Then I’m alerted that my phone is 28.1% DAMAGED, and somehow my phone’s SIM card will be damaged! Yes, it’s one of these scam sites!
Oh no, my phone apparently may be already physically damaged? I guess this is once someone is tricked by this official Google looking image you’ll want to throw your phone against the wall. As any user of Android will tell you updates from Google are non existent, and anything that could infect your phone, well is pretty much your problem. You can beg the vendor, but lol, good luck.
I like to live dangerously, so yeah let’s look at the app.
So with this scary and official looking thing it’s trying to railroad you into “Ace Cleaner”. I don’t know how on earth they haven’t either been reported, or knocked out of the app store. I guess Google is busy teaming up with Facebook trying to figure out how to censor the news appropriately instead of trying to squash actual scam artists.
«
But as the reviews imply, these scams work. People download this stuff and it sits on their machines, and they probably don’t realise it’s watching everything they do.
link to this extract
We can fix it: saving the truth from the internet • Medium
»
Terrorism and radicalism thrive because of our current media system. It is no coincidence that terrorism has grown and ISIS taken root at the same time that internet media has grown. It is easy to create a cultish cocoon of lies with today’s media system and terrorists exploit it to the hilt. As we are learning from the Comet Ping Pong situation, that cocoon extends to home grown conspiracy theories.
Powerful states have found tools of oppression in the internet we designed. The Russian government spread false information in the Ukraine and United States during elections. When there is no accountability for the truth, information is manipulated by the powerful for their own ends. The risk will grow as authoritarians exploit the weaknesses we built into the system.
The state of media today is similar to the spam crisis of the late 1990s. The integrity of email was at risk because of a flood of spam, most of which was fraudulent, malicious, or questionable. We solved the spam problem with a combination of technology, changes in social incentives, and laws. Today spam is only an annoyance because we have anti-spam technology like Brightmail**, informal rules that email senders like MailChimp use to limit abuse, and laws that allow legal action against the worst offenders. Like with spam, fixing the internet media problem will take a similar full assault of new technology, social incentives, and laws.
«
It is an important point how easily we accepted that religious radicalisation could happen online, yet have been surprised by it happening politically through the same medium.
link to this extract
Help Wanted at Google • WSJ
The WSJ noticed that the search giant has advertised for a manager of “Conservative Outreach and Public Policy Partnerships.” The employee “will act as Google’s liaison to conservative, libertarian and free market groups” and will be “part organizer, part advocate and part policy wonk”:
»
Google no doubt planned to continue wielding influence in a Hillary Clinton Administration. Eric Schmidt, executive chairman of Google’s parent company, advised John Podesta and Mrs. Clinton’s campaign on digital strategy and targeting voters, though perhaps not in the Upper Midwest. A report from the Campaign for Accountability turned up 57 people affiliated with both Mrs. Clinton (whether her campaign, foundation or State Department) and Google entities.
Now Google will have to scramble to preserve its enormous influence on everything from copyrights to privacy regulation. Whether Mr. Trump will indulge rent-seeking from Google and friends is anyone’s guess. But maybe Google’s Republican unicorn can host a staff seminar on the free-market philosophy that made the tech giant possible.
«
Nothing pleases a right-wing paper more than a right-wing administration bending liberal companies to its will.
link to this extract
Millions exposed to malvertising that hid attack code in banner pixels • Ars Technica UK
»
Researchers from antivirus provider Eset said “Stegano,” as they’ve dubbed the campaign, dates back to 2014. Beginning in early October, its unusually stealthy operators scored a major coup by getting the ads displayed on a variety of unnamed reputable news sites, each with millions of daily visitors. Borrowing from the word steganography—the practice of concealing secret messages inside a larger document that dates back to at least 440 BC—Stegano hides parts of its malicious code in parameters controlling the transparency of pixels used to display banner ads. While the attack code alters the tone or color of the images, the changes are almost invisible to the untrained eye.
The malicious script is concealed in the alpha channel that defines the transparency of pixels, making it extremely difficult for even sharp-eyed ad networks to detect. After verifying that the targeted browser isn’t running in a virtual machine or connected to other types of security software often used to detect attacks, the script redirects the browser to a site that hosts three exploits for now-patched Adobe Flash vulnerabilities.
«
Flash plus ad networks: it’s a recipe for disaster. (Thanks @papanic for the link.)
link to this extract
Errata, corrigenda and ai no corrida: none notified